On July 14, 2021, the National Cybersecurity Center of Excellence1 (NCCoE) at the National Institute of Standards and Technology2 (NIST) hosted a virtual workshop3 to seek feedback from government and industry experts on practical approaches to preventing and recovering from ransomware and other destructive cyberattacks. After we wrote up our feedback for NIST, we realized it would be helpful to share this perspective more broadly to help organizations better protect themselves against the rising tide of (highly profitable) ransomware attacks. While ransomware and extortion attacks are still evolving rapidly, we want to share a few critical lessons learned and shed some light on common misconceptions about ransomware attacks.
Clarifying attack terminology and scope
One common misconception about ransomware attacks is that they only involve ransomware—”pay me to get your systems and data back”—but these attacks have actually evolved into general extortion attacks. While ransom is still the main monetization angle, attackers are also stealing sensitive data (yours and your customers’) and threatening to disclose or sell it on the dark web or internet (often while holding onto it for later extortion attempts and future attacks).
We’re also seeing a widespread perception that ransomware is still constrained to basic cryptolocker style attacks, first seen in 2013, that only affect a single computer at a time (also known as the commodity model). Today’s attackers have evolved far beyond this—using toolkits and sophisticated affiliate business models to enable human operators to target whole organizations, deliberately steal admin credentials, and maximize the threat of business damage to targeted organizations. The ransomware operators often buy login credentials to organizations from other attack groups, rapidly turning what seems like low-priority malware infections into significant business risks.
Simple, prioritized guidance
We’ve also seen that many organizations still struggle with where to start, especially smaller operations with limited staff and experience. We believe all organizations should begin with simple and straightforward prioritization of efforts (three steps) and we have published this, along with why each priority is important.
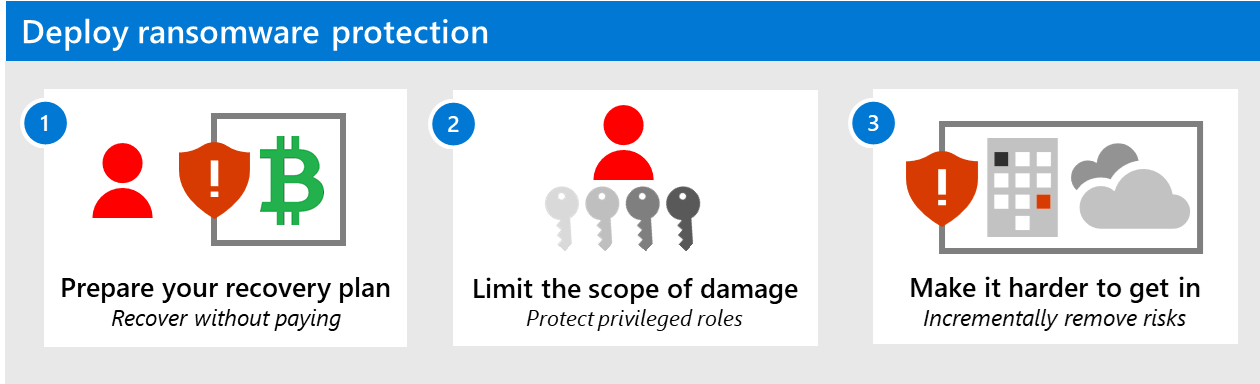
Figure 1: Recommended mitigation prioritization.
Create detailed instructions
Microsoft has also found that many organizations struggle with the next level of the planning process. As a result, we built guidance to make following these steps as clear and easy as possible. Microsoft already works with NIST NCCoE on several efforts, including the Zero Trust effort, which supports Presidential Executive Order (EO) 14028 on Improving the Nation’s Cybersecurity. We welcome the opportunity for any additional ransomware-related work by providing clarifying guidance using whatever tools and technologies organizations have available.
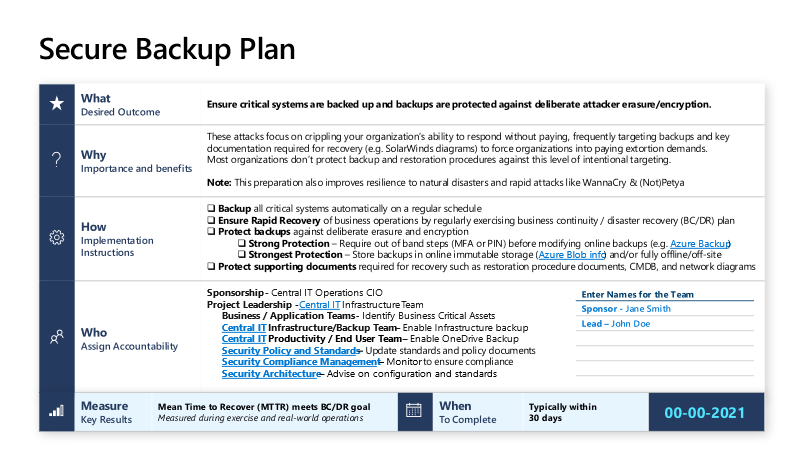
Figure 2: Secure backup instructions from Microsoft’s human-operated ransomware page.
Microsoft’s recommended mitigation prioritization
Based on our experience with ransomware attacks, we’ve found that prioritization should focus on these three steps: prepare, limit, and prevent. This may seem counterintuitive since most people want to simply prevent an attack and move on. But the unfortunate truth is that we must assume breach (a key Zero Trust principle) and focus on reliably mitigating the most damage first. This prioritization is critical because of the high likelihood of a worst-case scenario with ransomware. While it’s not a pleasant truth to accept, we’re facing creative and motivated human attackers who are adept at finding a way to control the complex real-world environments in which we operate. Against that reality, it’s important to prepare for the worst and establish frameworks to contain and prevent attackers’ abilities to get what they’re after.
While these priorities should govern what to do first, we encourage organizations to run as many steps in parallel as possible (including pulling quick wins forward from step three whenever you can).
Step 1. Prepare a recovery plan: Recover without paying
- What: Plan for the worst-case scenario and expect that it will happen at any level of the organization.
- Why: This will help your organization:
- Limit damage for the worst-case scenario: Restoring all systems from backups is highly disruptive to business, but it’s still more efficient than trying to do recovery using low-quality attacker-provided decryption tools after paying to get the key. Remember: paying is an uncertain path; you have no guarantee that the attackers’ key will work on all your files, that the tools will work effectively, or the attacker—who may be an amateur using a professional’s toolkit—will act in good faith.
- Limit the financial return for attackers: If an organization can restore business operations without paying, the attack has effectively failed and resulted in zero return on investment for the attackers. This makes it less likely they will target your organization again in the future (and deprives them of funding to attack others). Remember: attackers may still attempt to extort your organization through data disclosure or abusing/selling the stolen data, but this gives them less leverage than possessing the only means of accessing your data and systems.
- How: Organizations should ensure they:
- Register risk. Add ransomware to the risk register as a high-likelihood and high-impact scenario. Track mitigation status via your Enterprise Risk Management (ERM) assessment cycle.
- Define and backup critical business assets. Automatically back up critical assets on a regular schedule, including correct backup of critical dependencies, such as Microsoft Active Directory.
- Protect backups. To safeguard against deliberate erasure and encryption, use offline storage, immutable storage, and/or out-of-band steps (multifactor authentication or PIN) before modifying or erasing online backups.
- Test ‘recover from zero’ scenario. Ensure that your business continuity and disaster recovery (BC/DR) can rapidly bring critical business operations online from zero functionality (all systems down). Conduct practice exercises to validate cross-team processes and technical procedures, including out-of-band employee and customer communications (assume all email and chat are down). Important: protect (or print) supporting documents and systems required for recovery, including restoration-procedure documents, configuration management databases (CMDBs), network diagrams, and SolarWinds instances. Attackers regularly destroy these documents.
- Reduce on-premises exposure. Move data to cloud services with automatic backup and self-service rollback.
Step 2. Limit the scope of damage: Protect privileged roles (starting with IT admins)
- What: Ensure you have strong controls (prevent, detect, respond) for privileged accounts, such as IT admins and other roles with control of business-critical systems.
- Why: This slows or blocks attackers from gaining complete access to steal and encrypt your resources. Taking away the attacker’s ability to use IT admin accounts as a shortcut to resources will drastically lower the chances that they’ll be successful in controlling enough resources to impact your business and demand payment.
- How: Enable elevated security for privileged accounts—tightly protect, closely monitor, and rapidly respond to incidents related to these roles. See Microsoft’s recommended steps that:
- Cover end-to-end session security (including multifactor authentication for admins).
- Protect and monitor identity systems.
- Mitigate lateral traversal.
- Promote rapid threat response.
Step 3. Make it harder to get in: Incrementally remove risks
- What: Prevent a ransomware attacker from entering your environment, as well as rapidly respond to incidents and remove attacker access before they can steal and encrypt data.
- Why: This causes attackers to fail earlier and more often, undermining their profits. While prevention is the preferred outcome, it may not be possible to achieve 100 percent prevention and rapid response across a real-world organization with a complex multi-platform, multi-cloud estate and distributed IT responsibilities.
- How: Identify and execute quick wins that strengthen security controls to prevent entry and rapidly detect and evict attackers, while implementing a sustained program that helps you stay secure. Microsoft recommends following the principles outlined in the Zero Trust strategy. Against ransomware, organizations should prioritize:
- Improving security hygiene by reducing the attack surface and focusing on vulnerability management for assets in their estate.
- Implementing protection, detection, and response controls for digital assets, as well as providing visibility and alerting on attacker activity while responding to active threats.
The takeaway
To counter the threat of ransomware, it’s critical to identify, secure, and be ready to recover high-value assets—whether data or infrastructure—in the likely event of an attack. This requires a sustained effort involving obtaining buy-in from the top level of your organization (like the board) to get IT and security stakeholders working together asking nuanced questions. For example, what are the critical parts of the business that could be disrupted? Which digital assets map to these business segments (files, systems, databases)? How can we secure these assets? This process may be challenging, but it will help set up your organization to make impactful changes using the steps recommended above.
To learn more, visit our page on how to rapidly protect against ransomware and extortion.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
1National Cybersecurity Center of Excellence.
2National Institute of Standards and Technology, US Department of Commerce.
3Virtual Workshop on Preventing and Recovering from Ransomware and Other Destructive Cyber Events, National Cybersecurity Center of Excellence, 14 July 2021.








