Application modernization
Bring your existing apps and data into the cloud and meet evolving business needs more easily. Explore Power Platform tools and strategies that help align legacy systems with current business and technology standards.
Refine Results
Product
Topic
Publish date
-
Power Platform Developers tool – October update
We are delighted to share our October update for the Power Platform Developer tools. -
Power Platform

Forrester TEI highlights 3 benefits of Power Platform premium capabilities
Microsoft Power Platform recently commissioned a Forrester Total Economic Impact study to help customers better understand the value of Microsoft Power Platform premium capabilities. -
Power Apps

Microsoft and PMI announce certifications for university students to drive employability
Microsoft and the Project Management Institute (PMI) are partnering to announce the Microsoft Power Platform University Hub. -
Protecting data with Dataverse
Part 1: Security from External Threats In this blog series, we will be covering how to protect data in Dataverse from external and internal threats (both from internal users and Microsoft). -
Power Apps
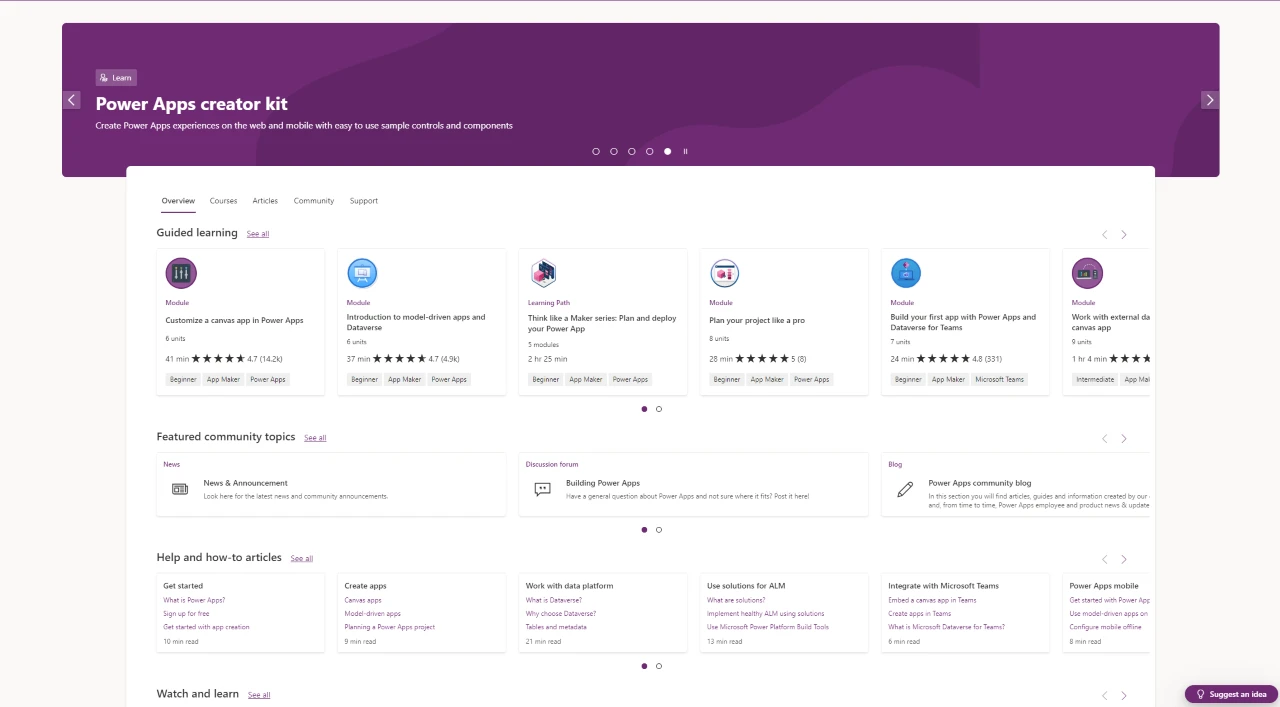
What’s new: Power Apps November 2022 Feature Update
Welcome to the Power Apps monthly feature update! We will use this blog to share a summary of product, community, and learning updates from throughout the month so you can access it in one easy place. -
Delegate the Mailbox Approval Process
I am excited to share that the mailbox approval process can now be delegated to another user instead of always requiring a Global or Exchange admin. -
Automate deployments with pipelines in Power Platform, now in preview
Pipelines within Power Platform aim to democratize application lifecycle management (ALM) for Power Platform and Dynamics 365 customers by bringing deployment automation capabilities into the product in a manner that’s more approachable for all makers, admins, and developers. -
Power Apps

Protecting Data with Dataverse Part 2: Security from Internal Threats (Users)
Protecting data from internal threats (users)