When cybercriminals breached the email network at H2-Pharma, an Alabama-based pharmaceutical company, nobody knew it had happened.
Most likely it was a phishing attack, an email scam that caught an employee off guard and tricked them into feeding their credentials into a malicious website designed to look legitimate, inadvertently handing a criminal the keys to their inbox.
H2 wasn’t flooded with spam or crippled by malware. But from that day on, bad actors were in the network, biding their time and monitoring email exchanges—particularly those of Josh B., Vice President of Commercial Operations, who oversaw H2’s relationships with vendors.
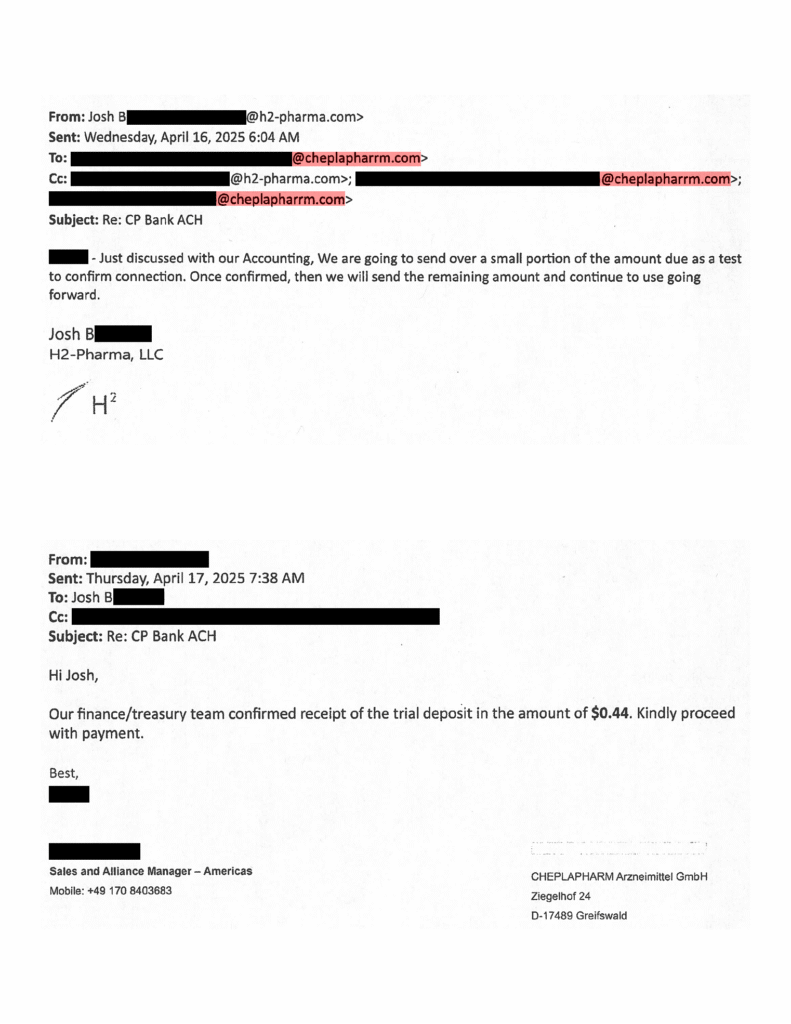
In April 2025, Josh B. reached out to Cheplapharm, a global pharmaceutical company headquartered in Germany that has been working with H2 for more than a decade. Josh B. was considering a change to H2’s payment processes, moving from wire transfers to ACH payments to save money on banking fees. He emailed a trusted contact at the company, a sales manager, to find out if the change was feasible.
Josh B. didn’t know it, but that was when the cybercriminals saw their opportunity.
The sales manager replied to Josh B.’s email, saying that Cheplapharm couldn’t accept ACH payments because it didn’t have a US bank account. But soon after, Josh B. got another email from his contact—same subject line, same email signature—saying that he’d checked with Cheplapharm’s finance and accounting teams and found that they could take ACH payments after all. The sales rep attached the details for a US-based account.
It wasn’t unusual for Cheplapharm to change course like this, so the request didn’t seem like a red flag to Josh B. Still, he was cautious—he transferred $0.44 to the account to make sure payments were routed properly. The sales manager confirmed receipt of the transfer. Josh B., reassured, made another transfer, this time for several million dollars. A few weeks later, he made another seven-figure payment to the account.
The problem was, Josh B. wasn’t communicating with a real sales manager at Cheplapharm. He was emailing the cybercriminals who’d been watching his communications, waiting for just this moment.
On May 20, Josh B. got another email from his sales contact—this time inquiring why Cheplapharm hadn’t received payment from H2. Josh B. pointed to the ACH transfers, but the real sales manager knew nothing about those payments, and by that time the imposter was long gone. The bank account where Josh B. sent the payments had been shut down. H2 was out more than $7.3 million—money it needed to pay Cheplapharm in order to provide medications its customers depend on.
The infrastructure that powers cybercrime
The type of attack that hit H2-Pharma is known as business email compromise (BEC), or payment diversion fraud, and it’s not an easy scam to pull off. It requires time, patience, and sophisticated social engineering. It also requires specialized technology. A BEC scam is a multi-stage attack, and each phase uses different tools and technical infrastructure.
The initial stage involves gaining access to an email account, often through phishing techniques. Other tactics may include scraping the web for vast lists of addresses to target, deploying mass-mailing tools to send out thousands of emails, and hosting legitimate-looking websites intended to harvest user credentials.
Fraudsters then use the stolen credentials to log into the victim’s account and search for supplier details, financial discussions, and pending invoices. They copy email signatures and monitor threads to find a moment when a bill needs to be paid, then slip into an ongoing conversation, impersonating the real vendor to convince the victim to route payment to a different account. Increasingly, they use AI voice cloning and face-swapping technology to manipulate victims.
After defrauding their target the attacker disappears, erasing their tracks before the victim realizes what has happened.
This type of fraud might be too technically demanding for the average cyber thief to manage on their own, but cybercrime today is a booming underground business with a wide range of “Cybercrime-as-a-Service” (CaaS) providers selling ready-made tools and services.
Until recently, criminals could subscribe to a service that provided the necessary tool to conduct attacks such as BEC for as little as $24 a month: a platform called RedVDS.
RedVDS provided cheap, disposable virtual computers (VDS stands for Virtual Dedicated Server) that were used as launchpads for a wide range of cyber-enabled financial fraud. RedVDS fueled a surge in worldwide fraud that has cost victims more than $66 million since 2019. These figures represent only confirmed cases—actual worldwide losses may be much higher.
Outsourcing cyberattacks to CaaS vendors like RedVDS not only makes it easier to launch sophisticated fraud schemes but also helps perpetrators evade detection. “Cybercriminals don’t want to use their own infrastructure,” says Donal Keating, Director of Innovation and Research at Microsoft. “Nobody uses their own car to rob a bank.”
RedVDS provided anonymity, taking payment in cryptocurrency and eliminating usage logs. Subscribers could log on remotely using a VPN to hide their real location while they gathered information over time. RedVDS was tailor-made for cybercrime, but it wasn’t malware; it was simply the infrastructure that facilitated cyberattacks. “This infrastructure layer is a critical enabler of modern cybercrime cases,” says Alexandra Gerst, Senior Corporate Counsel with Microsoft’s Digital Crimes Unit (DCU).
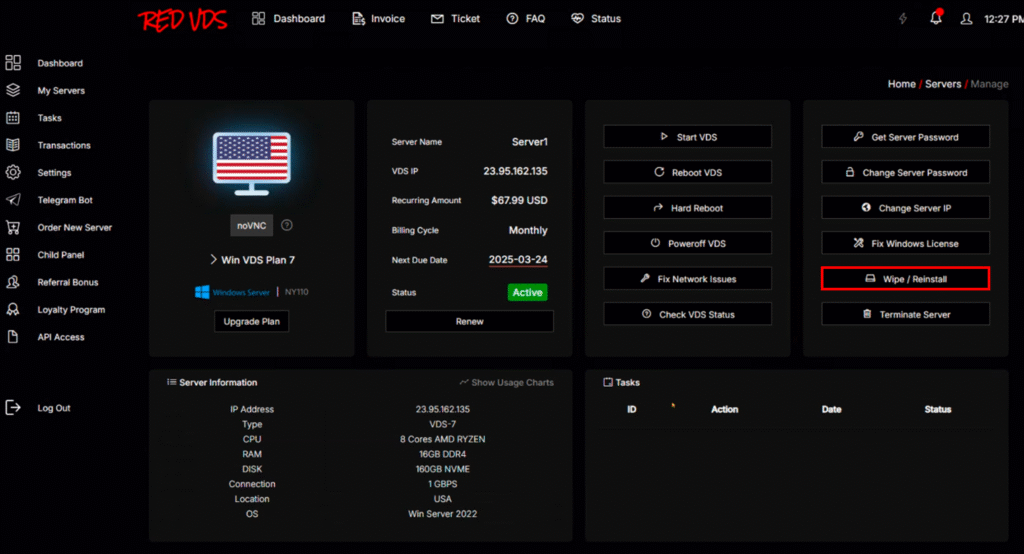
RedVDS also allowed criminals to wipe their server to remove evidence of wrongdoing. Deleted data can be recovered, but wiping a server overwrites the entire disk with a fresh operating system and a new IP address, leaving no trace of prior activity. RedVDS subscribers could wipe and reinstall their system in a matter of minutes.
The thread that unraveled the RedVDS enterprise
Microsoft tracks more than 100 trillion security signals daily to detect malicious activity, and the company’s threat analysts began to see a pattern: Thousands of attacks on customers worldwide were coming from different Windows hosts using the same computer ID. That ID mapped to a single Windows 2022 Eval installation, a “try before you buy” license that had been pirated. When the DCU’s investigators began to follow the stolen ID, they learned that users received receipts from RedVDS.
The operators behind RedVDS, a group Microsoft tracks as Storm-2470, were cloning the same Windows virtual machine over and over again without changing the system ID.
“At the end of the day, cybercriminals are just like the rest of us—they get a little bit lazy,” says Sean Ensz, Principal Investigator with the DCU. RedVDS facilitated scams that preyed on human error, yet in the end, it was the criminals’ own human error that led to the takedown of the enterprise.
How the DCU pulled the plug on RedVDS
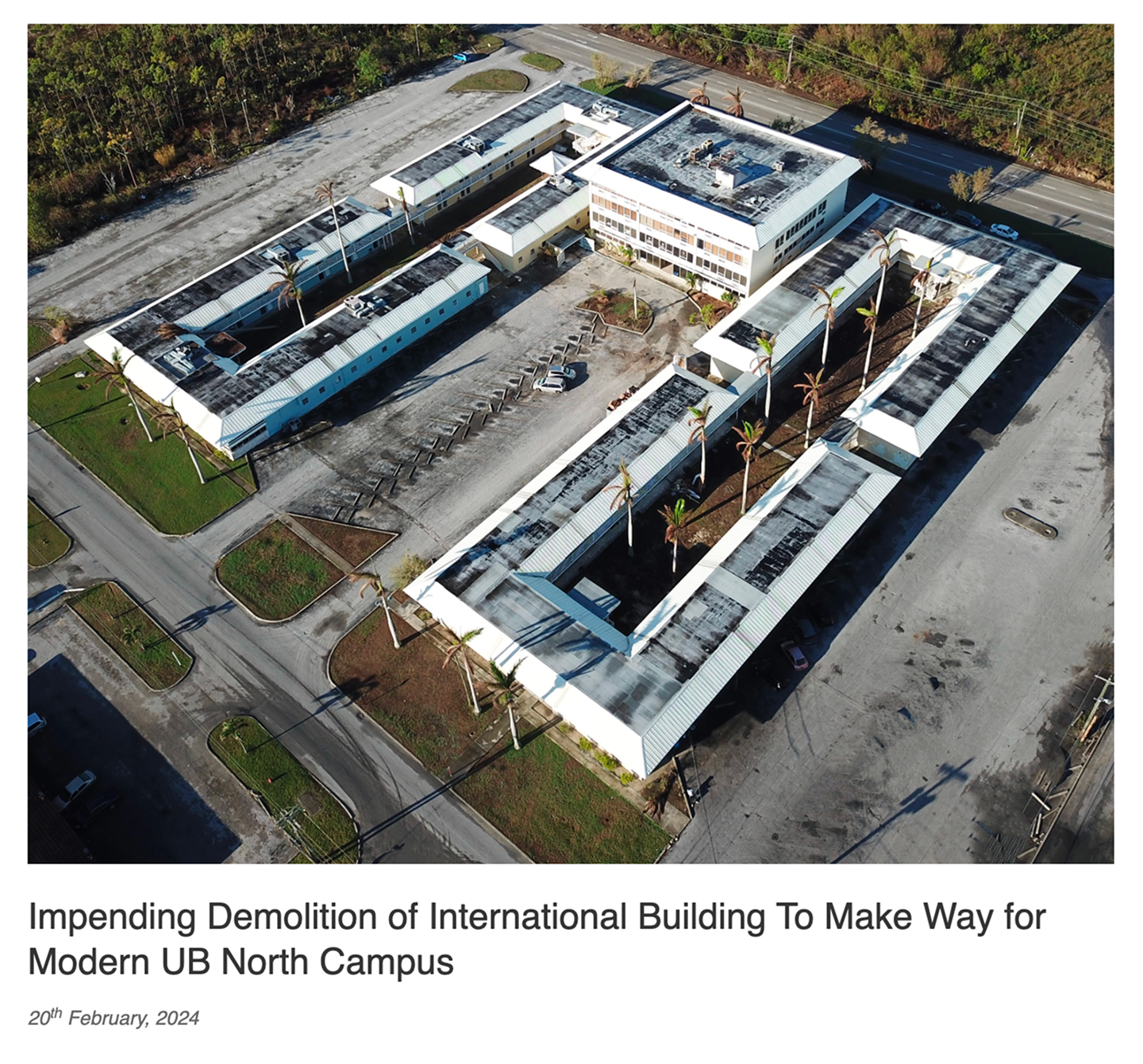
Investigators with the DCU went undercover as subscribers to RedVDS, learning how the platform worked and tracing cryptocurrency payments. They discovered that RedVDS was using a fictitious business entity that claimed to operate in the Bahamas, but the address of the business turned out to belong to a building at the University of the Bahamas that had been demolished in 2024.
Once they had traced the criminal activity to a specific group, the DCU knew exactly how to cut off RedVDS from victims, but it wasn’t what TV and movies might lead you to expect. There was no feverish hacking to neutralize the technology; no dramatic raid on an underground criminal lair. The DCU simply wields the power of the law.
The perpetrators were not only using Microsoft’s branding to defraud victims, they were violating the terms of service that governed the stolen Windows license. The misuse of Microsoft’s intellectual property provided legal grounds for the DCU to file a civil lawsuit, asking US courts for permission to seize the two domains RedVDS used to host its marketplace and customer portal. The case moved swiftly, and the DCU quickly took down redvds.com and redvds.pro, severing RedVDS from its cybercriminal customers.
The DCU also filed a civil lawsuit in the UK that helped obtain information about RedVDS’s operators and customers. The civil cases are part of a larger joint operation with international law enforcement. Germany’s Public Prosecutor’s Office Frankfurt am Main—Central Office for Combating Internet Crime (ZIT), together with the German State Criminal Police Office Brandenburg, has seized a key server associated with RedVDS, disrupting its central marketplace. Concurrently, and in line with ongoing efforts, Microsoft is collaborating with international law enforcement entities such as Europol’s European Cybercrime Centre (EC3) to dismantle the wider network of servers and payment systems that facilitated services for RedVDS customers.
Even after RedVDS was taken down, there were still virtual computers running the unauthorized Windows servers for cyberattacks. In response to such cases, the DCU has established the Statutory Automated Disruption (SAD) program, which enables the team to dismantle malicious infrastructure using both legal and technical measures. This program is powered by a semi-automated notification process that leverages local legal frameworks. Hosting providers are being alerted about illicit activity on their platforms and are asked to implement appropriate measures to stop any further harm.
In the first week after the DCU filed the civil case against RedVDS, the team was able to take down 95% of RedVDS virtual computers leveraging the SAD program. “That continuous automated pressure, paired with human oversight to route notices to the right hands, is what makes the disruption stick,” says Lakshmi Mucharla, Senior Data Analyst at the DCU. “Automated systems are designed to keep working as long as criminals keep trying to spin up the infrastructure.”
Don’t let it happen to you: How to identify—and avoid—business email compromise
However technologically sophisticated they might be, BEC attacks ultimately depend on social engineering. “The key component in this type of attack is the criminals’ ability to convince victims that they’re communicating with people they trust,” says Richard Boscovich, Assistant General Counsel in the DCU. This email, sent by a RedVDS user to Gatehouse Dock Condo Association (GDCA), which joined H2-Pharma as a co-plaintiff in the DCU’s US civil case, shows what to look out for.
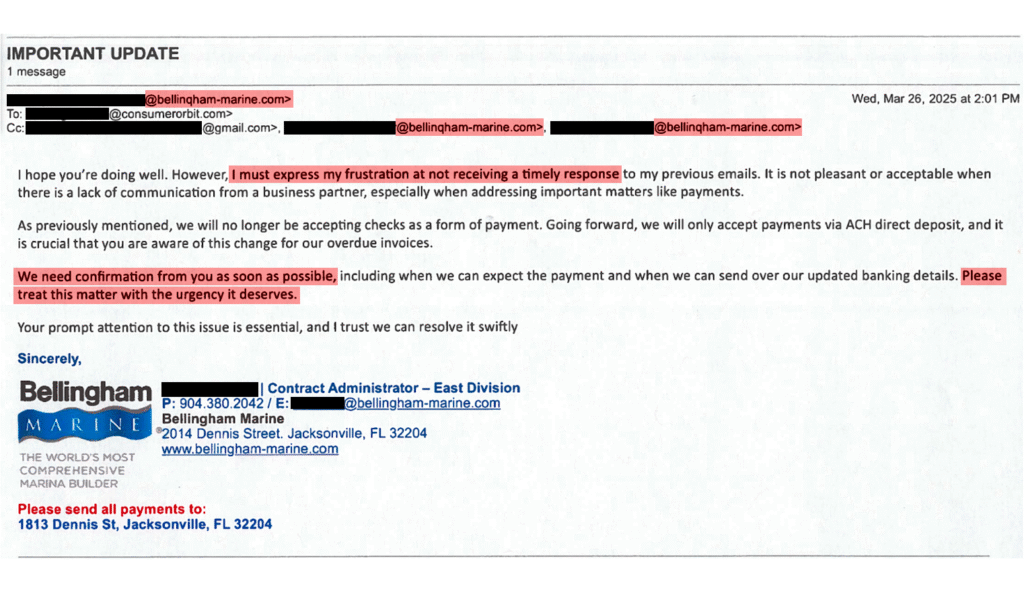
Urgency: Fraudsters demand payment quickly, threatening victims and using guilt to manipulate them into acting without full diligence. Slow down, read carefully, and check for telltale signs of fraud.
Homoglyph domains: A critical component of BEC attacks is registration of lookalike domains that are nearly indistinguishable from legitimate web addresses. The criminals who defrauded GDCA emailed from bellinqham-marine.com instead of bellingham-marine.com—nearly impossible to detect without close scrutiny. In the course of their investigation, the DCU uncovered over 7,300 IP addresses linked to RedVDS infrastructure that collectively hosted more than 3,700 homoglyph domains within a 30-day period.
Hiding behind pixels: Like most of us, victims at GDCA and H2-Pharma relied on digital communication—yet a simple in-person conversation would have exposed the attempted fraud. “If you’re dealing with payments, you need to be extra diligent in making sure that you’re interacting with the person you think you are,” says Jacklynne Sienicki, director of data analytics at the DCU. Pick up the phone and talk to a trusted contact, or better yet, meet them in person. Hundreds of RedVDS subscribers used deepfakes and AI voice cloning to fool victims, so don’t rely on a voicemail message or video call to confirm the authenticity of a request.
Exploiting security gaps: Always, always turn on multifactor authentication—it blocks 99% of phishing attempts. And stay on top of software updates. All legitimate technology providers embed security features into their products, but you won’t have up-to-date protection if you don’t install the latest updates.




