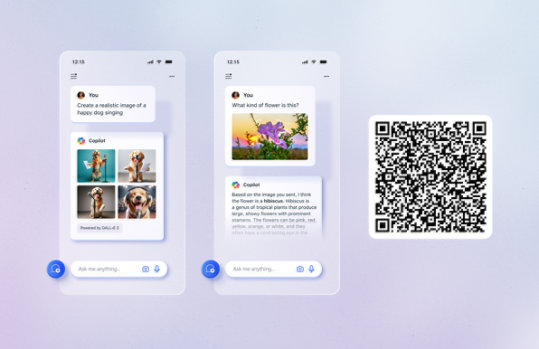
Unlock your potential with Microsoft Copilot
Get things done faster and unleash your creativity with the power of AI anywhere you go.
Local Administrator Password Solution (LAPS)
The "Local Administrator Password Solution" (LAPS) provides management of local account passwords of domain joined computers. Passwords are stored in Active Directory (AD) and protected by ACL, so only eligible users can read it or request its reset.
Important! Selecting a language below will dynamically change the complete page content to that language.
Version:
6.2
Date Published:
5/18/2021
File Name:
LAPS_Datasheet.docx
LAPS_TechnicalSpecification.docx
LAPS.ARM64.msi
LAPS.x64.msi
LAPS.x86.msi
LAPS_OperationsGuide.docx
File Size:
102.0 KB
71.0 KB
1.1 MB
1.1 MB
1.0 MB
626.3 KB
Important Deprecation Notice
NOTE: The legacy Microsoft LAPS product is deprecated as of Windows 11 23 H2 and later. Installation of the legacy Microsoft LAPS MSI package is blocked on newer OS versions. Microsoft will no longer consider code changes for the legacy Microsoft LAPS product.
Please use Windows LAPS, available on Windows Server 2019 and above, and on supported Windows 10 and Windows 11 clients, for managing local administrator account passwords. See https://aka.ms/laps for more information on Windows LAPS.
Microsoft will continue to support the legacy Microsoft LAPS product on older versions of Windows (prior to Windows 11 23 H2) on which it was previously supported. That support will end upon the normal End of Support for those OSes.
See https://aka.ms/LegacyLAPSDeprecation for more information.
End Deprecation Notice
Note: the only change in this release is that the binaries and installer package have been recompiled and signed with SHA256. No functionality has been added or modified.
For environments in which users are required to log on to computers without domain credentials, password management can become a complex issue. Such environments greatly increase the risk of a Pass-the-Hash (PtH) credential replay attack. The Local Administrator Password Solution (LAPS) provides a solution to this issue of using a common local account with an identical password on every computer in a domain. LAPS resolves this issue by setting a different, random password for the common local administrator account on every computer in the domain. Domain administrators using the solution can determine which users, such as helpdesk administrators, are authorized to read passwords.
LAPS simplifies password management while helping customers implement recommended defenses against cyberattacks. In particular, the solution mitigates the risk of lateral escalation that results when customers use the same administrative local account and password combination on their computers. LAPS stores the password for each computer’s local administrator account in Active Directory, secured in a confidential attribute in the computer’s corresponding Active Directory object. The computer is allowed to update its own password data in Active Directory, and domain administrators can grant read access to authorized users or groups, such as workstation helpdesk administrators.
Use LAPS to automatically manage local administrator passwords on domain joined computers so that passwords are unique on each managed computer, randomly generated, and securely stored in Active Directory infrastructure. The solution is built on Active Directory infrastructure and does not require other supporting technologies. LAPS uses a Group Policy client-side extension (CSE) that you install on managed computers to perform all management tasks. The solution’s management tools provide easy configuration and administration.
How does LAPS work?
The core of the LAPS solution is a GPO client-side extension (CSE) that performs the following tasks and can enforce the following actions during a GPO update:
• Checks whether the password of the local Administrator account has expired.
• Generates a new password when the old password is either expired or is required to be changed prior to expiration.
• Validates the new password against the password policy.
• Reports the password to Active Directory, storing it with a confidential attribute with the computer account in Active Directory.
• Reports the next expiration time for the password to Active Directory, storing it with an attribute with the computer account in Active Directory.
• Changes the password of the Administrator account.
The password then can be read from Active Directory by users who are allowed to do so. Eligible users can request a password change for a computer.
What are the features of LAPS?
LAPS includes the following features:
• Security that provides the ability to:
• Randomly generate passwords that are automatically changed on managed machines.
• Effectively mitigate PtH attacks that rely on identical local account passwords.
• Enforced password protection during transport via encryption using the Kerberos version 5 protocol.
• Use access control lists (ACLs) to protect passwords in Active Directory and easily implement a detailed security model.
• Manageability that provides the ability to:
• Configure password parameters, including age, complexity, and length.
• Force password reset on a per-machine basis.
• Use a security model that is integrated with ACLs in Active Directory.
• Use any Active Directory management tool of choice; custom tools, such as Windows PowerShell, are provided.
• Protect against computer account deletion.
• Easily implement the solution with a minimal footprint.
Supported Operating Systems
Windows Server 2019, Windows Server 2008, Windows Server 2016, Windows 10, Windows Server 2012 R2, Windows Server 2003, Windows Server 2008 R2, Windows Server 2012, Windows 7, Windows 8, Windows Vista, Windows 8.1, Windows Server 2022
Active Directory: (requires AD schema extension)
• Windows 2003 SP1 or later.
Managed machines:
• Windows Server 2003 SP2 or later, or Windows Server 2003 x64 Edition SP2 or later.
Note: Itanium-based machines are not supported.
Management tools:
• .NET Framework 4.0
• PowerShell 2.0 or later- The following steps need to be performed to configure LAPS
• Installation of GP CSE (Group Policy Client Side Extension) via MSI installation
• On management computers
• On clients to be managed
• AD preparation
• schema extension
• Permission updates
• Group policy configuration
Further details can be found in the operations guide.
