We’re now a year into our new reality, and two trends stand out. First, people need even more flexibility as we work, learn, and collaborate in a world without perimeters. And second, bad actors are getting even more sophisticated. They’re adding new attack vectors and combining them in new creative ways, as we just saw with Solorigate.
In January, I shared our top five identity priorities for 2021 to help you strengthen security and accelerate your transition to the new hybrid work era. More than ever, organizations need to strengthen their defenses to give employees, partners, and customers the flexibility to work from anywhere using apps that live inside and outside the traditional corporate network perimeter. That’s why Zero Trust, a security strategy that combines maximum flexibility with maximum security, is so crucial.
For IT pros and security professionals, the implementation of Zero Trust should be simple and straightforward. For users, it should never get in the way, and it should fit into familiar workflows and habits. This week, on the virtual Microsoft Ignite stage, I’m announcing several Azure Active Directory (Azure AD) innovations that will help make life easier for you and your employees now—and help you stay prepared for whatever comes next.
Give your employees a secure and seamless user experience
As part of our commitment to making security as seamless as possible, passwordless authentication is now generally available for organizations to deploy at scale. Your IT admins, employees, and partners can benefit from increased security and simplicity. We’ve made it easy to roll out passwordless at scale with expanded policies that define which authentication methods specific users or groups can use. New reporting capabilities allow you to see the usage and adoption of passwordless authentication methods across your organization. To help you simplify and secure remote access, we’ve also released the preview of Temporary Access Pass, a time-limited code used to set up and recover a passwordless credential.
Microsoft already has more than 200 million passwordless users across our consumer and enterprise services. We’re excited to see even more customers adopting passwordless each day. Axiata Group is the first company in Southeast Asia to eliminate passwords for their employees. They went passwordless using Windows Hello for Business and the Microsoft Authenticator app. Abid Adam, group chief risk and compliance officer at Axiata Group said, “Rather than adding friction with long passwords that create risk for the organization, we turned to biometrics. Now with Windows Hello, security is baked into our ecosystem, and we have better access to information with greater barriers to bad actors. It’s a win-win for our security team, our employees, and the company.” Similarly, in Europe, Umeå municipality wanted to strengthen security and eliminate the use of passwords. With help from Onevinn and Yubico partners, they were able to roll out their first passwordless deployment in less than 10 days. Watch my interview on Microsoft Mechanics to see passwordless in action.
Going passwordless not only simplifies the user experience but also strengthens your security posture. And thanks to Azure AD Conditional Access, you no longer need to request multifactor authentication every time someone accesses an app that touches sensitive data. Instead, you can step up authentication based on what the user is trying to do within the app—for example, downloading a highly confidential document. With Azure AD Conditional Access authentication context, coming to preview soon, you can move away from one-size-fits-all security and adopt more granular policies that protect resources with the right level of controls based on user actions or the data they are trying to access.
Announcements:
- General availability of passwordless authentication.
- Preview of Temporary Access Pass.
- Azure AD Conditional Access authentication context coming to preview soon.
Secure access to all apps
Most of you manage multi-cloud environments. Your developers are building apps that are distributed across Microsoft Azure, Amazon Web Services (AWS), and Google Cloud Platform. They need to sign in to each cloud with only one set of credentials. So that you can quickly configure single-sign-on (SSO) and user provisioning, we’re constantly expanding the Azure AD app gallery with as many pre-integrations as possible—even with our competitors.
AWS Single Sign-On app is now pre-integrated with Azure AD and available in the app gallery. This integration lets you connect Azure AD to AWS SSO, a cloud-based service that simplifies SSO access across multiple AWS accounts and resources. You can centralize management of user access to AWS, while your employees can gain access using their Azure AD credentials.
During the past year, many organizations have relied on our Azure AD App Proxy service to help employees secure remote access to on-premises apps. Usage grew more than 100 percent last year, helping organizations move away from VPN solutions. Today, we’re adding two new features to help you get the most out of App Proxy. First, native support for header-based authentication with App Proxy is now generally available. Second, traffic optimization by region for App Proxy is now in preview. This new feature lets you designate which region your App Proxy service connector group should use and select the same region as your apps. This new feature helps reduce latency and improve performance.
To protect your legacy, on-premises applications, we’re expanding the list of our secure hybrid access partnerships to include Datawiza, Perimeter 81, Silverfort, and Strata. In addition to connecting your on-premises apps, partners like Datawiza, Strata, and Silverfort can help you discover and prioritize apps and resources to migrate to Azure AD. “Silverfort is thrilled to be able to collaborate with Azure AD to enable unified secure access to legacy, on-premises apps, and resources,” said Ron Rasin, vice president of product and strategic alliances at Silverfort. “Identity has become the primary security control plane making it critical that organizations can discover, prioritize, and migrate the apps and resources to a central identity solution like Azure AD.”
Solorigate taught us that in many cases, cloud environments are more secure than on-premises. To strengthen your defenses, it’s critical to minimize your on-premises footprint and manage all your apps from the cloud. The process of discovering applications across different environments and prioritizing them for cloud modernization can be daunting, however. To make it easier, we’re announcing the general availability of Active Directory Federation Services (AD FS) activity and insights report. This report assesses all AD FS applications for compatibility with Azure AD, checks for any issues, and provides guidance on preparing individual applications for migration to Azure AD.
Announcements:
- AWS Single Sign-On now available in Azure AD app gallery.
- General availability of AD FS activity and insights report.
- New secure hybrid access partnerships with Datawiza, Perimeter 81, Silverfort, and Strata.
- General availability of Azure AD App Proxy support for header-based authentication apps.
- Preview of Azure AD App Proxy support for traffic optimization by region.
Secure your customers and partners
A strong Zero Trust approach requires that we treat access requests from customers, partners, and vendors just like requests from employees: verify every request, allow users to access the data they need only when they need it, and don’t let guests overstay their welcome. With Azure AD, you can apply consistent access policies to all types of external users.
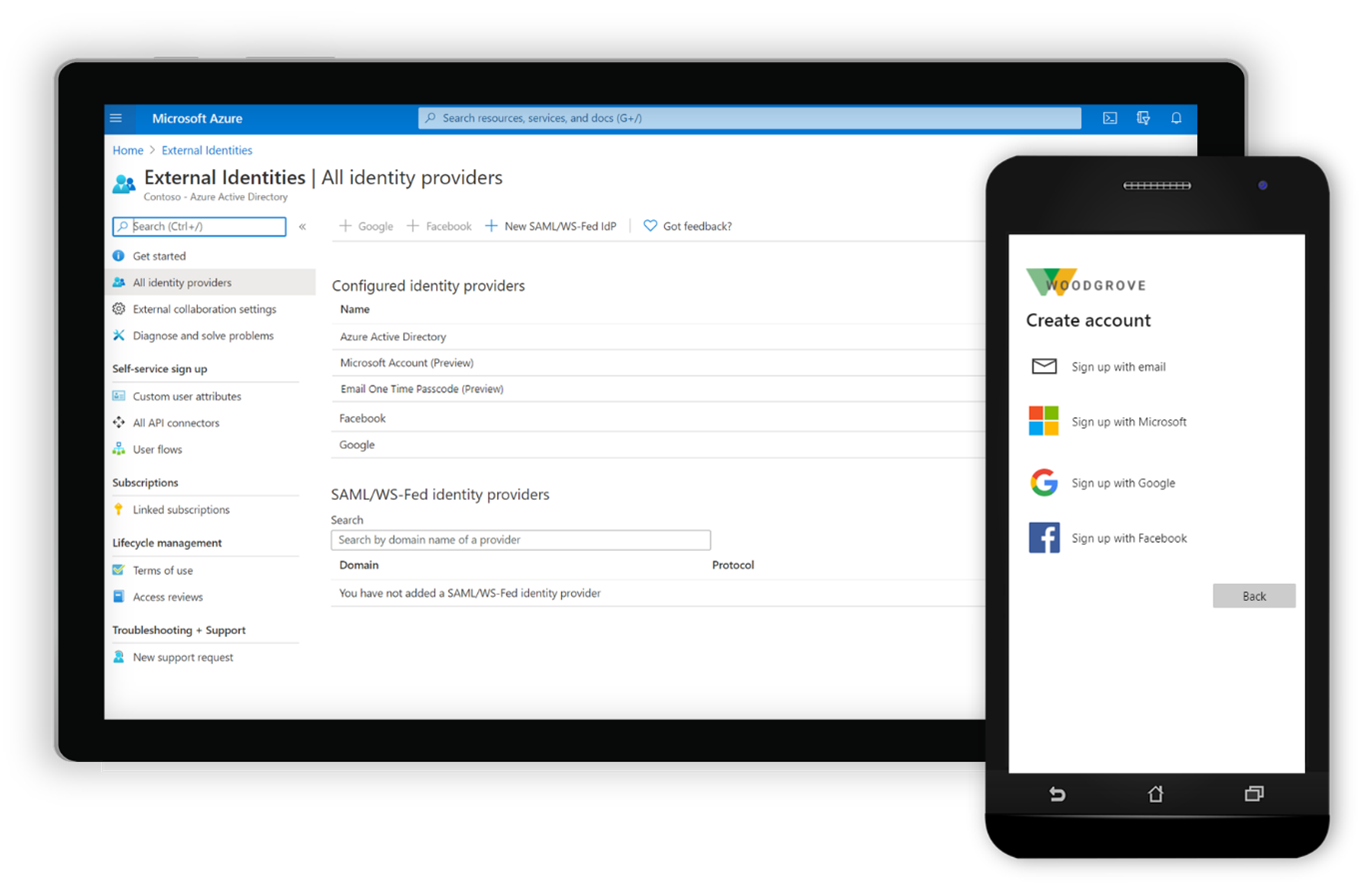
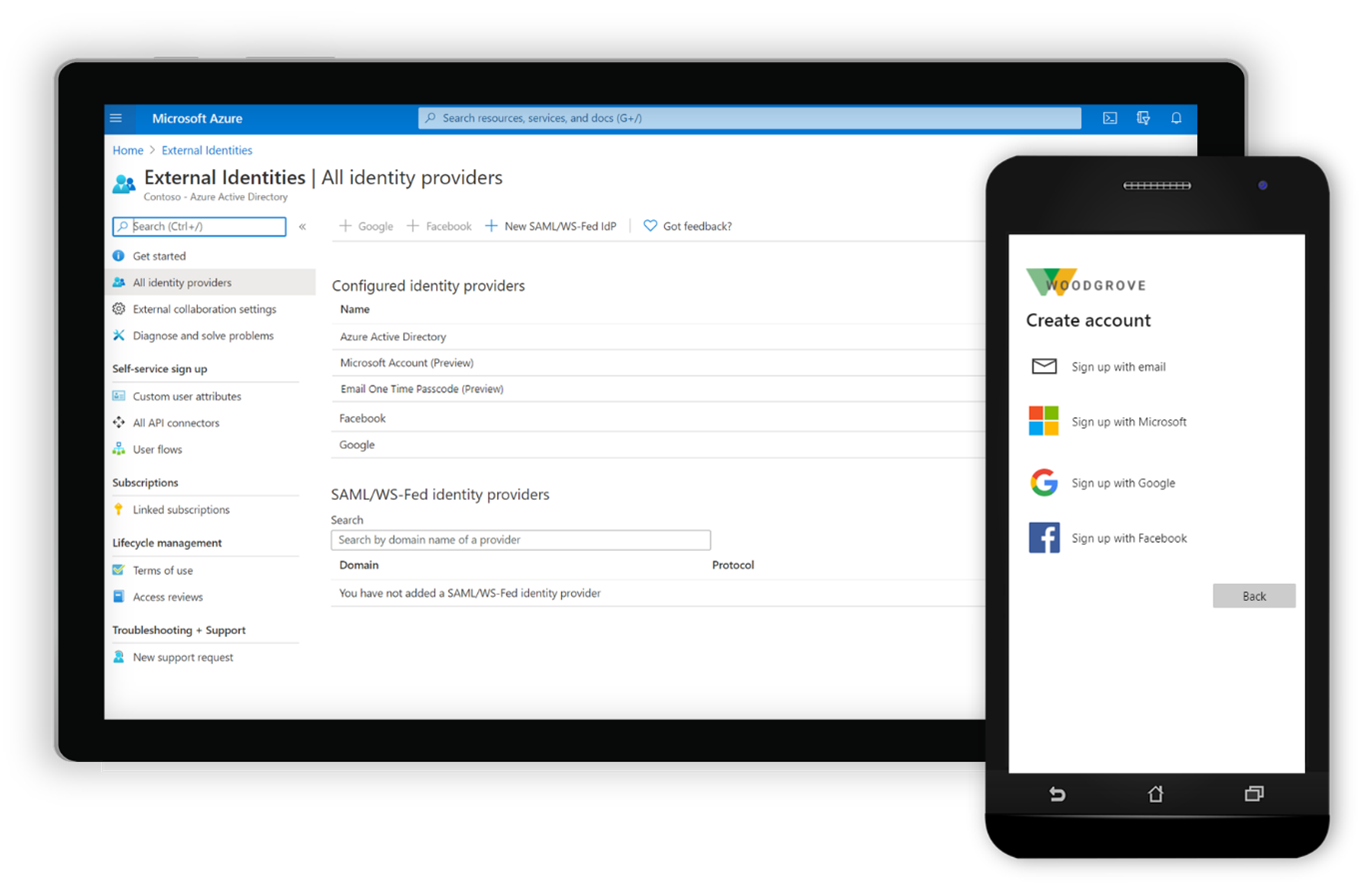
Generally available starting this month, Azure AD External Identities is a set of capabilities for securing and managing identity and access for customers and partners. Self-service sign-up user flows in Azure AD apps make it easy to create, manage, and customize onboarding experiences for external users, with little to no application code. You can integrate support for sign-in using Google and Facebook IDs and extend the flow with powerful API connectors. Using Azure AD Identity Protection, you can protect your business-to-business (B2B) and business-to-consumer (B2C) apps and users with adaptive, machine learning–driven security.
With automated guest access reviews for Microsoft Teams and Microsoft 365 groups, now generally available, Azure AD will prompt you to review and update access permissions for all guests added to new or existing Teams or groups on a regular schedule. The process of cleaning up access to sensitive resources that your guest users no longer need will become less manual—and less neglected.
Announcements:
- General availability of Azure AD External Identities.
- General availability of Azure AD access reviews for all guests in Teams and Microsoft 365 groups.
The future of identity is bright
While 2020 was a challenging year, we have much to look forward to in 2021, with innovations that will deliver more security, transparency, and privacy for users. Last Microsoft Ignite, I talked about verifiable credentials and our commitment to empowering every person to own their own identity thanks to decentralized identifiers. I’m happy to share that Azure AD verifiable credentials is entering preview in just a few weeks. Developers will get an SDK, with quick-start guides, for building apps that request and verify credentials, just like they do with usernames and passwords. I’m also excited to announce that we are partnering with some of the leading ID verification partners—Acuant, Au10tix, Idemia, Jumio, Socure, Onfido, Vu Security—to improve verifiability and secure information exchange.
Verifiable credentials let organizations confirm information about someone—like their education and professional certifications—without collecting and storing their personal data. This will revolutionize the way we grant permissions to access our information. Organizations will be able to issue digital versions of a variety of credentials such as physical badges, loyalty cards, and government-issued paper documents based on open standards. Because the digital information is verified by a known party, it’s more trustworthy, and verification will only take minutes instead of days or weeks.
Individuals get more control over what information they share with whom, and they can restrict access to that shared information at any time. They only have to verify a credential once to use it everywhere. To manage their credentials, they can use the Microsoft Authenticator app and other wallet apps that support open standards, such as the pilot application built by Keio University for their students.
Announcement:
- Preview of Azure AD verifiable credentials.
And finally, I’m happy to share that we’re releasing a new Microsoft Identity and Access Administrator Certification, which you can find at the Microsoft Security Resources portal. This training helps admins design, implement, and operate Azure AD as the organization’s security control plane.
Announcement:
- Release of the Microsoft Identity and Access Administrator Certification.
The new features announced at Microsoft Ignite will make it easier to provide seamless user experiences in the hybrid workplace and to strengthen your defenses against attacks that are increasingly sophisticated. As you try these new tools, please send us your feedback so we can continue to build advancements that help you keep your employees secure, connected, and productive.
Let’s make 2021 the Year of Passwordless!
To see these features in action when I take the Microsoft Ignite stage tomorrow, register for free at Microsoft Ignite and watch my session starting at 5 PM Pacific Time. Follow Microsoft Identity at @AzureAD on Twitter for more news and best practices.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security Blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.