Welcome to 2023.
After the pandemic upended how we work, learn, play, and manage our lives, we find ourselves more connected than ever, with more convenient access to an ever-wider range of online tools and experiences. But as our global digital footprint continues to grow, so does the risk of cyberthreats. And now, economic uncertainty is challenging the very resources organizations need to defend against escalating attacks.
As the first line of defense, identity has become the new battleground. This is evident from the huge volume of attacks that we intercept at Microsoft.1 For example, we see 1,287 password attacks every second, or more than 111 million a day. This past year, password breach replay attacks grew to 5.8 billion per month, while phishing attacks rose to 31 million per month and password spray attacks soared to five million per month.
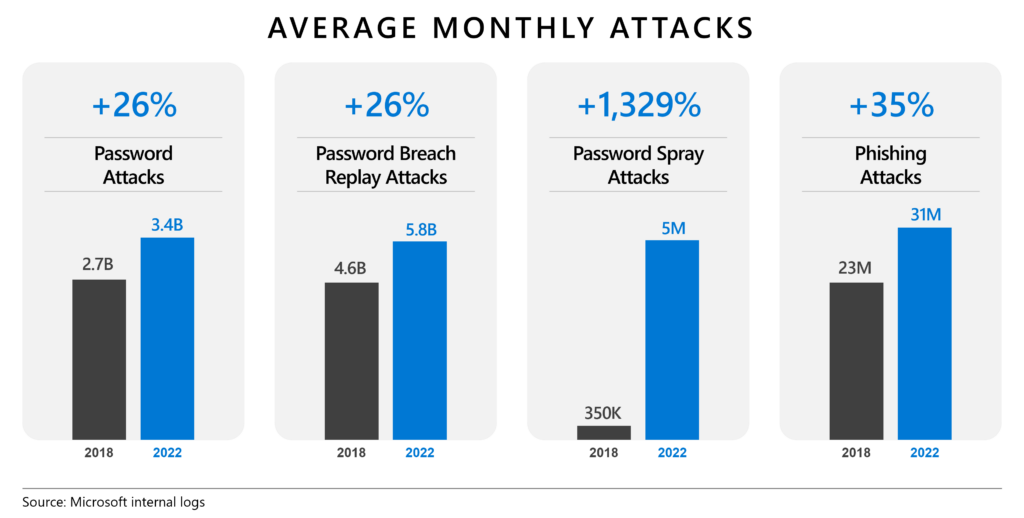
Figure 1: Growth in password-related attacks between 2018 and 2022.
Clearly, bad actors aren’t standing still. So, neither can we.
As organizations look for opportunities to do more with less, they’re no doubt considering how security teams can contribute. With that in mind, I’d like to share five identity priorities for 2023 that will pay off in ways you can actually measure:
- Protect against identity compromise using a “Defense in Depth” approach.
- Modernize identity security to do more with less.
- Protect access holistically by configuring identity and network access solutions to work together.
- Simplify and automate identity governance.
- Verify remote users in a cheaper, faster, more trustworthy way.
By adopting the latest identity innovations, you can better protect both your digital estate and your budget.
1. Protect against identity compromise using a “Defense in Depth” approach
While credential attacks are still devastatingly effective, cybercriminals are also escalating in ways that are much harder to detect; for example, bypassing basic multifactor authentication and manipulating users into giving up their credentials or second factors. They’re also infiltrating organizations through their suppliers, scouring GitHub repositories for credentials embedded in code, and stealing tokens. The most sophisticated and well-funded attackers are even attempting to take over the infrastructure that issues tokens.
Protecting user accounts is critical but no longer enough. You now must protect every layer of your identity ecosystem, including non-human or workload identities, plus the infrastructure that provides, stores, and manages all your identities. Your best bet is a Defense in Depth approach that requires close collaboration between your security operations center (SOC) and identity teams:
- Security posture management: Monitoring your organization’s identity systems and identifying misconfigurations, vulnerabilities, and missing or bad policies and controls.
- Real-time protection and remediation with identity: Enforcing Conditional Access policies based on risk aggregated from multiple sources on any suspicious activity related to user accounts in the directory.
- Identity threat detection and investigation: Examining signals from all corners of your digital estate to reveal anomalous patterns too subtle for any individual tool or team to detect.
To assist your Defense in Depth approach, Microsoft provides unified, customizable experiences across Microsoft Entra, Microsoft Defender for Identity, and Microsoft Sentinel.
The first step you can take—and your best return on investment—is to turn on multifactor authentication, a feature included with every subscription to Microsoft Azure Active Directory (Azure AD), part of Microsoft Entra.2 In our experience, of all accounts compromised in a single month, more than 99.9 percent didn’t use multifactor authentication. Employing phishing-resistant multifactor authentication methods such as Windows Hello, FIDO 2 security keys and passkeys, and certificate-based authentication (CBA) will further reduce your risk. We also recommend blocking legacy authentication, because less secure protocols like POP and IMAP can’t enforce multifactor authentication.3
Where to start: Learn more about Azure AD and Microsoft Defender.
2. Modernize identity security to do more with less
It may be tempting to stick with legacy technologies when they’re tested, familiar, and do an okay job for now, like an old car that manages to get you to and from work even with the engine warning light flashing. You may be understandably worried about business disruption and the cost of transitioning from old to new, but “patchwork quilts” of inflexible and poorly integrated technologies are expensive to maintain and leave gaps in your defenses. And since cybercriminals continue to innovate their tactics, your risk will only increase.
Modern, cloud-native identity solutions such as Microsoft Entra are more resilient, more scalable, and more secure against modern threats. They’re also better equipped to accommodate the rapid changes to products, services, and business processes necessary to compete in today’s unpredictable business environment. You can significantly increase business agility, better fortify your environment against future threats, and save money by taking advantage of the advanced, integrated features available in Microsoft Entra.
Modernization is less daunting if you break it down into well-defined, time-bound projects with clear benefits. Start by migrating off of Active Directory Federation Services (AD FS) to simplify your environment and retire those on-premises servers (if CBA has been a blocker for you, it’s now available in Microsoft Entra).4 Next, connect pre-integrated applications to Azure AD to gain advantages such as single sign-on.5 Finally, inventory your security environment, consolidate any redundant tools to reduce your management burden, and apply your subscription savings to other priorities.
Where to start: If you’re using AD FS, explore the benefits of modernizing identity and access capabilities.
3. Protect access holistically by configuring identity and network access solutions to work together.
As any sports fan knows, highly skilled defenders are far more effective when they communicate and work together. You can strengthen your overall security posture by integrating tools that currently operate in silos. For example, many organizations employ network access solutions that recognize device- and network-related risks and prevent bad actors from crossing the network to compromise on-premises and legacy web-based applications. But many of these tools lack in-depth identity awareness, which can weaken your secure access posture.
Applying a Zero Trust approach means explicitly verifying every access request using every available signal. You can get the most detailed picture of session risk by combining everything the network access solution knows about the network and device with everything the identity solution knows about the user session.
If your network access vendor is part of the Microsoft Secure Hybrid Access program, you can integrate their solution with Azure AD.6 This way, the on-premises applications and custom or legacy web-based apps you’re protecting with your network access solution also gain many of the same benefits that pre-integrated apps enjoy.7
Where to start: Learn how to integrate your network access solution with Azure AD.
4. Simplify and automate identity governance
Security awareness and mitigation efforts often focus on protecting your organization from external threats, such as hackers employing stolen or easily guessed credentials. But threats can be internal, too. For example, users tend to accumulate access to apps and resources they no longer need. Similarly, organizations sometimes forget to remove access granted to external collaborators when projects or contracts end. Organizations even discover still-active accounts of former employees that retain access to critical resources.
This is where identity governance comes in. Because governance helps to reduce internal risk—whether from simple neglect or actual malfeasance—it’s critical for organizations of every size, geography, and industry. Microsoft Entra Identity Governance is a complete identity governance solution that helps you comply with regulatory requirements while increasing employee productivity through real-time, self-service, and workflow-based entitlements. It extends capabilities already available in Azure AD by adding Lifecycle Workflows, separation of duties, and cloud provisioning to on-premises apps. Because it’s cloud-delivered, Microsoft Entra Identity Governance scales to complex cloud and hybrid environments, unlike traditional on-premises identity governance point solutions.
If you already have an identity governance solution in place, you’ll save money, reduce complexity, and close security gaps by consolidating multiple point solutions and adopting a solution that grows with you.
Where to start: Learn more about the Microsoft Entra Identity Governance Preview and try it for free today.
5. Verify remote users in a cheaper, faster, more trustworthy way
Identity verification for customers and employees is a significant expense for many organizations. When people apply for school admissions, loans, and jobs, a lot of time goes into the manual collection and verification of documents to prove age, citizenship, income, skills, professional experience, and more. If you collect and store such information in a centralized database, then you’re responsible for everything it takes to fully secure and protect it. This not only creates risk for you, but it also creates risk for your employees or customers—they naturally want control over who accesses their personal information and how it gets used.
Verifiable credentials introduce the concept of a per-claim trust authority. The trust authority populates a credential with a claim about you that you can store digitally. For example, a loan officer can confirm your current employment by requesting digital credentials issued by your employer and verifying them in real time. Our standards-based implementation, Microsoft Entra Verified ID, helps organizations reduce the burden of identity verification and simplify processes such as new employee onboarding. Since we launched it in August 2022, customers worldwide have already started using it to streamline verification processes.
Verified ID is currently available to all Azure AD customers at no additional charge. You can use APIs to create custom apps with simple and privacy-respecting identity verification built in.8
Where to start: Learn more about Verified ID.
Microsoft can help you secure more with less
As you kick off the new year, the strategies outlined in this blog can help you navigate tough decisions on where to focus your energies and how to empower your organization to do more with less. Our recommendations come from serving thousands of customers, collaborating with the industry, and protecting the digital economy from ever-evolving threats. We look forward to continuing our partnership with you—from day-to-day interactions to joint deployment planning to direct feedback that informs our strategy. As always, we remain committed to building the products and tools you need to defend your organization throughout 2023 and beyond.
Learn more about Microsoft Entra.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
1Your Pa$$word doesn’t matter, Alex Weinert. July 9, 2019.
2How it works: Azure AD Multi-Factor Authentication, Microsoft. August 25, 2022.
3New tools to block legacy authentication in your organization, Alex Weinert. March 12, 2020.
4Overview of Azure AD certificate-based authentication, Microsoft. October 18, 2022.
5What is single sign-on in Azure Active Directory? Microsoft. December 7, 2022.
6Secure hybrid access through Azure AD partner integrations, Microsoft. July 8, 2022.
7Benefits of migrating app authentication to Azure AD, Microsoft. December 15, 2022.
8Request Service REST API, Microsoft. September 4, 2022.








