For the third year in a row, Microsoft successfully demonstrated industry-leading defense capabilities in the independent MITRE Engenuity ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge) Evaluations.
As the attack surface evolves on a near-daily basis, threat actors are creating more advanced techniques targeted across domains such as endpoints, identities, emails, documents, and cloud apps, requiring security solutions with the capability to automatically analyze threat data across these domains and build a complete picture of the attacks. The 2020 ATT&CK Evaluations concentrated on advanced threat actors known to the industry as FIN7 and Carbanak (also called Carbon Spider). This year’s rigorous evaluation included new benchmarks of detection and protection simulations of more than 174 steps across the attack chain, affecting both Windows client endpoints, servers, and, for the first time, Linux devices.
This cross-platform, sophisticated attack simulation significantly elevated the stakes for detection and protection, and we are proud to report that results showed Microsoft Defender for Endpoint effectively detected and prevented malicious activity at every major attack stage. In this evaluation, we were able to put Microsoft Defender for Endpoint’s Linux capabilities to the test. MITRE Engenuity ran the simulated Carbanak and FIN7 attack end-to-end and across multiple attack domains, meaning defenders benefited from the added capabilities in Microsoft 365 Defender and got visibility beyond just endpoint protection. MITRE Engenuity’s ATT&CK Evaluations results showed that Microsoft provides:
- Industry-leading protection: Microsoft’s industry-leading capabilities quickly identified suspicious activity and offered real-time containment to rapidly stop the attack.
- Superior detection and protection on Linux: Microsoft Defender for Endpoint blocked everything on Linux, providing exceptional detection, protection, and visibility that comprehensively captured Linux file server activity.
- Excellent detection and visibility across the attack chain: Our world-class SecOps experience and Microsoft 365 Defender capabilities showed the full attack story across domains and quickly correlated all activity down to two incidents.
Figure 1. MITRE Engenuity’s ATT&CK Evaluation results demonstrated that Microsoft provides industry-leading protection, superior detection and protection on Linux, and excellent detection and visibility across the attack chain.
Microsoft participated in the ATT&CK Evaluations because we believe it is the most comprehensive testing environment that most closely mirrors real-world attacks. Our mission is to empower world-class defenders by continuing to drive product excellence, listening to customers, and investing in research to deliver intelligent solutions. We attribute this success to these investments and our customer-first approach.
Microsoft Defender once again prevails over the adversary
Microsoft’s massive depth and breadth of security optics and threat intelligence is integrated into Microsoft Defender products and uniquely enables us to stand out in complex attack scenarios.
Industry-leading protection
Microsoft Defender for Endpoint blocked the attack at the earliest stage, providing containment in real-time. Defender for Endpoint quickly identified the suspicious activity and incriminated it as malicious. This prevented the attacker from taking actions that may have had a negative impact on the device, such as shell execution, discovery, persistence, or exfiltration, effectively blocking the simulation and stopping the attack from proceeding.
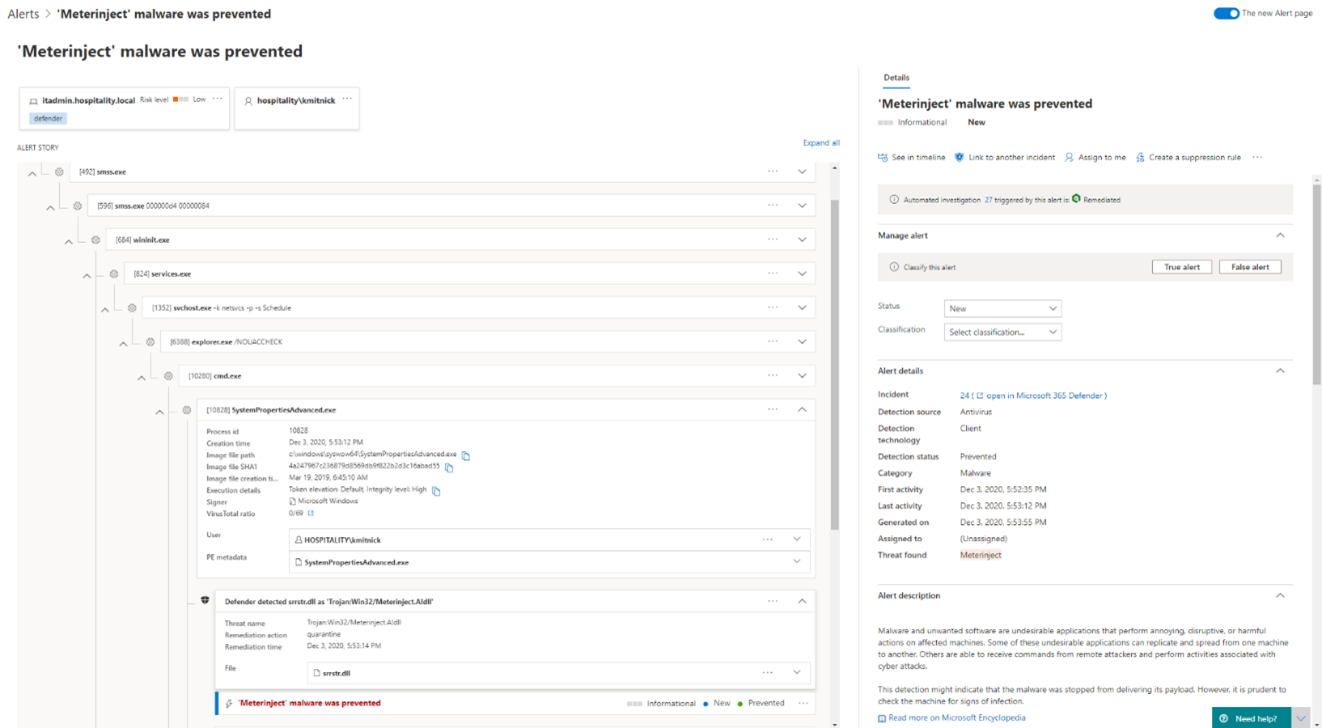
Figure 2. Defender for Endpoint alert page: SystemPropertiesAdvanced.exe attempts to execute code in the illegitimate srrstr.dll and is blocked by Defender for Endpoint.
Microsoft Defender for Endpoint provided extensive visibility and coverage for the attack chain on Linux.
Superior detection and protection on Linux
Our endpoint security capabilities for Linux fit seamlessly into the attack story, and Microsoft Defender for Endpoint was able to provide extensive visibility and coverage for the attack chain, which indicates how essential endpoint detection and response (EDR) detection, protection, and visibility are for navigating today’s Linux threat landscape. Defender for Endpoint was able to completely capture Linux file server activity, including sign-in, connections, read and copied files, various discovery activities, and Pass-the-Hash (PtH). We are proud to offer this kind of coverage on Linux as we continue to extend endpoint security capabilities across all the major platforms (Windows, Linux, macOS, Android, and iOS).
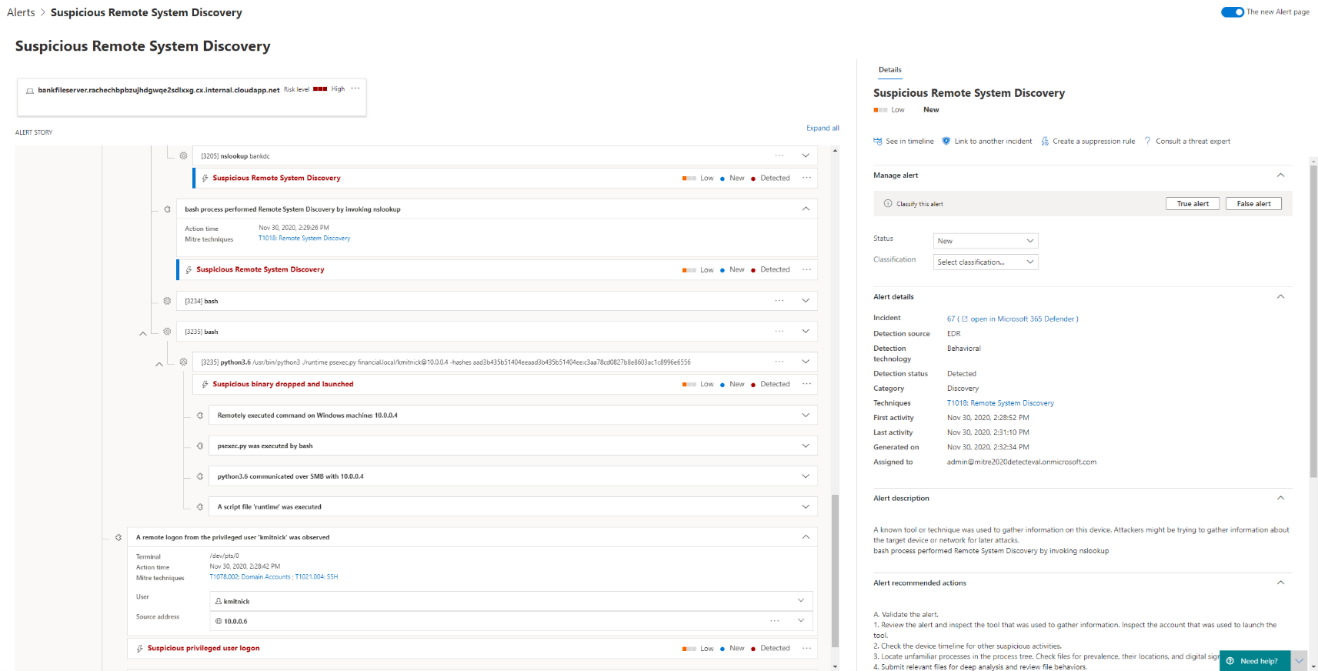
Figure 3. Defender for Endpoint alert page on a Linux device: Lateral movement attack story, from remote system discovery, suspicious login, and remote code execution using Python from Linux device to endpoint.
Microsoft 365 Defender dramatically reduced alert noise from over 1,000 alerts down to just two incidents.
Excellent detection and visibility across the attack chain
The results of the ATT&CK Evaluation highlighted our deep detection capabilities and the comprehensive optics across the attack chain, including:
- Detecting advanced attack techniques on endpoints: Microsoft Defender for Endpoint recorded and alerted on all malicious activities across the attack chain, including advanced attack techniques such as injections, shellcode execution, execution using scheduled tasks, UAC bypass, web browser and OS credentials collection, screen and keystroke collection, and persistence using application shimming.
- Providing deep visibility into the timeline of events on devices: Microsoft 365 Defender presented a detailed view of the events taking place on the device through the device timeline. The device timeline also provided a new capability to surface attack techniques: a specific sequence of standalone events is combined to build a more meaningful representation of identified attack technique. This recent addition to the device timeline empowers Security Operations Center (SOC) analysts to glean more insight into the activities on the device, as well as the potential reason for their execution.
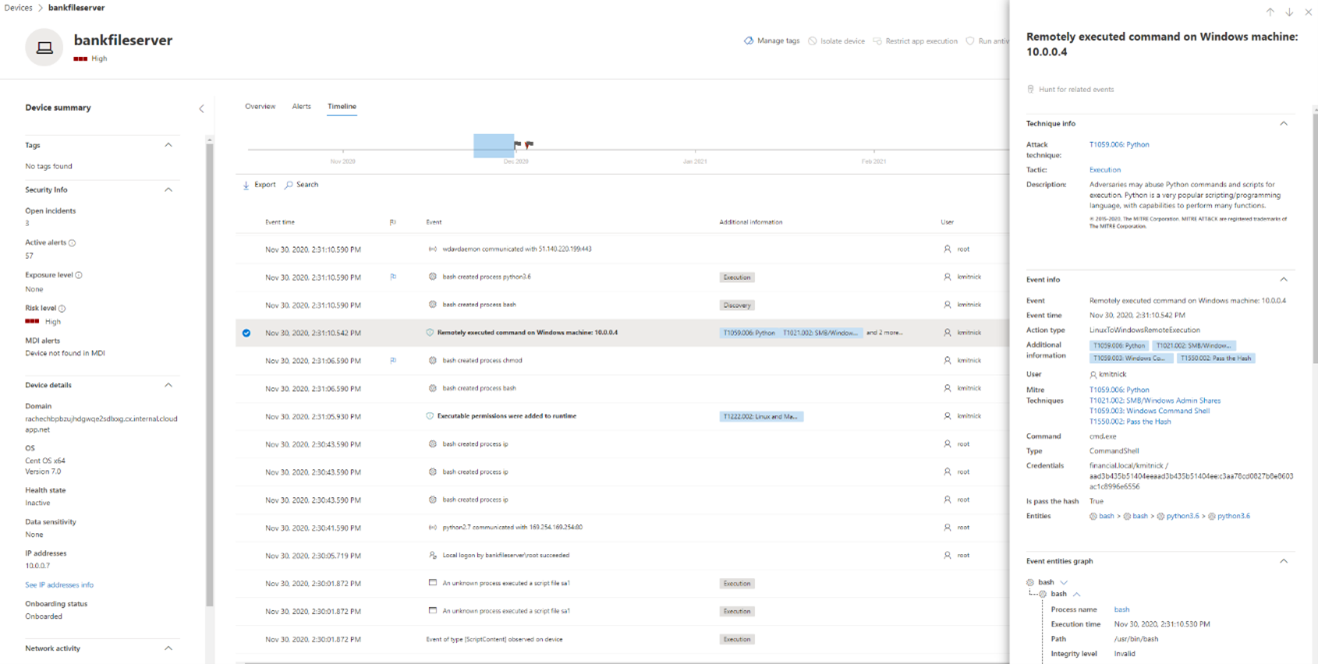
Figure 4. Defender for Endpoint device timeline on a Linux device: Lateral movement technique for remote code execution from Linux device to endpoint is highlighted.
- Identifying activities associated with compromised identities: Leveraging both device and identity signals, Microsoft 365 Defender provided deep visibility and alerting for actions taking place on a device by what’s known as a compromised account. Microsoft 365 Defender used sophisticated techniques, such as pass-the-hash and pass-the-ticket. Microsoft Defender for Identity analyzed and detected account compromise at the domain level, tracking and alerting account activity for lateral movement using remote service creation. Having this view beyond endpoint and across other domains, such as identities, is a unique advantage of Microsoft 365 Defender, giving customers more robust security against today’s modern, multifaceted threats.
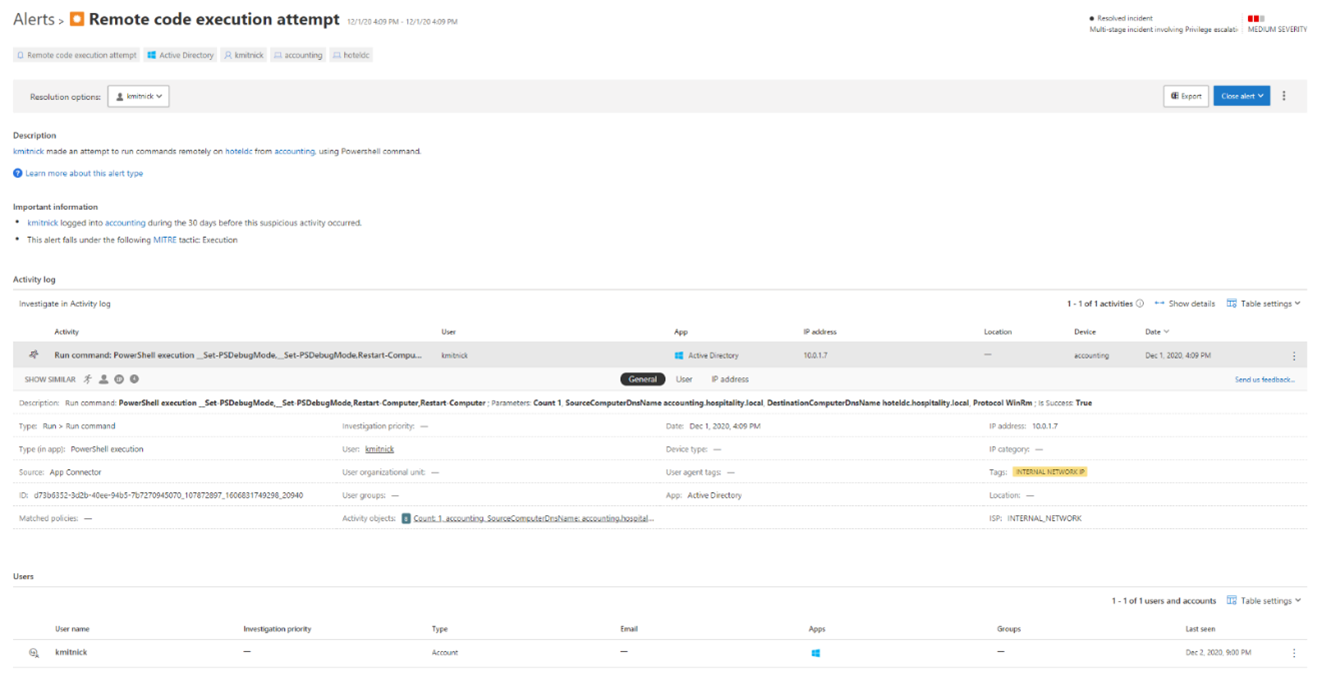
Figure 5. Defender for Identity alert page: Lateral movement using remote code execution from Windows server to endpoint detected by Defender for Identity as a suspicious identity behavior for user kmitnick.
With this depth of detection capabilities and breadth of visibility, Microsoft 365 Defender provided a unified view of the attack and empowered SOCs to respond by delivering:
- A detailed attack story of alerted activities is linked together, tagged with the appropriate MITRE ATT&CK techniques, and included every needed piece of data. This was achieved through our massive optics and unique native integration of signal, sources, and capabilities, enabling the SOC analyst to arrive at an accurate conclusion and act effectively.
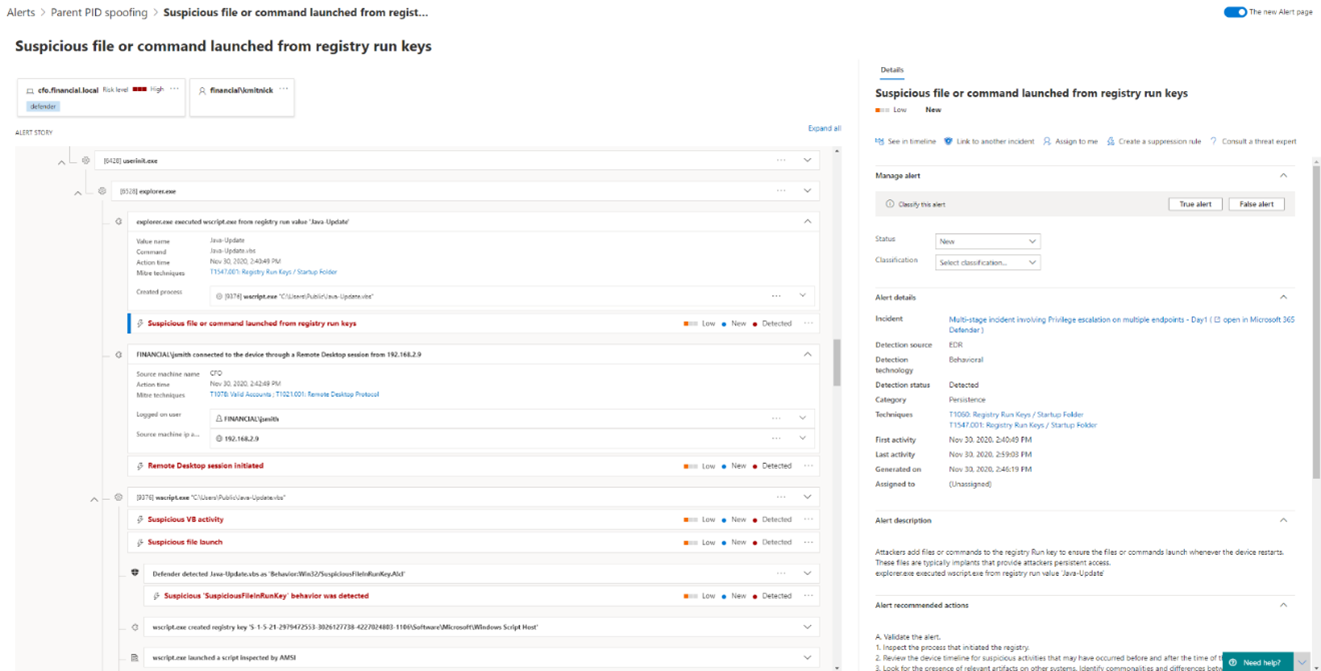
Figure 6. Defender for Endpoint alert page: Lateral movement using remote desktop connection, script execution via Registry run key, and suspicious script execution being detected.
- Two meaningful incidents generated from over 1,000 alerts, bringing together the rich information and context necessary for SOCs to effectively evaluate the scope of the attack, without the volume of triage and investigation work that is normally needed. With today’s limited time and resources, security teams need tools that rapidly and effectively investigate challenging scenarios, such as lateral movement from Windows to Linux and suspicious behavior across the organization by a compromised identity.
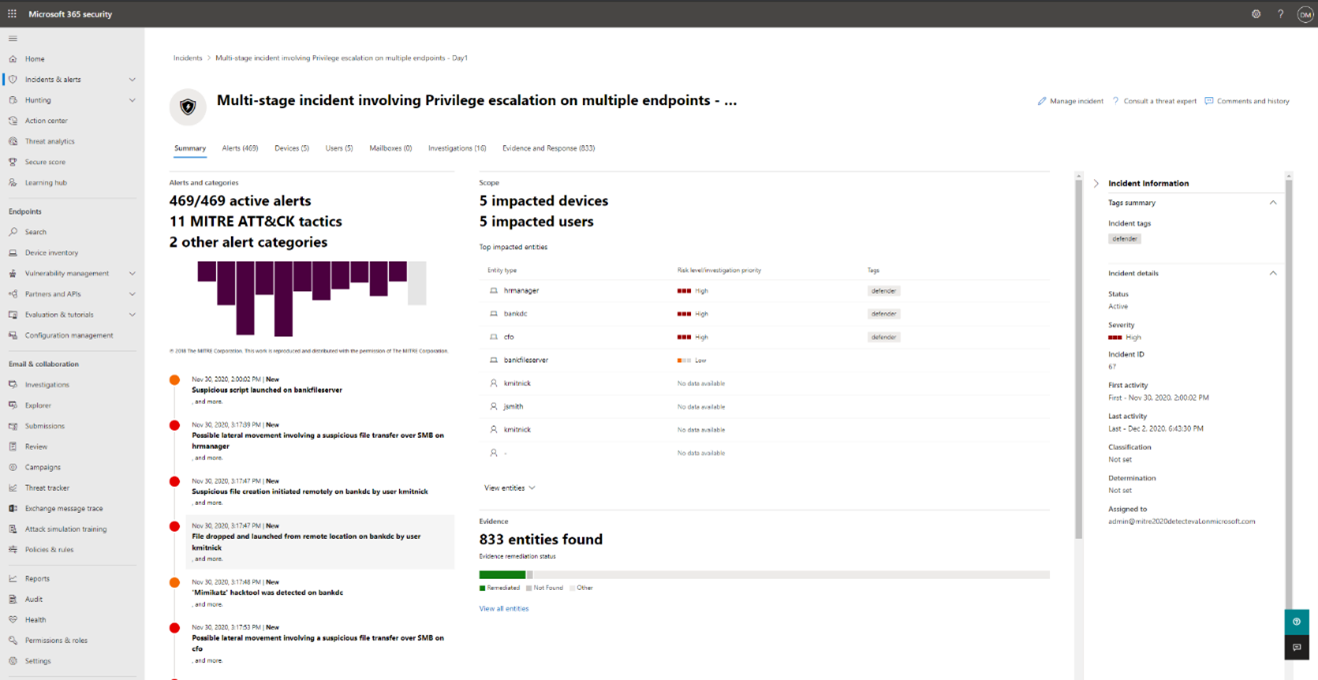
Figure 7. Microsoft 365 Defender incident page correlating all the devices, users, alerts, and evidence that describe the first attack simulated by MITRE Engenuity.
MITRE Engenuity Carbanak and FIN7 Evaluation details
The 2020 MITRE Engenuity ATT&CK Evaluations reflect an evolution of industry testing that Microsoft supports and is happy to contribute to. Our participation demonstrates our commitment to work with the industry to evaluate our capabilities using modern approaches that simulate real-world attack scenarios and that allow participants to learn from each other.
- In this evaluation, MITRE Engenuity expanded the scope to evaluate protection and detection capabilities on Linux, as well as Windows, as the Carbanak and FIN7 attacker groups used tools that interacted with both platforms, including point of sale specific technologies. We were excited to put our Linux capabilities to the test in this evaluation as we’ve continued to extend endpoint security across all the major platforms (Linux, macOS, Android, and iOS).
- This year, MITRE Engenuity did not include managed security service providers (MSSP) in the evaluation. This means that all the protection and detection value presented by Microsoft Defender for Endpoint is the result of fully automated, AI-driven advanced algorithms meant to protect organizations from advanced attacks with no additional services needed.
- Finally, for the first time, MITRE Engenuity executed two evaluations. The first was a detection evaluation, which tested our visibility and awareness of an ongoing attack and its techniques. The second was a protection evaluation, which tested our capabilities to block the attack at an early stage.
To fully execute the end-to-end detection and protection simulations of Carbanak and FIN7, MITRE Engenuity required participants to provide two different environments:
- Detection environment: MITRE Engenuity asked participants to turn off all proactive protection and blocking capabilities. For Microsoft Defender for Endpoint and the additional value of Microsoft 365 Defender, this meant all capabilities that normally block this kind of attack, such as automatic remediation flows, application isolation, attack surface reduction, network protection, exploit protection, controlled folder access, and next-gen antivirus prevention were turned off.
- Protection environment: All proactive protection and blocking capabilities are turned on. Some steps executed in the detection evaluation were chosen by MITRE Engenuity to be tested in a protection setup. That enabled Microsoft 365 Defender to prove its blocking abilities for a variety of steps, where it prevented and blocked execution at a very early stage of each step.
Real-world testing is critical to detection and prevention
As the security landscape changes, we are on a mission to help defenders solve the toughest and most critical problems. Coordinated, targeted, and advanced attacks carried out by sophisticated adversaries are some of the most complex threats that security teams encounter. This is why participating in evaluations such as MITRE ATT&CK is so important in ensuring we’re delivering solutions that empower defenders to protect their organizations. Our vision with our Microsoft Defender products is to provide industry-leading, best-of-breed, cross-domain security for the modern workplace. Microsoft 365 Defender is designed to provide extended detection and response (XDR) by combining protection for endpoints (Microsoft Defender for Endpoint), email and productivity tools (Microsoft Defender for Office 365), identities (Microsoft Defender for Identity), and cloud applications (Microsoft Cloud App Security). This unique combination helps to stop attacks before they happen, enables a rapid and complete response, and gives back time to the security team to focus on their most critical priorities.
In response to MITRE Engenuity’s call for community contribution related to the Carbanak and FIN7 actor groups, Microsoft researchers worked to consolidate and share threat intelligence with MITRE Engenuity. Microsoft shared key similarities and differences in focus, tooling, and operations observed for these two groups, as well as shared evidence for known and new tactics, techniques, and procedures (TTPs). This year, MITRE Engenuity elevated their attack scenarios, starting from gathering threat intelligence and then through the implementation of sophisticated and realistic attack chains. We’re delighted to see that MITRE Engenuity incorporated the feedback Microsoft shared from previous rounds and that this evaluation continues to evolve with each year. This kind of collaboration and continued evolution is of benefit to all in the security community. We thank MITRE Engenuity for the opportunity to contribute to and participate in this year’s evaluation.
Learn more
Microsoft Defender for Endpoint is an industry-leading, cloud-powered endpoint security solution offering vulnerability management, endpoint protection, endpoint detection and response, and mobile threat defense. With our solution, threats are no match. Take advantage of Microsoft’s unrivaled threat optics and proven capabilities. Learn more about Microsoft 365 Defender or Microsoft Defender for Endpoint, and sign up for a trial today.
To learn more about Microsoft Security solutions visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.








