Editor’s Note:
The Office 2013 Windows client update that is mentioned in this post has updated information.
Paul Andrew is a technical product manager on the Office 365 team working on identity.
Today we’re adding Multi-Factor Authentication for Office 365 to Office 365 Midsize Business, Enterprise plans, Academic plans, Nonprofit plans, and standalone Office 365 plans, including Exchange Online and SharePoint Online. This will allow organizations with these subscriptions to enable multi-factor authentication for their Office 365 users without requiring any additional purchase or subscription.
Multi-factor authentication increases the security of user logins for cloud services above and beyond just a password. With Multi-Factor Authentication for Office 365, users are required to acknowledge a phone call, text message, or an app notification on their smartphone after correctly entering their password. Only after this second authentication factor has been satisfied can a user sign in.
Multi-factor authentication has been available for Office 365 administrative roles since June 2013, and today we’re extending this capability to any Office 365 user. We’re also enhancing the capabilities that have been available since June. We’re adding App Passwords for users so they can authenticate from Office desktop applications as these are not yet updated to enable multi-factor authentication. And we’re enabling users who are authenticated from a federated on-premises directory to be enabled for multi-factor authentication.
This addition of multi-factor authentication is part of our ongoing effort to enhance security for Office 365, and we’re already working on Office desktop application improvements to Multi-Factor Authentication for Office 365, which we’ll introduce later in this post. Office 365 offers many robust built-in security features for all customers and also optional controls that enable subscribers to customize their security preferences.
Let’s take a look at how Office 365 customers can take advantage of multi-factor authentication and configure it, including using App Passwords for Office desktop applications.
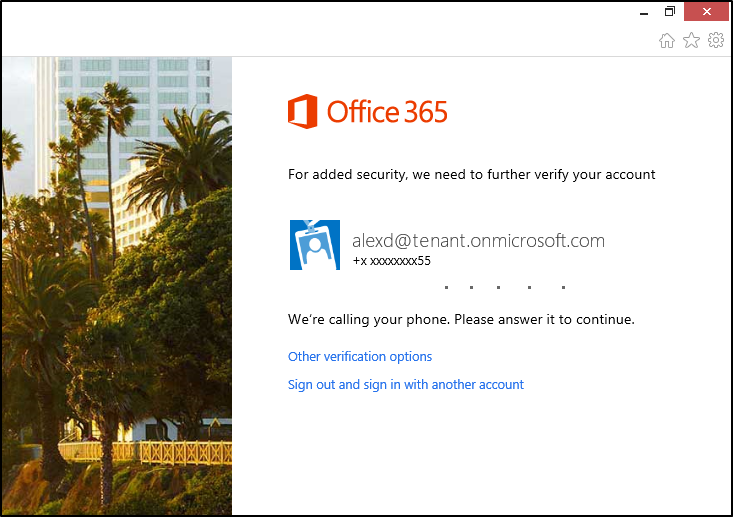
After entering your account password, you see a message like this while your phone is being called for acknowledgement.
Multi-Factor Authentication for Office 365
Office 365 administrators enroll users for multi-factor authentication through the Office 365 admin center.
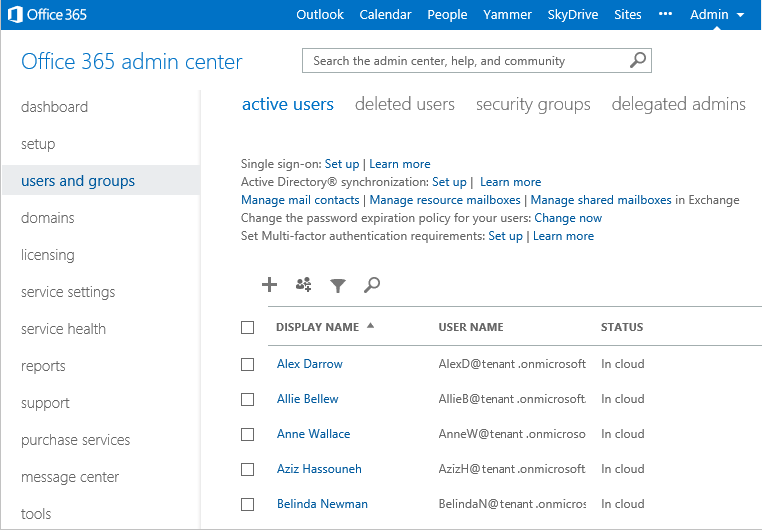
On the users and groups page in the Office 365 admin center, you can enroll users for multi-factor authentication by clicking the Set Multi-factor authentication requirements: Set up link.
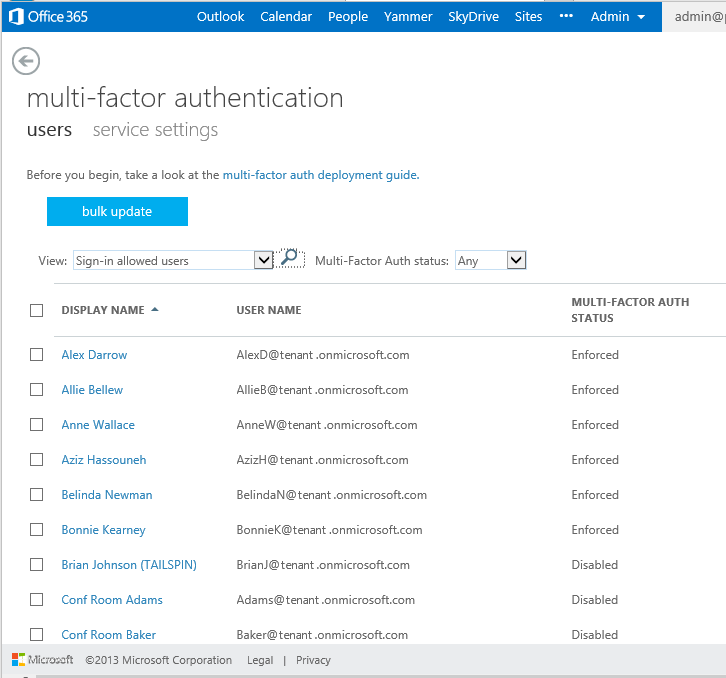
The multi-factor authentication page lists the users and allows you to enroll a user for multi-factor authentication.
After a user is enabled for multi-factor authentication, they will be required to configure their second factor of authentication at their next login. Each subsequent login is enforced and will require use of the password and phone acknowledgement.
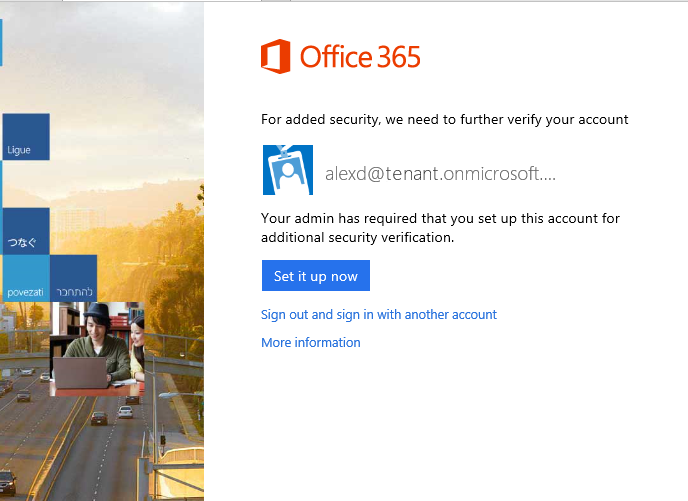
After being enrolled for multi-factor authentication, the next time a user signs in, they see a message asking them to set up their second authentication factor.
Any of the following may be used for the second factor of authentication.
- Call my mobile phone. The user receives a phone call that asks them to press the pound key. Once the pound key is pressed, the user is logged in.
- Text code to my mobile phone. The user receives a text message containing a six-digit code that they must enter into the portal.
- Call my office phone. This is the same as Call my mobile phone, but it enables the user to select a different phone if they do not have their mobile phone with them.
- Notify me through app. The user configured a smartphone app and they receive a notification in the app that they must confirm the login. Smartphone apps are available for Windows Phone, iPhone, and Android devices.
- Show one-time code in app. The same smartphone app is used. Instead of receiving a notification, the user starts the app and enters the six-digit code from the app into the portal.
Once a user is signed in they can change their second factor of authentication.
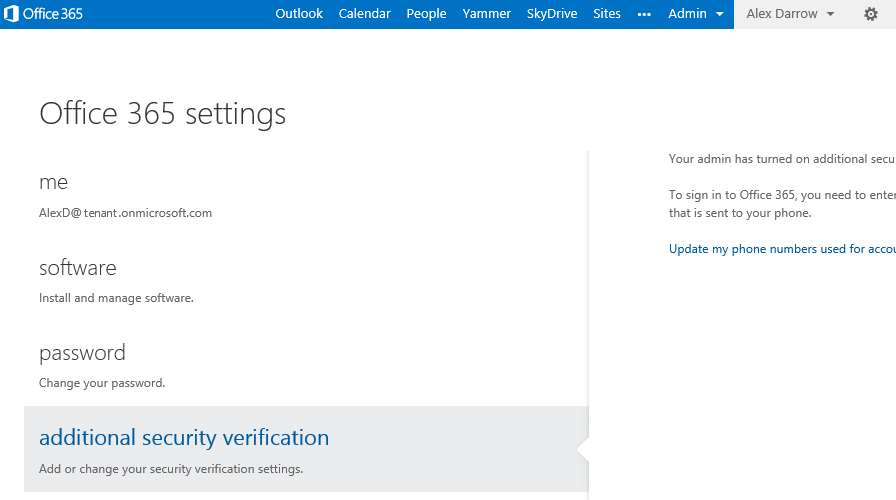
The settings menu is the little cog at the top right of the portal screen. In the settings menu clicking the additional security verification link.
App Passwords in Multi-Factor Authentication for Office 365
Users who are enrolled for multi-factor authentication are required to configure App Passwords in order to use Office desktop applications, including Outlook, Lync, Word, Excel, PowerPoint, and SkyDrive Pro.
Once an information worker has logged in with multi-factor authentication, they will be able to create one or more App Passwords for use in Office client applications. An App Password is a 16-character randomly generated password that can be used with an Office client application as a way of increasing security in lieu of the second authentication factor.
App Passwords are not available for use with PowerShell access to Office 365, and they can be turned off entirely for the Office 365 tenant for customers who have special security policies.
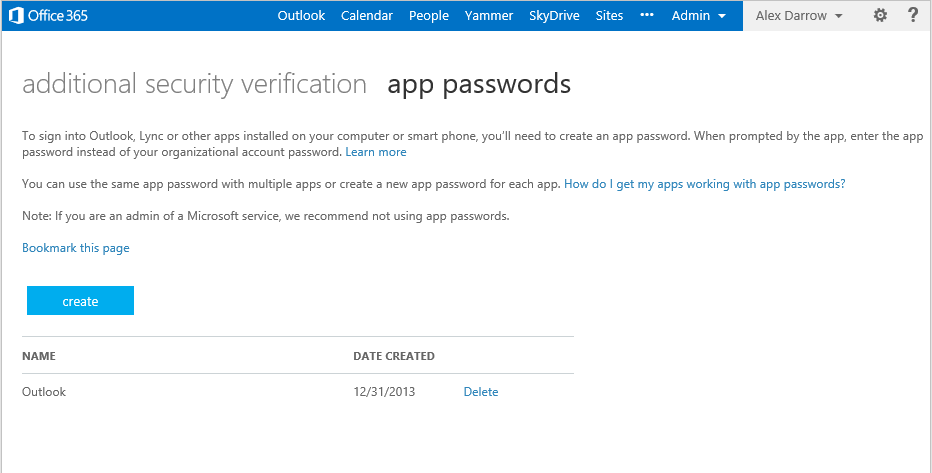
After you’ve created an App Password for an Office desktop application, such as Outlook, it is indicated in a list in your account.
Road map for multi-factor authentication in Office desktop applications
Microsoft is continuing to invest in multi-factor authentication scenarios, including Office client integration and smart card certificates. Today’s release of multi-factor authentication does not include a second factor of authentication for Office desktop applications such as Outlook, Lync, Word, Excel, PowerPoint, PowerShell, and SkyDrive Pro. As we noted in the App Password section above, however, users who have been enrolled for multi-factor authentication currently have an alternative: they can use App Passwords to log in to Office client applications with a higher level of security than a user-selected password.
Soon Office 365 customers will be able to use multi-factor authentication directly from Office 2013 client applications. We’re planning to add native multi-factor authentication for applications such as Outlook, Lync, Word, Excel, PowerPoint, PowerShell, and OneDrive for Business, with a release date planned for later in 2014. This update includes the current phone-based multi-factor authentication, and it adds capability to integrate other forms of authentication such as: third-party multi-factor authentication solutions and smart cards. Smart card support is planned to include the U.S. Department of Defense (DoD) Common Access Card (CAC) and the U.S. Federal Personal Identity Verification card (PIV), among others. We’ll give you more information about these and more updates closer to release.
For more information about Multi-Factor Authentication for Office 365 please read the TechNet article Multi-Factor Authentication for Office 365
— Paul Andrew @pndrw
Frequently asked questions
Q: Which Office 365 plans include Multi-Factor Authentication?
A: Office 365 Midsize Business, Enterprise plans, Academic plans, Nonprofit plans, and standalone Office 365 plans, including Exchange Online and SharePoint Online. MFA is not currently included in Office 365 Small Business and Office 365 Dedicated plans.
Q: Is Multi-Factor Authentication available for government customer?
A: Yes, customers with government specific G SKU plans will have Multi-Factor Authentication included. Government customers using Office 365 Dedicated will not have Multi-Factor Authentication included.
Q: Is Multi-Factor Authentication available when using smartphones?
A: Multi-Factor Authentication can be used from smartphones using the browser on the phone to access Office 365. Mail apps on smartphones can use App Password to authenticate if they have Multi-Factor Authentication enabled. Neither Multi-Factor Authentication nor App Password sign-in are currently compatible with OWA for iPhone/iPad.



