This post is authored by Andrew Marshall, Principal Security Program Manager, TwC Security, Yanbing Shi, Software Engineer, Internet Information Services Team, and Sourabh Shirhatti, Program Manager, Internet Information Services Team.
As a follow-up to our announcement regarding TLS 1.2 support at Microsoft, we are announcing new functionality in Windows Server 2012R2 and Windows Server 2016 to increase your awareness of clients connecting to your services with weak security protocols or cipher suites.
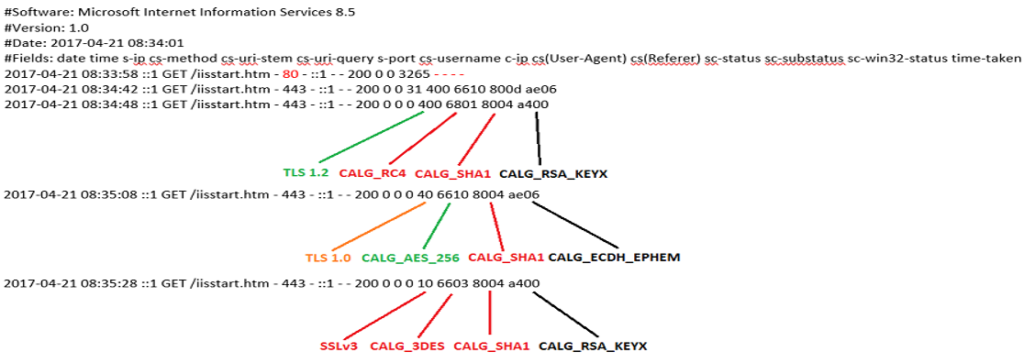
IIS logs can already be used to correlate client IP address, user agent string, and service URI. With the addition of the new custom logging fields detailed below, you will be able to quantify the usage of outdated security protocols and ciphers by clients connecting to your services.
To enable this new functionality, these four server variables need to be configured as the sources of the custom fields in IIS applicationHost.config. The custom logging can be configured on either server level or site level. Here is a sample site-level configuration:
Each SSL info field is a hexadecimal number that maps to either a secure protocol version or cipher suite algorithm.
For an HTTP plain-text request, all four fields will be logged as ‘-‘.
A sample log and explanation of the new fields follows:
For more information visit Official Microsoft Documentation for Custom Logging Fields in IIS.







