 We periodically update our stories, but we can’t verify that they represent the full picture of our current situation at Microsoft. We leave them on the site so you can see what our thinking and experience was at the time.
We periodically update our stories, but we can’t verify that they represent the full picture of our current situation at Microsoft. We leave them on the site so you can see what our thinking and experience was at the time.
For any large enterprise like Microsoft, monitoring threats to infrastructure and applications developing and maintaining an always-on Security Information and Event Management (SIEM) solution like Microsoft Sentinel that’s equipped to ward off threats isn’t only a weighty task but also a truly challenging undertaking.
The threat landscape is constantly evolving, and data breaches—originating from outside or within organizations—are commonplace. Organizations now acknowledge that securing their digital perimeter is an insufficient and inherently reactive approach. That’s because modern security solutions, to be robust, must protect the entire enterprise environment, including core business processes, the sensitive data that those processes might expose, and the systems that support those processes.
This recognition prompted Microsoft to seek a more complete, continuous, and dynamic solution to better protect its SAP assets—Microsoft Sentinel, a cloud-native SIEM platform that uses built-in AI to quickly help analyze large volumes of data across an enterprise. Microsoft’s SAP assets include applications that support Microsoft’s core business processes and combined, comprise an impressive 24 terabytes (TB) of data.
Microsoft had a two-fold rationale for developing its new Microsoft Sentinel SAP SIEM solution: to better detect suspicious activity and to fully document security incidents and how the organization resolves them. Enterprise resource planning (ERP) systems like SAP are facing increasing cybersecurity threats, across the industry spectrum, from healthcare and manufacturing, to finance, retail, and e-commerce.
Threat actors, recognizing such systems’ vulnerabilities, have identified ERP systems as a prime target. SAP vulnerability is a critical concern for enterprise executives and senior security professionals, given that the average cost of an SAP breach is $5 million per attack. That cost doesn’t figure in the reputational damage a breach or attack might confer, which is often substantial and prolonged.
Identifying threats—and a solution
Microsoft Sentinel and Microsoft’s SAP Security teams defined a roadmap to address current challenges and chart a path to using the preventive and detective capabilities of Microsoft Sentinel and Microsoft Azure. Additionally, the collaborative efforts of SAP and Microsoft Azure increase end-to-end visibility across enterprise systems and applications and help bolster system resilience. Although Microsoft has tools in place to detect and log threats across its SAP landscape, the challenge was managing the number of tools, the data sources, and the effort required to analyze and help remediate a threat.
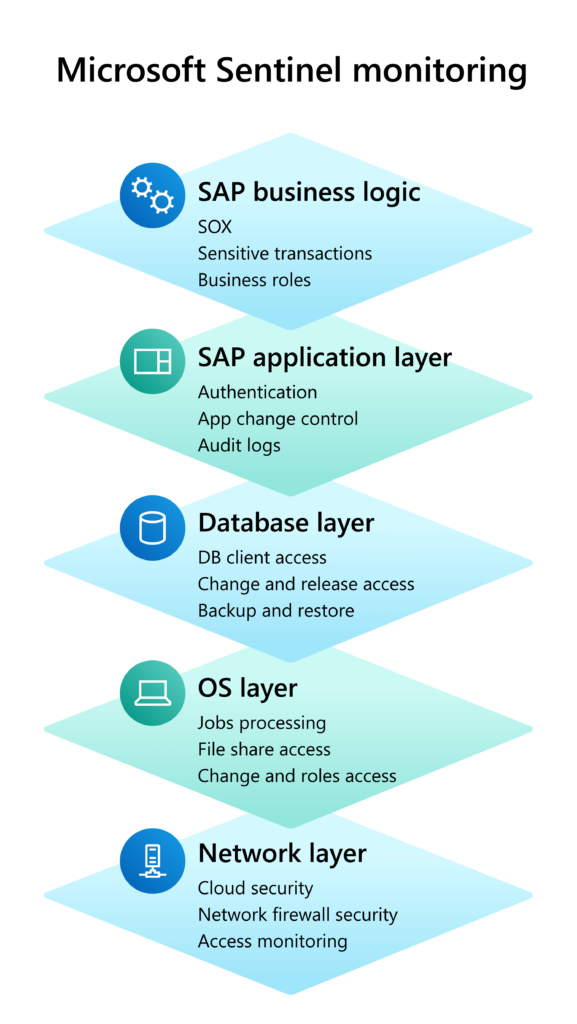
Considering that any breach in Microsoft SAP applications could have catastrophic consequences for us, we knew that we needed a solution that enabled rapid vulnerability detection and monitoring capabilities to reduce risks to the organization. We needed an internally managed and configured SIEM solution that could baseline user behaviors and detect anomalies across SAP to include the OS and network layer, the database layer, and the application and business logic layers.
—Kusuma Sri Veeranki, senior software engineer and SAP security lead, Microsoft Digital
At the same time, Microsoft also wanted to implement a centralized SIEM solution that detects and helps prevent threats. The SIEM tools in use were effective, but the monitoring structure was inherently reactive because it didn’t allow for real-time monitoring. When a potential threat or an active security incident was identified, an alert was generated. However, the time to assess and remediate threats was variable, and response lags were common. Further, the process for addressing some vulnerabilities involved patching, for example, so any exposure remained viable until patches were applied across the system. Finally, there wasn’t an easy way to follow an SAP security alert through the system to determine the remedial actions taken within Microsoft and by whom.
Microsoft also recognized that the existing SAP SIEM solution didn’t always meet its stringent compliance requirements and didn’t permit sufficient visibility into the entire threat environment. And from an enterprise-wide perspective, Microsoft was essentially operating separate corporate and SAP security solutions, an outdated model that the company sought to replace. The new monitoring solution, when operational, would include a separate Sentinel instance for SAP but would also fully integrate with the Microsoft corporate Security Operations Center (SOC).
We’re excited to be able to use the capabilities that Sentinel provides our customers out of the box along with SAP specific capabilities on an initiative as important as Microsoft SAP security. This represents a new approach in SIEM solutions.
—Yoav Daniely, principal group product manager, Microsoft Security, Compliance, Identity, and Management
“Considering that any breach in Microsoft SAP applications could have catastrophic consequences for us, we knew that we needed a solution that enabled rapid vulnerability detection and monitoring capabilities to reduce risks to the organization,” says Kusuma Sri Veeranki, a senior software engineer and SAP security lead for Microsoft Digital, the organization that powers, protects, and transforms the company. “We needed an internally managed and configured SIEM solution that could baseline user behaviors and detect anomalies across SAP to include the OS and network layer, the database layer, and the application and business logic layers.”
The ideal solution, Veeranki says, would also permit visibility into all other systems, products, and applications that interconnect with SAP.
SAP as Microsoft Sentinel Customer Zero
To develop its new SIEM solution for SAP, the organization decided to use Microsoft Sentinel, a relatively new product, in conjunction with Microsoft’s existing security, orchestration, automation, and response (SOAR) platform. Developed initially for Microsoft Azure, Microsoft Sentinel is designed to collect data and monitor suspicious activities at cloud scale by using sophisticated analytics and threat intelligence. Recently cited in a Forrester Consulting study as an efficient, highly scalable, and flexible SIEM solution that incorporates Azure Log Analytics, Sentinel is also the first cloud-native product in the market.
Our objective is to deliver a configurable solution that has the ability to monitor end-to-end processes and take the appropriate action as defined within the system, including those that should be stopped. Many of the current products on the market are SAP-centric but are limited in their integration capabilities. So, we’re customer zero for leveraging Microsoft Sentinel for SAP security and for enabling that cross-correlation capability.
—Aaron Hillard, principal software engineering manager and SAP security lead, Microsoft Digital
“We’re excited to be able to use the capabilities that Sentinel provides our customers out of the box along with SAP specific capabilities on an initiative as important as Microsoft SAP security,” says Yoav Daniely, principal group product manager on the Microsoft Security, Compliance, Identity, and Management (SCIM) team. “This represents a new approach in SIEM solutions.”
To configure Microsoft Sentinel to monitor the entire Microsoft SAP environment—it includes 15 SAP production systems including six Sarbanes-Oxley (SOX) systems—the engineering team and the Microsoft Azure product group recognized that the solution also needed to provide cross-correlation coverage. Cross correlation is the ability to surveil the entire organization to include junctures where SAP integrates with other systems and applications such as Microsoft Dynamics 365. For example, Sentinel could detect a hypothetical scenario in which a user who creates a new payee in Dynamics but also “pays” that customer in SAP without the activity being detected.

“Our objective is to deliver a configurable solution that has the ability to monitor end-to-end processes and take the appropriate action as defined within the system, including those that should be stopped,” says Aaron Hillard, principal software engineering manager and SAP security lead in Microsoft Digital. “Many of the current products on the market are SAP-centric but are limited in their integration capabilities. So, we’re customer zero for leveraging Microsoft Sentinel for SAP security and for enabling that cross-correlation capability.”
Ultimately, the goal is to equip Microsoft Sentinel to assess and respond dynamically to all security threats across all enterprise hosts, platforms, applications, and business processes, and then provide automated remediation as feasible and appropriate. The risk scenarios that Microsoft Sentinel addresses will continue to expand as the product evolves.
“Sentinel gives us the ability to monitor the data and activities holistically, because Microsoft, like many other enterprises, uses numerous systems throughout the operations environment,” Veeranki says. “That’s a key differentiator of Sentinel compared to SIEM systems that are designed purely for SAP.”
Microsoft Sentinel incorporates advanced machine learning and AI capabilities that identify suspicious patterns and activities that previously defied detection. Additionally, it is able to readily integrate numerous platforms and products that enterprise companies use and enable organizations to customize configuration to meet their security-monitoring needs.
Managing massive inputs efficiently with an innovative data connector
To date, the Microsoft SAP and Microsoft Sentinel SAP threat monitoring engineering teams identified an initial 27 initial high-risk scenarios that encompass a broad range of use cases. These use cases involve changes in system, client, or audit-log configuration, and suspicious or unauthorized user logins, data access, or role assignments. Monitoring also covers account-modification or password-change activities, and any audit-log manipulation or brute-force attack, among others. Other risk scenarios are being identified with respect to highly sensitive business and financial threats, and the teams are developing and completing proofs of concept for those scenarios. The SAP and Sentinel teams will continue to expand the threat-detection capabilities of Microsoft Sentinel and the risk scenarios that it addresses the product evolves.
The Microsoft SAP footprint is massive and change management within the platforms is highly complex. Therefore, to prevent system overload because of memory requirements, the engineering team must deploy a robust yet nimble mechanism to accommodate the vast amount of data coming into Microsoft Sentinel. To that end, the engineering team developed a Microsoft Sentinel-specific data connector that manages SAP inputs in a manner that’s specific to the underlying applications. The connector facilitates a complete security solution to visualize, alert, and respond to threats, and it’s easily configurable through built-in watchlists that match specific environment needs.
The data connector extracts data for monitoring, stores it, and then moves it through Sentinel in an incremental manner that the system can “understand,” says Anirudh Dahuja, an SAP platform engineer in Microsoft Digital. “Otherwise, there’s a risk of overloading the system, an issue that we’ve encountered,” he says.
To accomplish efficient use of the new tool, the engineering team used indexing to accommodate unwieldy tables and expedite querying. The team also incorporated secrets connectivity by using the Microsoft Azure Key Vault, which provides a secure store to create, store, and maintain keys that access and encrypt cloud resources, apps, and solutions. To manage the requisite memory optimization, the team leveraged Docker containers to accommodate the data connector functions before moving data into Microsoft Sentinel using custom Microsoft Azure APIs.
There’s another challenge that Microsoft Sentinel engineers are experiencing and working to remedy: how to reduce the “noise” in the monitoring system to differentiate between authorized, permissible activities and real threats that warrant action. Because Sentinel is designed to detect a very broad range of potentially suspicious or intentionally malicious activities, the number of alerts it raised initially produced many false positives.
“That’s something we’re working on now—improving alert fidelity and fine-tuning the system to produce fewer false positives,” Veeranki says.
That’s the biggest advantage of using Sentinel for SAP monitoring—the analytics. There are a lot of other tools in the market that alert you to SAP threats, but that’s where they stop. Microsoft Sentinel offers a scalable cross-platform solution to detect and mitigate threats in near real time. We’re not only detecting threats but also quickly responding to and remediating them.
—Anirudh Dahuja, SAP platform engineer, Microsoft Digital
She adds that Microsoft will continue to share the challenges and remedies that teams discover as the Microsoft Sentinel implementation proceeds. Customers then can accelerate their own implementations by using these learnings.
Tallying early Sentinel benefits and moving forward
Microsoft Sentinel allows for comprehensive cross correlation across enterprise resources, in addition to SAP, thereby helping identify known and previously difficult-to-detect security threats in near real time. That’s a capability high on the wish list for many of Microsoft’s existing enterprise customers. Interestingly, two other critical Sentinel benefits are emerging. Despite the initiative’s early development stage—it’s been less than a year since its inception—Microsoft Sentinel has proved highly scalable and customizable from the outset. It also promises to engender efficiencies generally for Microsoft security operations, by providing a single SIEM system and “pane of glass” through which to continuously view security logs, alerts, and incidents across the enterprise.
Further benefits, still in development, are the advanced analytics being integrated to help detect anomalies in activities involving SAP systems and the automated remediation that Microsoft Sentinel will eventually provide. That’s a winning combination, in Dahuja’s view.
“That’s the biggest advantage of using Sentinel for SAP monitoring—the analytics. There are a lot of other tools in the market that alert you to SAP threats, but that’s where they stop. Microsoft Sentinel offers a scalable cross-platform solution to detect and mitigate threats in near real time,” Dahuja says. “We’re not only detecting threats but also quickly responding to and remediating them.”
- Learn how we’re boosting our response to cybersecurity attacks with Microsoft Sentinel.
- Read how we’re implementing a Zero Trust security model at Microsoft.
- Explore how we’re transforming wired network security with our Security First Initiative.

Want more information? Email us and include a link to this story and we’ll get back to you.




