This blog post is part of the Microsoft Intelligent Security Association (MISA) guest blog series. You can learn more about MISA here.
Cybercriminals have ramped up their initial compromises through phishing and pharming attacks using a variety of tools and tactics that, while numerous, are simple and often go undetected. One technique that attackers continue to leverage to obfuscate their activity and remain undetected is dwell time.
Dwell is the time between the initial compromise and the point when the attack campaign is identified. While industry reports offer differing averages for dwell time, I have yet to see reporting that presents an average below the 50 to 60-day range. Read more about advanced endpoint protection and dwell time.
Bolster Your Advanced Endpoint Protection (AEP)
Download the Digital Defense white paper here.
While dwell times have slightly decreased as attackers become less patient, they are still significant enough to evade the plethora of security tools that exist today. The challenge with these tools is their inability to piece together attacker activity over long periods. By the time enough indicators of compromise (IoC) reveal themselves to be detected, it is often too late to prevent a breach. Most monitoring solutions look for attacker activity to identify a potential indicator of compromise. However, the best way to combat dwell time is to identify and eradicate dormant or nascent malware that stays well-hidden before they periodically activate.
A layered solution
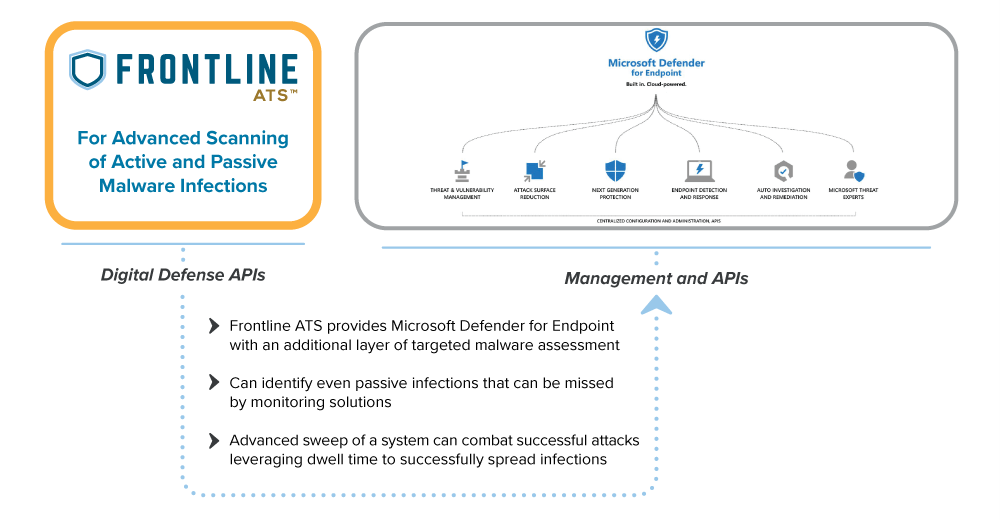
Frontline Active Threat Sweep™ (Frontline ATS™), integrated with Microsoft Defender for Endpoint, identifies malware designed to actively evade EDR solutions. Frontline ATS™ is part of the Digital Defense Frontline.Cloud platform providing on-demand agentless threat detection that proactively analyzes assets for indications of a malware infection before other agent-based security tools can be deployed. When integrated, Frontline ATS augments Defender for Endpoint’s capabilities by identifying hidden IoCs without adding agents.
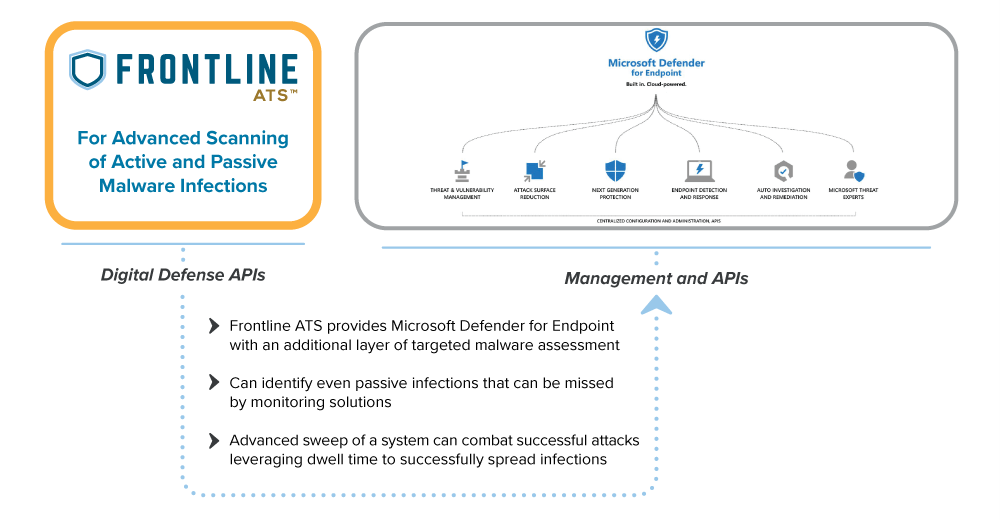
The ability to stay undetected for long periods of time is one of the most common and challenging tactics that attackers use to execute a successful breach. In addition, even when a security team using monitoring tools or an incident response (IR) service is able to detect a threat and clean up an infection, it is common to see it repeatedly resurface. This is because even though all active indicators of the threat have been investigated and addressed, if the initial, and often inactive, installation of malware is not discovered due to inactivity, it can later be re-activated to re-spark an infection. With Frontline ATS and Defender for Endpoint, security teams can find any source, artifact, or inactive remnants of malware that could restart the attack campaign. Defender for Endpoint and Frontline ATS provides comprehensive and unobtrusive advanced endpoint detection, protection, and response for drastically improving the security operations team’s effectiveness at preventing breaches.
To learn about the Digital Defense Frontline ATS integration with Microsoft Defender for Endpoint, please visit our listing in the Microsoft Azure Marketplace or visit Digital Defense to learn more.
To learn more about the Microsoft Intelligent Security Association (MISA), visit our website where you can learn about the MISA program, product integrations, and find MISA members. Visit the video playlist to learn about the strength of member integrations with Microsoft products.
For more information about Microsoft Security Solutions, visit the Microsoft Security website. Bookmark the Security blog to keep up with our expert coverage of security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.