Publishing CBL-Mariner CVEs on the Security Update Guide CVRF API
Microsoft is pleased to announce that beginning January 11, 2023, we will publish CBL-Mariner CVEs in the Security Update Guide (SUG) Common Vulnerability Reporting Framework (CVRF) API. CBL-Mariner is a Linux distribution built by Microsoft to power Azure’s cloud and edge products and services and is currently in preview as an AKS Container Host. Sharing CVEs regarding vulnerabilities that have been addressed CBL-Mariner upstream open-source projects will help security teams find the most up to date information to discover, assess, and patch systems quickly and consistently across cloud and edge scenarios.
The addition of CBL-Mariner CVEs to the CVRF API represents a sizable increase in monthly volume of published CVEs. For customers ingesting CVEs through the API who do not wish to receive CBL-Mariner related CVEs, we recommend you create an automation to filter out CBL-Mariner-related CVEs. You can identify Mariner CVEs by checking if the CVE contains a tag with value “Managed by Mariner”.
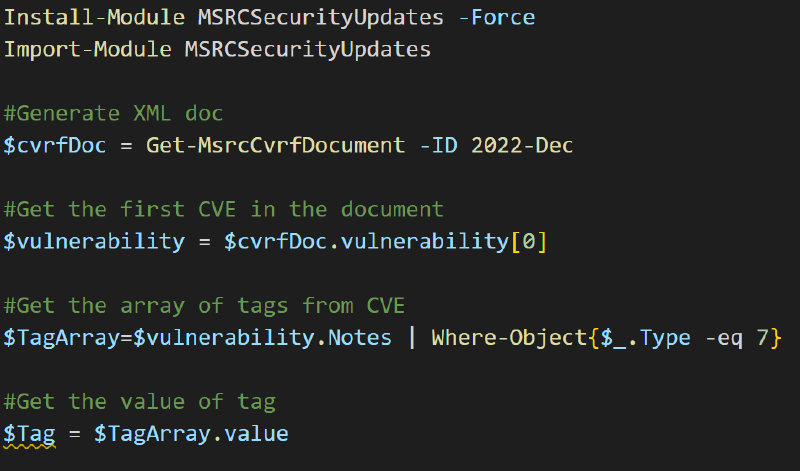
Here is a link to example PowerShell scripts for help navigating data on the CVRF API. The snippet below (not shown on the GitHub page linked) demonstrates how to use a PowerShell script to find the tag of the first CVE (unspecified) in a monthly release:
CBL-Mariner is built from a number of upstream open-source projects, so the majority of CBL-Mariner CVEs are authored and published by other organizations, also known as CVE Numbering Authority (CNA). The CVRF API will include the owning CNA as part of the CVE record, referenced by Type=8. Security researchers are encouraged to work directly with the respective upstream open-source projects to report issues or findings.
As we continue to improve the features and data available in the SUG we remain focused on providing our customers with the best experience possible. If you have any questions or suggestions for additional improvements, please feel free to contact us at MSRC Support Form.
Lisa Olson and Japhet Debrah
Microsoft Security Response Center
