From transparency to action: What the latest Microsoft email security benchmark reveals
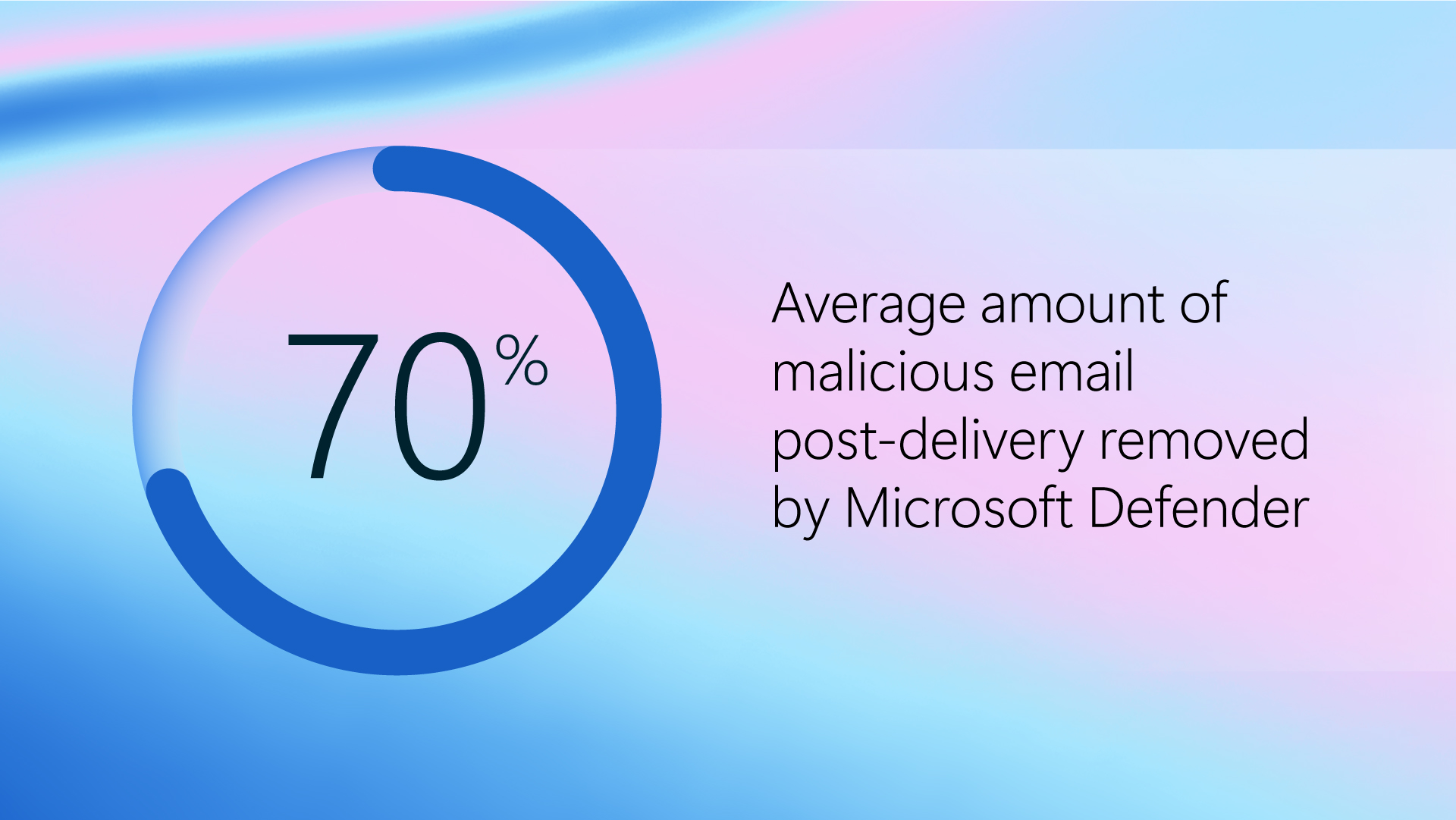
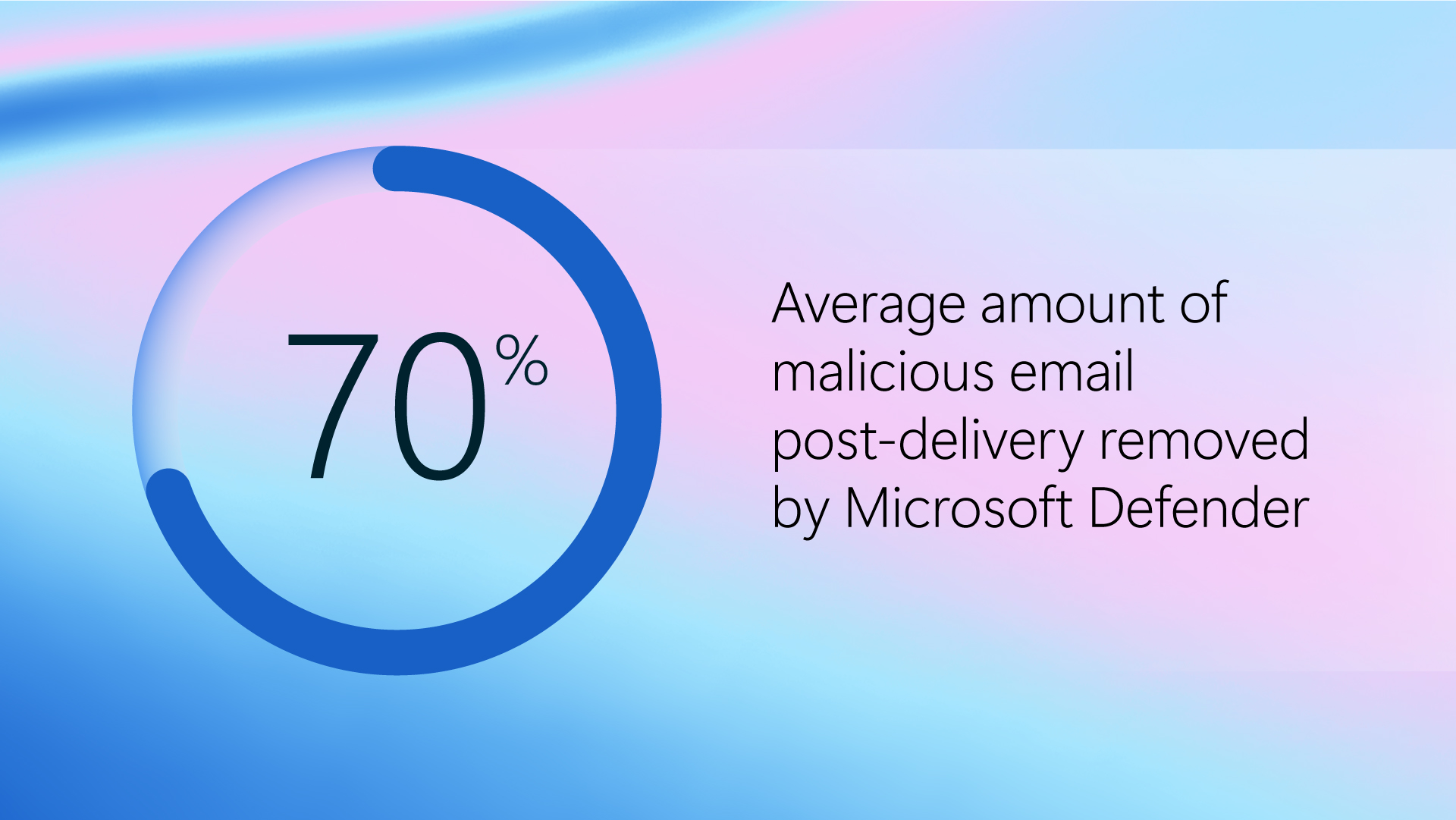
The latest Microsoft benchmarking data reveals how Microsoft Defender mitigates modern email threats compared to SEG and ICES vendors.
 Security
Security


Learn how to protect your emails from threats like phishing, malware, and business email compromise.