The cybersecurity landscape has fundamentally changed, as evidenced by large-scale, complex attacks like Nobelium, Hafnium, and more recently last week’s Colonial Pipeline attack, which signals that human-operated ransomware is on the rise.
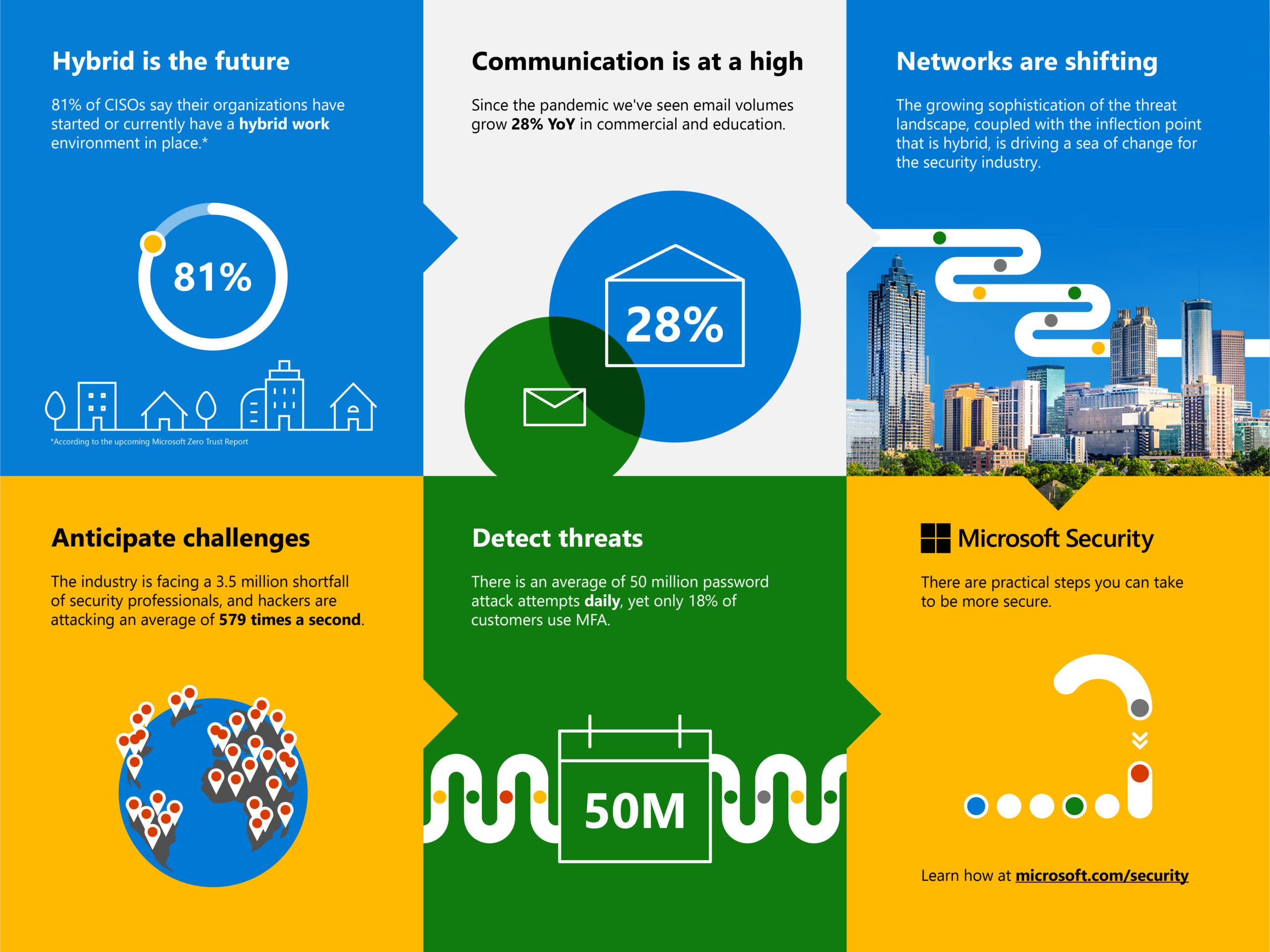
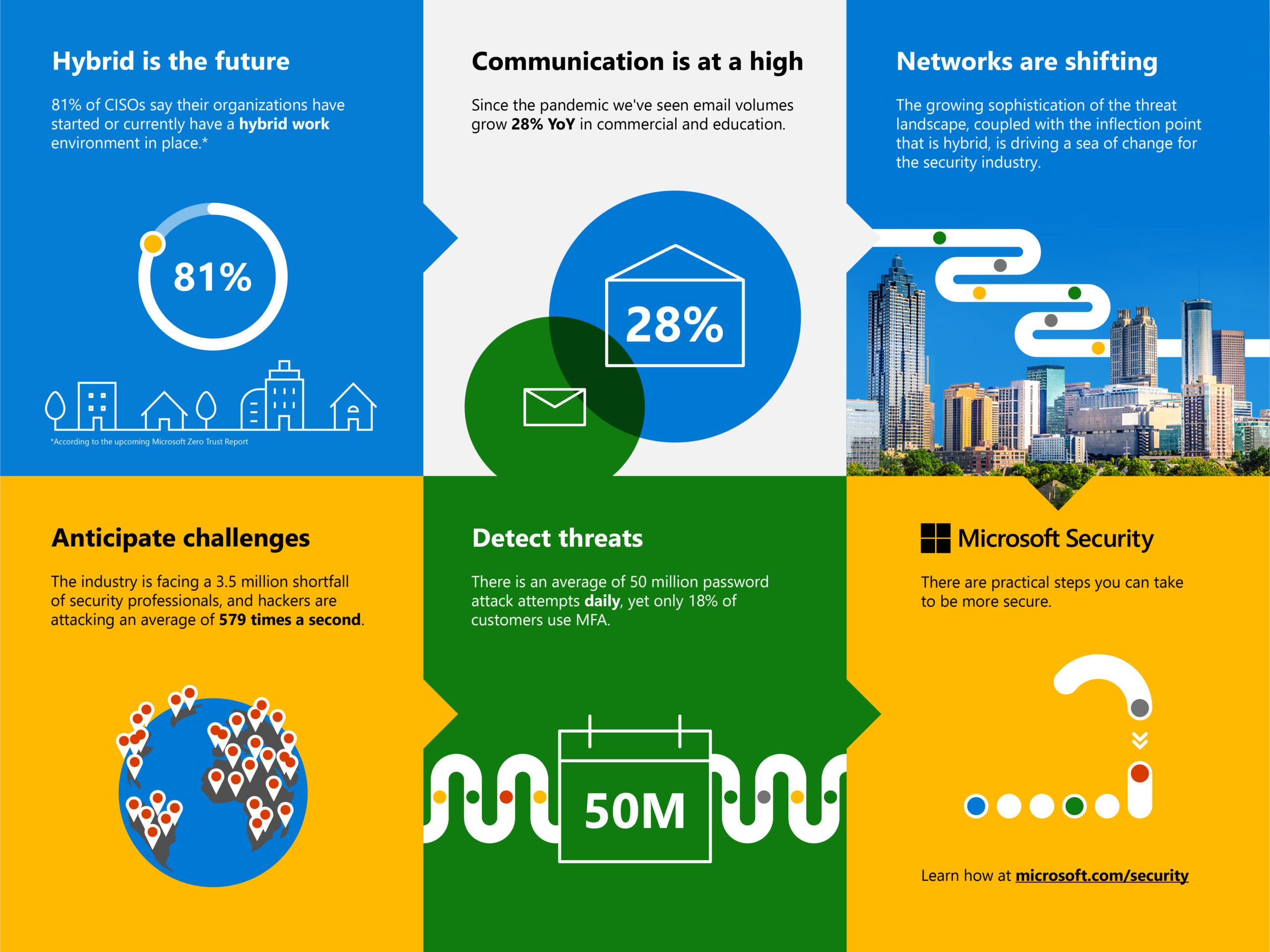
Hackers launch an average of 50 million password attacks every day—579 per second. Phishing attacks have increased. Firmware attacks are on the rise, and ransomware has become incredibly problematic. And while Microsoft intercepted and thwarted a record-breaking 30 billion email threats last year, our work is never done.
We are now actively tracking 40 plus active nation-state actors and over 140 threat groups representing 20 countries—that number used to be a handful.
We are also rapidly delivering innovation to meet the needs of a changing landscape and you can read more about our latest product updates for RSA in a blog I published today.
Security continues to be a number one priority for our customers, especially as many companies around the world are looking to transition from remote work to hybrid. To truly meet this challenge, defenders across the industry must come together for an end-to-end, Zero Trust security approach that covers the entire technology ecosystem. Because today, digital transformation cannot happen without security transformation.
The future of work is hybrid: Here’s what we can do
Even as many people start to transition back to the office, we expect a future where hybrid work is the norm. Forrester predicts that once people have settled into their new work patterns post-pandemic, we will still see a 300 percent increase in employees working remotely from pre-pandemic levels. According to our own Work Trend Index, The Next Great Disruption is Hybrid Work—Are We Ready?, 46 percent of people plan to move because they can now work remotely.
People are working on corporate networks and home networks and moving fluidly between business and personal activity online thanks to technologies intertwined with both aspects of our daily routines. The network is changing with employees’ home networks and devices are now part of the corporate network. What this means for organizations is that the network is suddenly without firm borders.
Our own approach
My friend and colleague Bret Arsenault, Microsoft’s Chief Information Security Officer, had the mammoth task of transitioning Microsoft and its 160,000 plus employees to remote work in March 2020 and has created our technology plan to transition to hybrid work.
Bret’s approach to solving this has been to foster a culture where security is everyone’s job. Just today, new guidance went out on a few areas:
- Keeping devices healthy and managed: All devices that need access to corporate resources must be managed to seamlessly keep your device secure and protected from phishing and malicious websites.
- Making security everyone’s job: We will offer new training, opportunities to provide feedback, and a new virtual security summit to ensure our employees are empowered and equipped to be more secure.
- Securing home offices: We will continue to build and offer resources and guidelines for employees that will work remotely either part or full time.
- Building for Zero Trust: We are asking our developers to build with a Zero Trust mentality.
While we have been remote, and as part of our Zero Trust approach, we have also been moving employees off the corporate network. An internet-first approach reduces exposure and gives employees a consistent experience whether they are at home or in the office.
We believe that security is a team sport and that when we share what we’re learning, we can all make the world a safer place. So we are sharing Bret’s guidance with our customers and partners. These specific steps will be the first of many in ensuring our hybrid workforce is as secure as possible.
There are other practical things that we will continue to focus on, and every business should consider as we move into hybrid work.
Identity is more important than ever: Use the tools you likely already have to protect it
Through NOBELIUM and other recent attacks, a clear theme has emerged—identity is the battleground for attacks of the future. We know weak passwords, password spraying, and phishing are the entry point for the vast majority of attacks. As our own CISO, Bret Arsenault, likes to say, “hackers don’t break in, they log in.”
In building a defense for our new threat landscape, the first thing every business should do is examine the tools they already have.
A great example of this is multifactor authentication (MFA). MFA is a defense that our customers have available to them, yet when looking at our own customer data, only 18 percent have it turned on. Any customer with a commercial service subscription—Azure or Microsoft 365—can turn on MFA at no additional cost.
We saw a significant jump in usage when the pandemic began. And when that happened, we saw a significant decrease in aggregate compromises—people thought they were activating to protect only remote access, but MFA protects the entire network.
We work with many kinds of organizations of all sizes—for some, implementing MFA is as easy as flipping the switch. But we understand and empathize that for others it’s much more complex. We’re actively working to make MFA rollout easier and more seamless for our customers, as well as ensuring that the end-user experience is as frictionless and friendly as possible. We are dedicated to working alongside our customers to make everyone more secure. We’ve introduced a number of programs to drive MFA adoption—from the introduction of security defaults to giving customers an entire toolset for internal communications.
Embrace a Zero Trust mindset
In a world where identity is the new battleground, adopting a Zero Trust strategy is no longer an option, it’s a new business imperative. People and organizations need to have trust in the technologies that bring them together. The term Zero Trust may feel like the opposite of that, but when you assume breach and provide the least privileged access necessary, it actually empowers employees with the flexibility and freedom they want.
The hybrid world is largely perimeterless, so wrapping protections around identity and devices is critical. As part of Zero Trust, we also think the future is passwordless and we will start to see that transition this year.
In fact, to help our customers on their Zero Trust journey we are excited to roll out a new Zero Trust assessment tool today that can help companies understand where they are currently and where they need to go.
For a deeper look at the imperatives around Zero Trust and how Microsoft is reimagining the concept of identity for a perimeterless world, read Joy Chik’s blog, 5 identity priorities for 2021—strengthening security for the hybrid work era and beyond, from Microsoft Ignite.
Take advantage of more robust security in the cloud
The benefits of the cloud for a remote or hybrid workforce are plentiful. Business-critical information can be accessed over the network, making it easy to have workers in any location.
Over the next 6 to 12 months, we will see rapid migration to the cloud, as companies recover from 2020 and implement new infrastructure. In a recent survey of our Microsoft Intelligent Security Association (MISA) partners, 90 percent reported that customers have accelerated their move to the cloud due to the pandemic.
Having a strong cloud posture also provides a level of security that most companies just couldn’t achieve on their own. And we learned from NOBELIUM that the vast majority of attacks originated on-premises, while attacks via the cloud were largely unsuccessful.
Invest in people and skills—and focus on diversity
We know that attackers exploit not just our digital holes, but the holes in our defender teams. Right now, we have two big problems: a shortage of cybersecurity professionals and a lack of diversity within teams. In the coming year, attackers will find these gaps and take advantage.
There is an estimated shortfall of 3.5 million security professionals this year—91 percent of our MISA partners report more demand than supply for cybersecurity professionals. This shortage can mean not only unfilled positions but also too much work on the shoulders of existing teams.
How do we solve this? We build the workforce of the future. We teach, train, and arm new defenders. After all, anyone can be a superhero of cybersecurity. It just takes passion and purpose—and some skilling.
I firmly believe anyone can be a defender, and with the proper training programs, we can all work together to build a cybersecurity workforce that reflects our planet. We must build diverse teams that reflect the many viewpoints of people globally, including the same demographics as the attackers themselves, to meet the security and privacy challenges of our time.
That’s why we’re pleased to offer new skilling programs and certifications across security, compliance, and identity. There are programs available for all levels of expertise, no matter where a defender is on their journey.
Fortunately, in a future where remote work is more common, the world is our oyster in terms of cultivating new and diverse talent. No longer constrained by physical office locations, it’s an exciting time to find the next generation of defenders and help them develop.
What’s next
We’re emerging from a year that has altered the world forever. It changed the way we live and work, brought new challenges in cybersecurity, and reminded all of us that there is no playbook for change.
But where there’s uncertainty, there is also the power to shape the world in positive and profound ways. At the heart of security and privacy protection is the freedom to imagine, plan, empower, and inspire.
As security professionals, it is within our superpowers to help people and organizations feel safe and be safe—to help them persist in the face of adversity with optimism, empathy, and peace of mind.
Learn more
Learn more about Microsoft’s approach to securing hybrid work, including context from our CISO Bret Arsenault, as well as a link to his new podcast Security Unlocked.
You can also assess your Zero Trust maturity stage to determine where your organization is and how to move to the next stage.
To learn more about Microsoft security solutions and how to optimize your Zero Trust strategy, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.