
Enable employees to work remotely and stay more secure
Help your employees who work from home remain productive and secure using Microsoft solutions.

Get single sign-on and multifactor authentication with Microsoft Entra ID
Enable secure remote work by connecting all your cloud apps. Use unlimited single sign-on (SSO) and multifactor authentication (MFA) at no extra cost with Microsoft Entra ID.
Connect to your apps
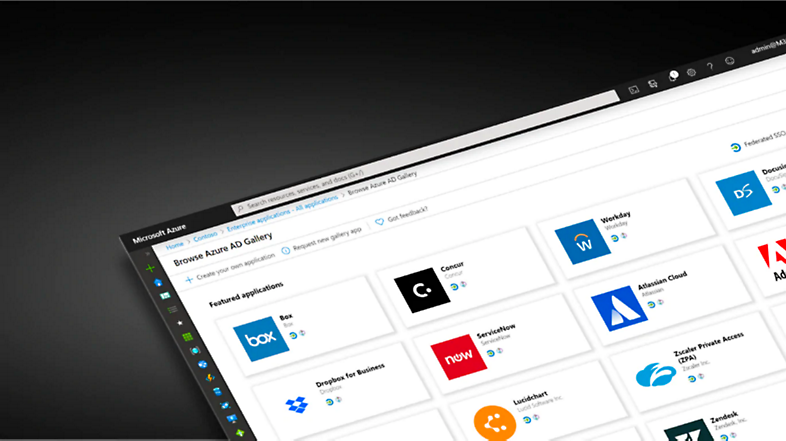
Set up remote access to apps
Establishing identity management in the cloud is your first step. Microsoft Entra ID lets you manage authentication across devices, cloud apps, and on-premises apps. With single sign-on, your employees can access resources from any device while working remotely.

Enable remote access to on-premises web apps
Your business-critical apps may not be set up for access from outside the corporate network. Use Microsoft Entra ID application proxy, a lightweight agent, to enable access to your on-premises apps without opening up broad access to your network. Combine it with existing Microsoft Entra authentication and Microsoft Entra conditional access policies to help keep users and data secured.

Collaborate with contractors and partners
Partnering with other organizations becomes more challenging without in-person meetings. Create and maintain relationships no matter where you are by removing barriers to remote interaction. Grant access to the right apps with a single sign-on experience. Ensure appropriate access to your organization’s resources anytime, anywhere, by applying a greater level of security and governance for partners.

Protect access from anywhere
Multifactor authentication (MFA) is the single best thing you can do to improve security for remote work. If you’re not able to distribute hardware security devices, use biometrics or mobile device authentication apps, such as Microsoft Authenticator, as the second factor.
Extend protection to devices
Many organizations are increasing the use of personal devices to enable remote work. Microsoft Entra conditional access policies and Microsoft Intune app protection policies help manage and secure corporate data in approved apps on personal devices.

Manage devices from the cloud
Microsoft Intune lets you manage both company-owned and employee-owned devices from the cloud. It allows you to manage across devices (laptop, tablet, and mobile device) and operating systems (iOS, Windows, and Android). Set up your Intune subscription then add users and groups of users, assign licenses, deploy and protect apps, and set up device enrollment.

Create conditional access policies
Create conditional access policies according to user, device, application, and risk. Enforce controls that allow a device to access a specific resource only if it’s compliant.
Strengthen Protection against threats

Help protect against phishing
Phishing is a primary point of entry for attackers, and recent world events have provided them with a new opportunity to trick users into clicking on lures. Set up antiphishing protections with Microsoft Defender for Office 365 to increase security against malicious emails and help protect your employees from increasingly sophisticated attacks.

Protect endpoints
The Microsoft Defender for Endpoint integrated suite of pre- and post-breach protection capabilities helps your security team protect your environment and scale and operate efficiently while being remote. Take advantage of threat and vulnerability management, attack surface reduction, and auto investigation and remediation today. These features require relatively low effort to leverage and can have the greatest impact in helping to drive better security and improved efficiencies.
Protect and govern your remote work

Control and manage use of cloud apps and resources
Remote workers often need access to a variety of business-critical cloud apps to do their jobs. Use Microsoft Defender for Cloud Apps to monitor session risk, gain visibility into usage, and enforce app and file usage policies in real time. Maintain productivity by educating and guiding workers to access the cloud resources they need through more secure methods.

Strengthen your security posture using intelligent insights and guidance
Once you’ve deployed your security infrastructure, ensure you’re taking full advantage of its capabilities with an optimized configuration. Identify potential posture improvements and develop and implement a plan to get the most security out of your Microsoft 365 and Azure workloads with Microsoft Secure Score.
More on securing remote work
Enable secure, remote access for your work
Now, more than ever, remote work capabilities are vital. Ensure your workforce is as efficient working from home as they were at the office. In this webinar you’ll learn how Microsoft Entra ID helps improve efficiency while maintaining the right balance of productivity and security for remote workers.

Security Controls for Remote Work webinar
With the increase in remote work, legacy network architectures are suddenly under enormous strain. Many organizations are now rethinking their network infrastructure design, especially for apps such as Office apps and Microsoft Teams. In this webinar, we provide guidance on how to manage security in the changing environment.

Why multifactor authentication is a priority
Dealing with passwords is challenging for many companies. Breaches happen if passwords aren’t augmented or replaced with stronger authentication methods that are easily adopted by users. Learn why passwords don’t protect you from most attacks (but MFA does) and how to find the right options for your company and your users. We’ll also share how Microsoft can help you start eliminating passwords in your environment.
Additional security resources
Read blogs about securing remote work
Best practices and guidance for security professionals on how to enable your users to work remotely.
Get set up with Microsoft FastTrack
Microsoft FastTrack is now available to assist organizations setting up remote work.
View tasks to support remote work
The top 12 tasks for security teams to support people working remotely or from home.
Work securely from anywhere
Guidance to help ensure your employees are working securely when they are working remotely.

Follow Microsoft