Featured
Recent posts
-

|
Deploying Microsoft Baseline Security Mode at Microsoft: Our virtuous learning cycle
The enterprise security frontier isn’t just evolving. It’s accelerating beyond the limits of traditional security models. AI acceleration, cloud adoption, and rapid growth of enterprise apps have dramatically expanded the attack surface. Every new app…
-

|
Responsible AI: Why it matters and how we’re infusing it into our internal AI projects at Microsoft
Like the computer itself and electricity before it, AI is a transformational technology. It’s providing never-before-seen opportunities to reimagine productivity, address major social challenges, and democratize access to technology and knowledge. Engage with our experts!…
-

|
Accelerating transformation: How we’re reshaping Microsoft with continuous improvement and AI
Technology companies are really people companies. In an age of rapidly advancing AI, losing sight of this reality leads to an overemphasis on new tools while neglecting opportunities for the transformational change that AI offers.…
-

|
Mapping the Microsoft approach to accessibility in the world of AI
More than 1 billion people worldwide have a disability, and 83 percent of people will experience a disability during their working age. As AI transforms how we build and experience technology, accessibility has to be…
-

|
Microsoft CISO advice: Read our four tips for securing your network
Geoff Belknap, CVP and operating CISO for Core and Enterprise, shares four key practices your business can use to be prepared for managing network security incidents. Learn from our experience Network isolation (Secure Future Initiative)…
-

|
Deploying the Employee Self‑Service Agent: Our blueprint for enterprise‑scale success
The case for AI in employee assistance The advent of generative AI tools and agents has been a game changer for the modern workplace at Microsoft. And one of the foremost examples of how we’re…
-

|
Microsoft CISO advice: Explore our four tips for securing your customer support ecosystem
Microsoft business operations teams know all too well that cyberattackers seek to exploit customer support pathways. Tools that can unlock customer accounts or aid in troubleshooting issues in complex environments are a rich target. “The…
-
|
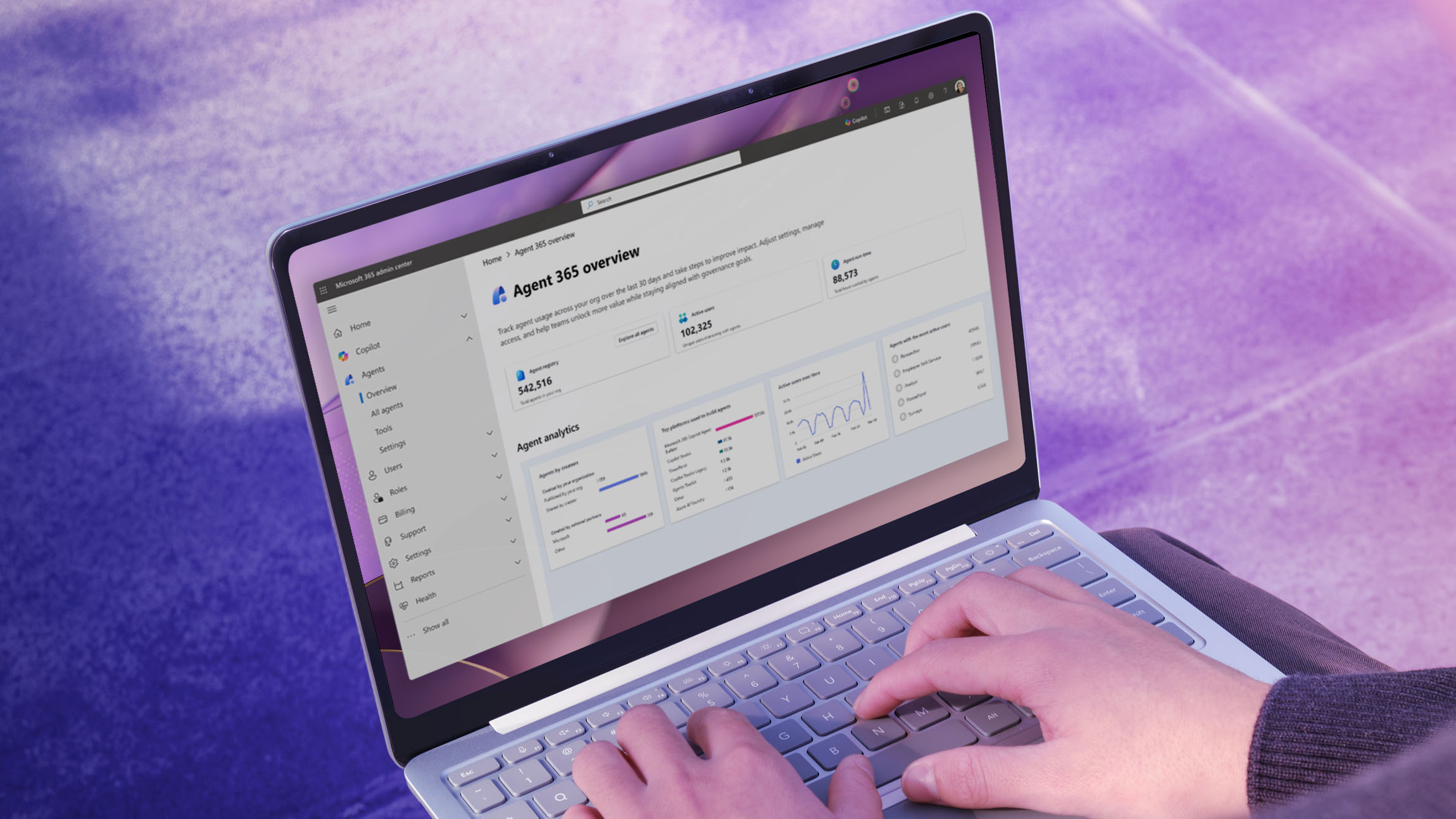
Shaping AI management at Microsoft with Agent 365 and Copilot controls
AI is moving fast at Microsoft. Every month, we’re discovering new ways that our employees are using Microsoft 365 Copilot and rapidly emerging agentic tools to work smarter, automate routine tasks, and unlock new patterns…
-

|
Powering the new age of AI-led engineering in IT at Microsoft
When generative AI burst into the mainstream, it landed in our IT engineering organization like a shockwave. There was excitement, curiosity, skepticism, and no shortage of questions about what this technology meant for the future…
-

|
The Frontier Firm: How knowledge workers are forging their own AI tools at Microsoft
Knowledge workers have all been there. Maybe you’re a product manager with a backlog that you can’t ever get to. Perhaps you’re a designer who can never seem to get engineering resources assigned to you.…
-

|
Getting started with Windows Hello for Business and Day 1 authentication at Microsoft
At Microsoft, we’re relentlessly focused on modernizing our passwordless protections in ways that strengthen our identity and security for everyone at the company. At an organization the size of ours—with a global workforce, massive cloud…
-

|
Protecting anonymity at scale: How we built cloud-first hidden membership groups at Microsoft
Some Microsoft employee groups can’t afford to be visible. For years, we supported email‑based communities internally here at Microsoft whose very existence depends on anonymity. These include employee resource groups, confidential project teams, and other…
Popular tags
Archives
- April 2026 (2)
- March 2026 (11)
- February 2026 (8)
- January 2026 (8)
- December 2025 (3)
- November 2025 (9)
- October 2025 (9)
- September 2025 (7)
- August 2025 (7)
- July 2025 (6)
- June 2025 (9)
- May 2025 (19)
- April 2025 (15)
- March 2025 (4)
- February 2025 (12)
- January 2025 (10)
- December 2024 (5)
- November 2024 (1)
- October 2024 (7)
- September 2024 (7)
- August 2024 (4)
- July 2024 (3)
- June 2024 (9)
- May 2024 (8)
- April 2024 (4)
- March 2024 (13)
- February 2024 (9)
- January 2024 (10)
- December 2023 (8)
- November 2023 (6)
- October 2023 (9)
- September 2023 (10)
- August 2023 (8)
- July 2023 (5)
- June 2023 (8)
- May 2023 (3)
- April 2023 (4)
- March 2023 (6)
- February 2023 (2)
- January 2023 (5)
- December 2022 (5)
- November 2022 (2)
- October 2022 (3)
- September 2022 (1)
- August 2022 (3)
- July 2022 (1)
- June 2022 (3)
- May 2022 (2)
- April 2022 (7)
- March 2022 (1)
- February 2022 (2)
- December 2021 (4)
- November 2021 (1)
- October 2021 (6)
- August 2021 (1)
- July 2021 (3)
- June 2021 (5)
- May 2021 (6)
- April 2021 (4)
- March 2021 (1)
- February 2021 (1)
- January 2021 (1)



