Stopping C2 communications in human-operated ransomware through network protection
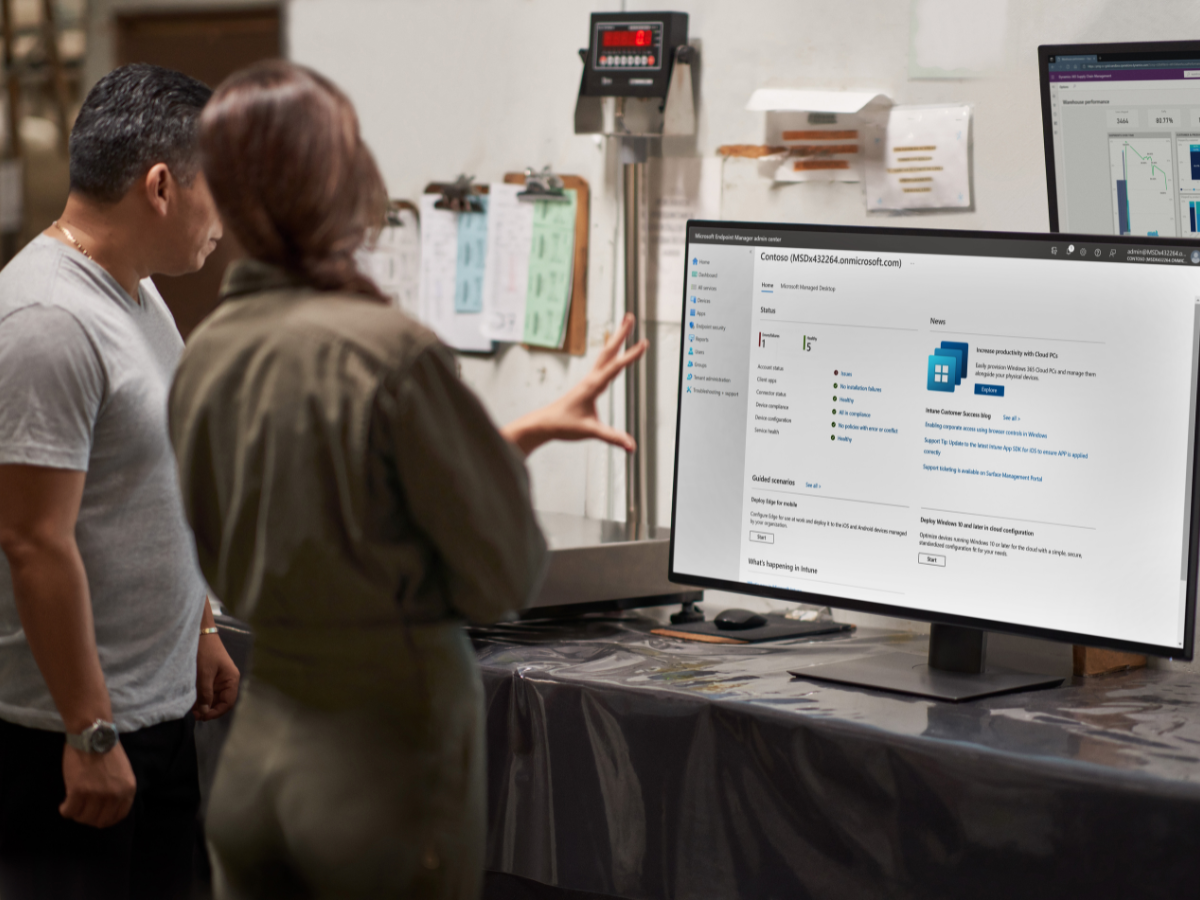
Providing advanced protection against increasingly sophisticated human-operated ransomware, Microsoft Defender for Endpoint’s network protection leverages threat intelligence and machine learning to block command-and-control (C2) communications.