Looking back at the last two years, to say that our security strategies have evolved would be an understatement. Organizations around the world made overnight transitions to remote work models in response to a global pandemic, forcing them to reassess attack surface areas as they underwent an accelerated digital transformation. Meanwhile, cybercriminals seized new opportunities—introducing COVID-19-themed social engineering campaigns and accelerated ransomware attacks. Nation-state actors launched increasingly bold and sophisticated nation-state attacks.1
In this environment, security transformation has become key to survival. The mandate to explicitly verify every access request, focus on least privilege access overall, and constantly assume breach to maintain vigilance was made clear, as exemplified by calls from governments and businesses worldwide to accelerate the adoption of Zero Trust strategies.
Sidebar: Zero Trust is a proactive, integrated approach to security across all layers of the digital estate that explicitly and continuously verifies every transaction, asserts least privilege, and relies on intelligence, advanced detection, and real-time response to threats.
The evolution of Zero Trust
Microsoft has embraced Zero Trust to defend our own estate and as a guiding principle for the development of our products. We have also helped thousands of our customers—including Siemens— deploy Zero Trust strategies, accelerate their digital transformation, and increase frequency of advanced attacks using our Zero Trust architecture.
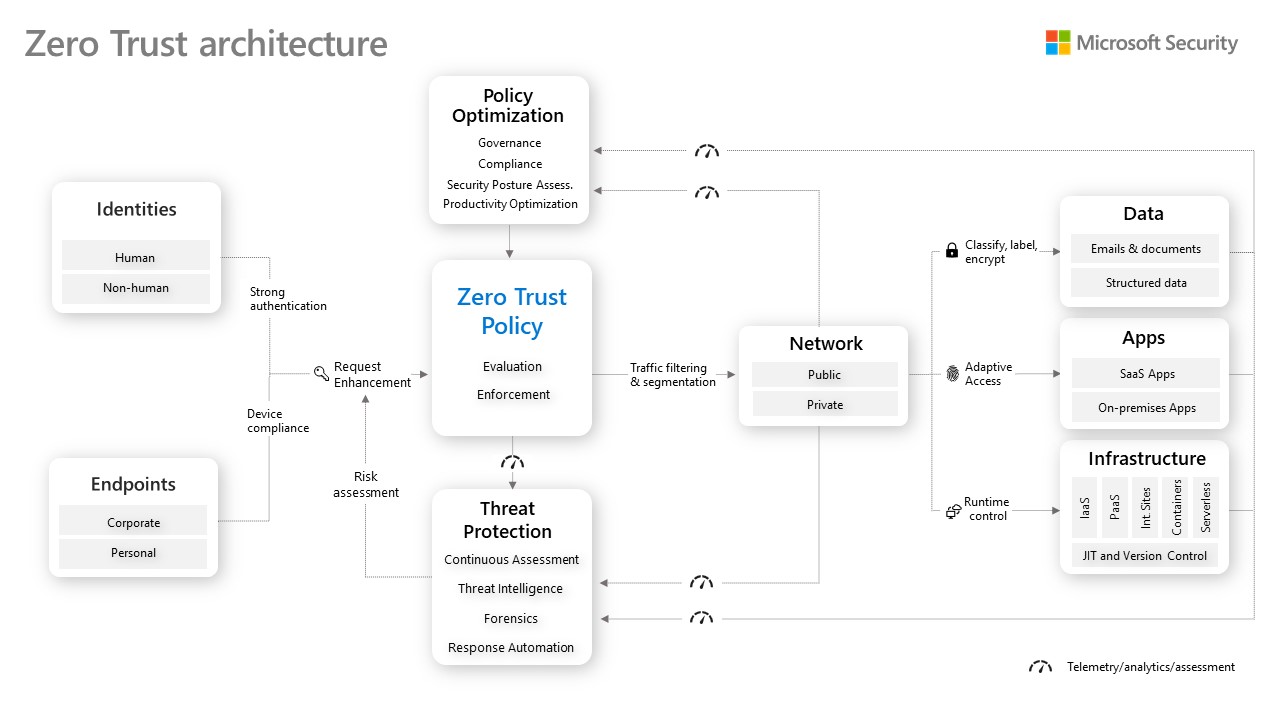
Figure 1: Learnings across thousands of Zero Trust deployments have informed our Zero Trust architecture, which emphasizes the critical importance of integrating policy enforcement and automation, threat intelligence, and threat protection across security pillars.
Lessons learned and emerging trends
Today, we’re publishing the new whitepaper, Evolving Zero Trust, to share the key lessons we’ve learned by embracing Zero Trust at Microsoft and supporting thousands of organizations in their Zero Trust deployments. This informs our beliefs on Zero Trust implementations needed to evolve to adapt and keep organizations protected. We’re also sharing the evolution of our recommended Zero Trust architecture and maturity model that has been informed by these insights.
Highlights from the paper include:
- Lessons from the most successful organizations: The last couple of years have reinforced the importance of applying Zero Trust comprehensively across the digital estate. Organizations that were furthest along in their journeys were more resilient against sophisticated attacks, improved user experiences, and reduced implementation and management costs. We also saw that successful organizations doubled down on automation and a robust Zero Trust governance strategy—both of which can improve security posture and time to remediation while reducing the workload on scarce security personnel.
- Emerging industry trends: Zero Trust is a dynamic security model that continues to evolve to meet current threats and business realities. Going forward, we will see deeper integration of Zero Trust across pillars—leading to simplified policy automation, more advanced and intelligent threat detection, and more comprehensive attack mitigation. We also predict a wider adoption of the principles behind Zero Trust—verify explicitly, enforce least privilege access, and assume breach—to include the tools and processes used to develop applications, the hybrid and multi-cloud environments in which they run, as well as the application themselves.
- A more connected Zero Trust architecture: The learnings highlighted above led us to refine our Zero Trust architecture to more emphasize the critical importance of capturing telemetry from across the environment to inform policy decisions, provide better threat intelligence, measure the user experience, and more. The updated architecture showcases the importance of integrating policy enforcement and automation, threat intelligence, and threat protection across security pillars.
This document showcases the incredible evolution and acceleration in the adoption of Zero Trust security strategies. Just a few years ago, Zero Trust was merely a new buzzword for many organizations. Today, 76 percent of large organizations have adopted a Zero Trust approach. We hope that the lessons, trends, and positions we shared in this document are helpful in the planning and application of your own Zero Trust strategy.
The insights and actionable learnings in this document have been provided by a diverse group of customers, partners, and security-focused individuals working across applications, data, endpoint management, identity, infrastructure, networking, threat protection, and our own internal security organization. I’d like to thank our customers and partners for their expertise and insights, as well as my colleagues for their contributions to this whitepaper, architecture, and maturity model guidance.
Learn More
Get the complete Zero Trust whitepaper for key insights, Zero Trust architecture, and a maturity model to help accelerate your adoption.
For a repository of technical resources to help accelerate the deployment and integration of Zero Trust across all security pillars, visit the Zero Trust Guidance Center.
Use the Zero Trust Assessment tool to evaluate your Zero Trust security posture, maturity, and receive practical recommendations to help reach key milestones.
Read the 2021 Microsoft Digital Defense Report (MDDR) for in-depth findings about Microsoft’s tracking of nation-state threat groups, specific threat actors, attack methods, and more.
To learn more about Zero Trust, visit Microsoft Security’s Zero Trust website.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
1Microsoft Digital Defense Report shares new insights on nation-state attacks, John Lambert, Microsoft. 25 October 2021.








