
Microsoft Canada launches Azure Landing Zone for Canada’s Public Sector
Microsoft Canada has launched its open-sourced Azure Landing Zone for Canada’s public sector. This is a purpose-built reference implementation to guide government departments to be compliant with Canadian standards.
Security and compliance are top priorities for governments around the world. The Government of Canada has adopted a Cloud-First strategy, and has defined a security and compliance standard that departments must adhere to for hosting Protected B data and applications in the public cloud (Canada’s Protected B / Medium Integrity / Medium Availability (PBMM) Security Control Profile).
To be compliant, each department is required to implement the required foundation and controls within their public cloud tenant, as well as provide attestation (through the SA&A process) to achieve an Authority to Operate (ATO). Furthermore, government departments are also responsible for continuously auditing their cloud environment to ensure continuous compliance and monitor drift.
Government organizations need to adopt modern cloud tooling and capabilities to achieve the required posture efficiently and, more importantly, in a continuous and sustainable manner.
To support Canadian public sector and government organizations to achieve this, the Microsoft Canada team has worked on a purpose-built Azure reference implementation for Canadian public sector departments. This reference implementation provides a core set of capabilities out of the box to help departments achieve their PBMM compliance and Authority to Operate approval faster. It also enables continuous monitoring and auditing of their environment. This reference implementation has been used with multiple departments already and has been open sourced to allow for ease of adoption and compliance acceleration.
Here are some of the capabilities and possibilities inherent in this reference implementation:
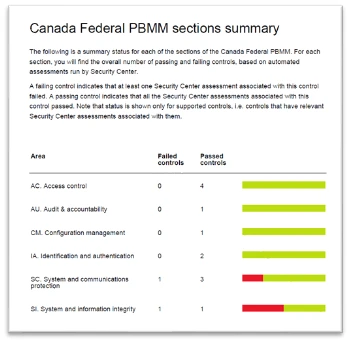
- Just-in-time, and continuous, audit: leveraging Azure’s governance capabilities through Azure Policy, the organization can take a snap shot audit of the environment (all the way down to the resource/machine/service level) from the lens of a number of built-in policies such as ITSG-33 regulatory compliance by using NIST SP 800-53 Rev. 4 and Canada Federal PBMM. This audit report can be accessed, and exported, on-demand from the Azure Portal directly (see sample screenshot). Alerts can also be set up for critical issues.
- Central logging, monitoring, and SIEM: through Azure Monitor, Microsoft Sentinel and other solutions, the reference implementation provides the full set of capabilities to enable CloudOps and SecOps.
- DevOps and DevSecOps: the structure of reference implementation allows for completely segregated environments (subscriptions) to reside within the Azure Landing Zone to enable development agility and velocity while maintaining compliance, as well as the ability for integration to promote applications between environments/subscriptions in a true continuous delivery model. This, combined with the security and policy capabilities, provides the recipe to adopt DevSecOps practices.
- Modular support for Archetypes: The reference implementation provides a hub and spoke model where different archetypes (at the spokes) can be established to support applications and workloads while inheriting all the controls and governance from the management hub. Archetypes are solutions comprised of multiple services and components to deliver a capability. An example of that would be providing a full Machine Learning (ML) environment that enables ML models as well as data pipelines, storage, and governance as needed. This also allows for extensibility in the future. Currently, we have the following archetypes already established:
- Machine Learning (supporting any ML-based use cases)
- Healthcare (specific controls for Canadian healthcare workloads)
- Generic Subscription (used for any workloads)
Get Started! Enable your department’s journey to a compliant cloud implementation more quickly by:
- Reviewing the reference implementation architecture design document
- Using the onboarding guide for Azure DevOps to test drive the automation
- Deploying the reference implementation to your environment: https://github.com/Azure/CanadaPubSecALZ/
- Reaching out to your Microsoft representatives for additional support




