Microsoft is proud to promote Cybersecurity Awareness Month as part of our ongoing commitment to security for all. Year-round, Microsoft tracks nation-state threat activities to help protect organizations and individuals from these advanced persistent actors. We’re constantly improving our capabilities to bring better detections, threat context, and actor knowledge to our customers so they can improve their own defenses. To learn more about how Microsoft responds to nation-state attacks and how to defend your organization, watch the Decoding NOBELIUM docuseries. Hear directly from the frontline defenders who helped protect organizations against the most sophisticated attack in history.
The aims of nation-state cyber actors—largely espionage and disruption—remain consistent, along with their most reliable tactics and techniques: credential harvesting, malware, and VPN exploits. However, a common theme this year among the actors originating from China, Russia, North Korea, and Iran has been increased targeting of IT service providers as a way of exploiting downstream customers.1
Earlier this month, we published the 2021 Microsoft Digital Defense Report (MDDR), which provides more in-depth findings about Microsoft’s tracking of nation-state threat groups, including information on the most heavily targeted sectors and countries, specific threat actors, attack methods, and more. This blog captures the high-level themes from the MDDR, and we encourage you to download the full report for additional details.
Government agencies and non-governmental organizations are favored targets
Whenever an organization or individual account holder is targeted or compromised by observed nation-state activities, Microsoft delivers a nation-state notification (NSN) directly to that customer to give them the information they need to investigate the activity. Over the past three years, we’ve delivered over 20,500 NSNs. According to the analysis of the actor activity behind these NSNs, nation-state attacks in the past year have largely focused on operational objectives of espionage and intelligence collection rather than destructive attacks.
“Nation-state activity spans nearly every industry sector and geographic region. In other words, protections against these tactics are critical for every organization and individual.”—2021 Microsoft Digital Defense Report.
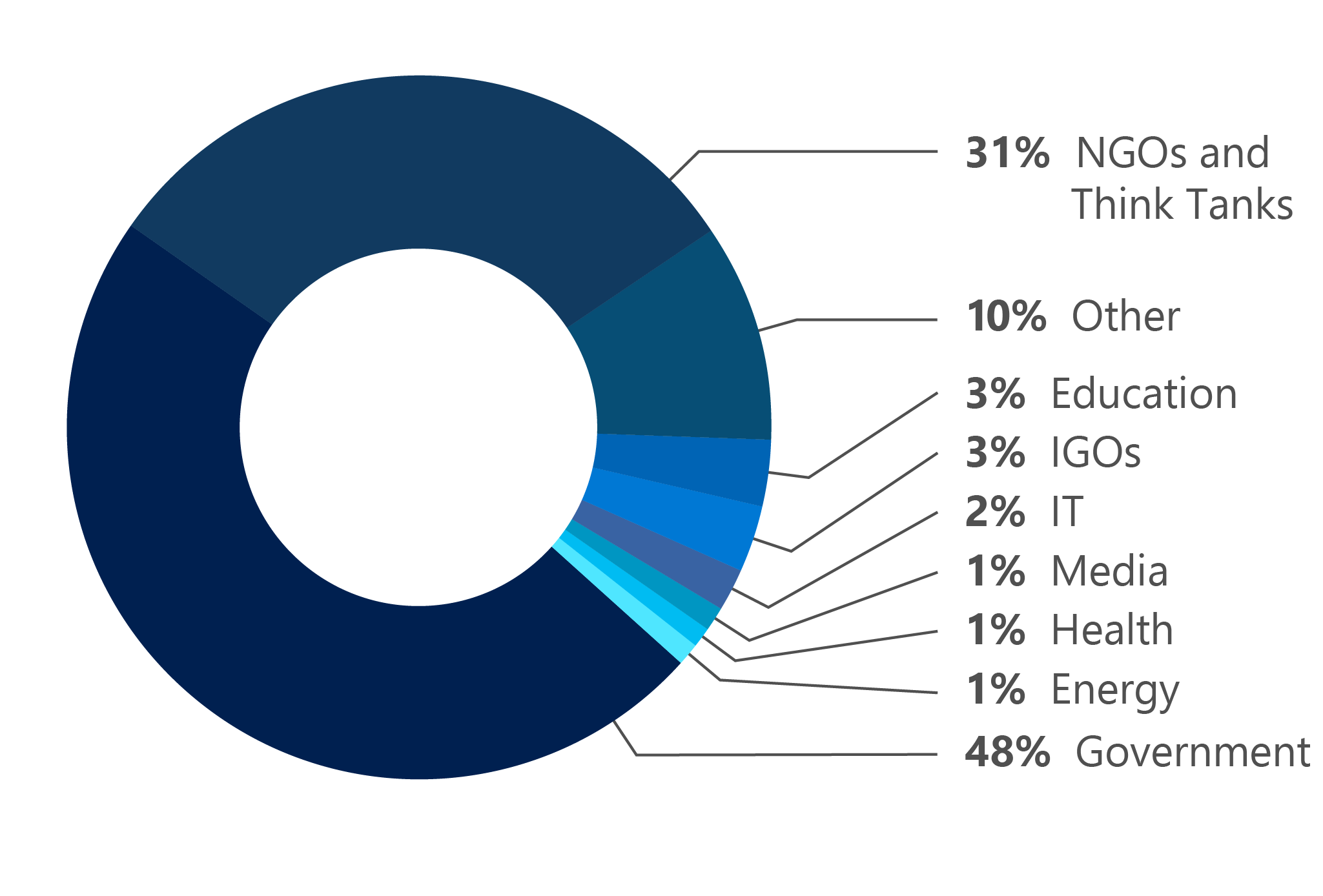
The Microsoft Threat Intelligence Center (MSTIC) and the Microsoft Digital Crimes Unit (DCU) have observed that nearly 80 percent of nation-state attacks were directed against government agencies, think tanks, and non-government organizations (NGOs). The nation-state groups we refer to as NOBELIUM, NICKEL, THALLIUM, and PHOSPHORUS were the most active against the government sector, targeting mostly government entities involved in international affairs.
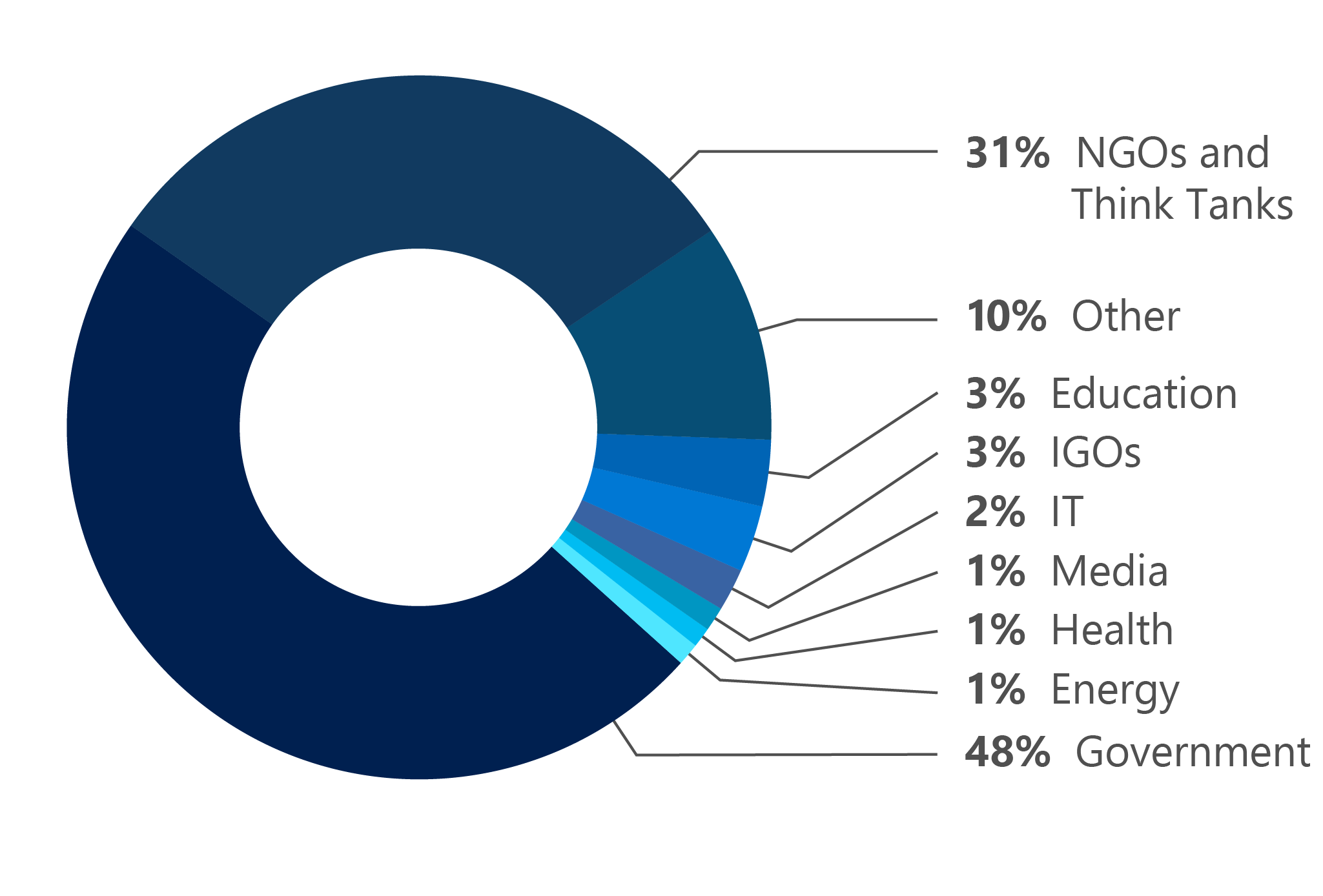
Figure 1: Sectors targeted by nation-state attacks (July 2020 to June 2021).
Russia-based cyber attackers in particular have increasingly set their sights on government targets. Year-on-year comparisons of NSN data depict a marked increase in successful compromises, from a 21 percent success rate between July 2019 and June 2020, up to 32 percent since July 2020. In turn, the percentage of government organizations targeted by Russian threat actors exploded from roughly 3 percent last year, to 53 percent since July 2020 (see figure 3).
Most-targeted countries
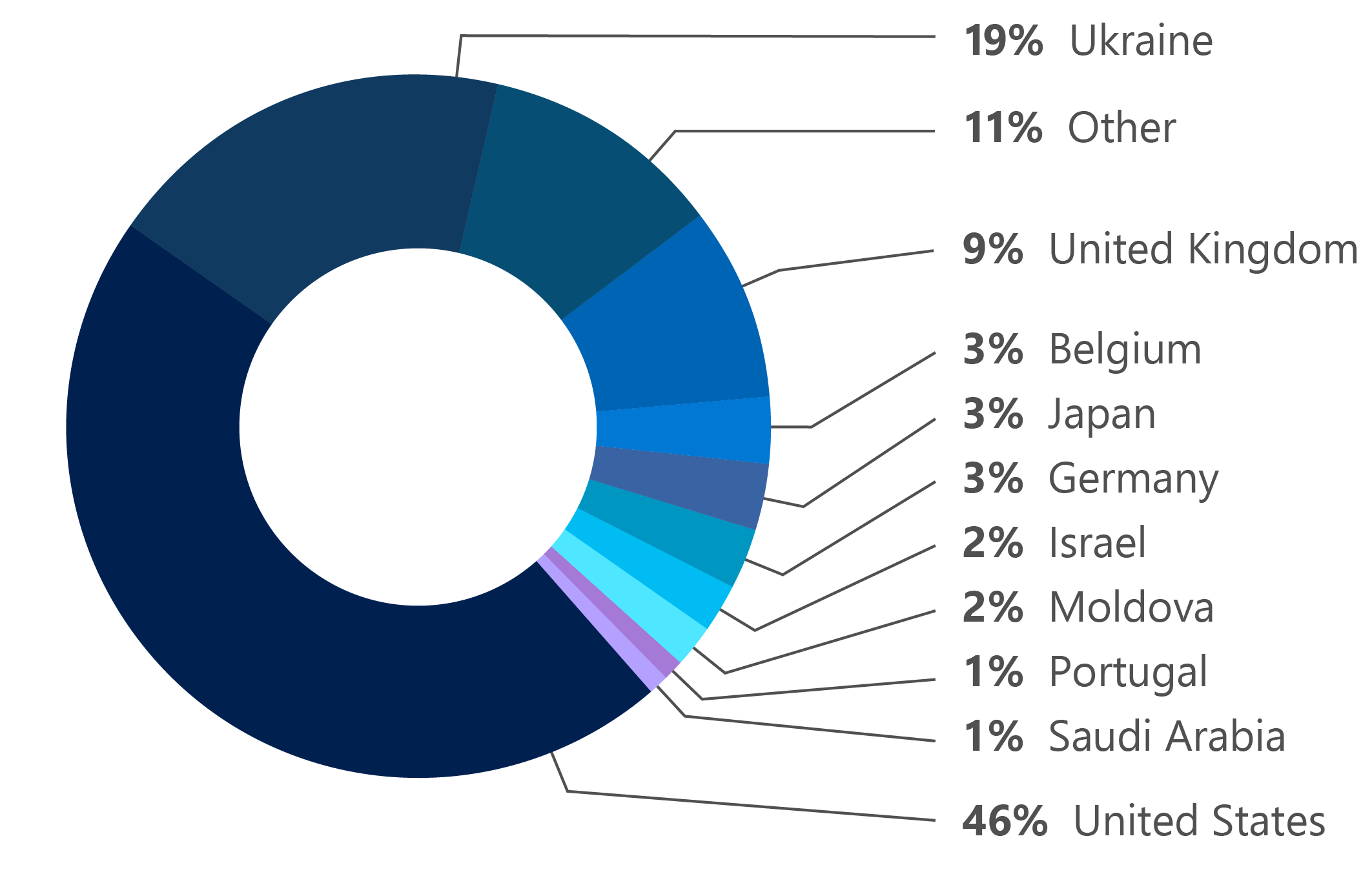
The United States remained the most highly targeted country in the past year. Russia-based NOBELIUM also heavily targeted Ukraine, particularly focusing on government interests involved in rallying against a build-up of Russian troops along Ukraine’s border—driving the number of Ukrainian customers impacted from 6 last year to more than 1,200 this year. This past year also saw a near quadrupling in the targeting of Israeli entities, driven exclusively by Iranian actors as tensions escalated between the two countries.
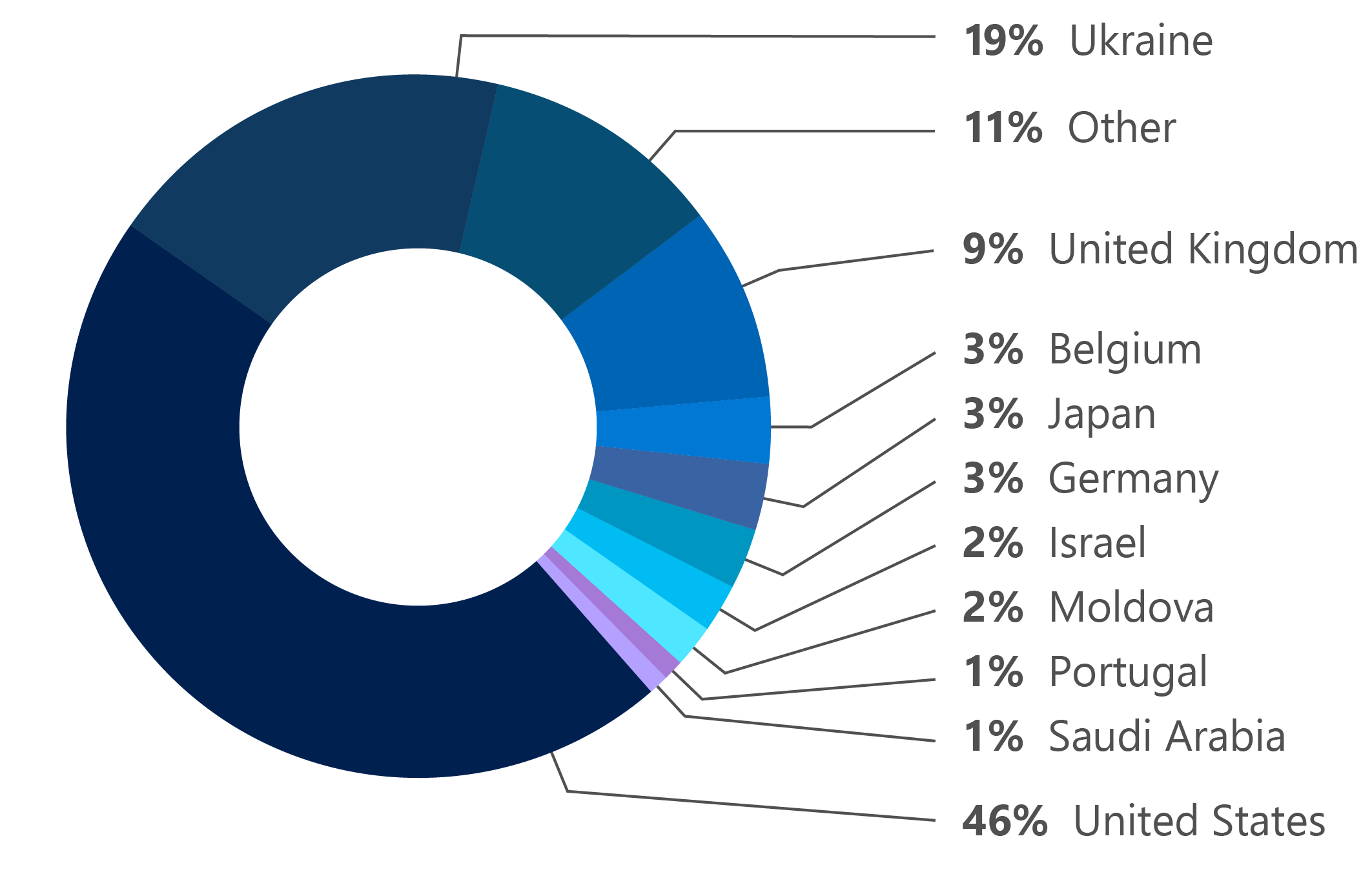
Figure 2: Countries most targeted (July 2020 to June 2021).
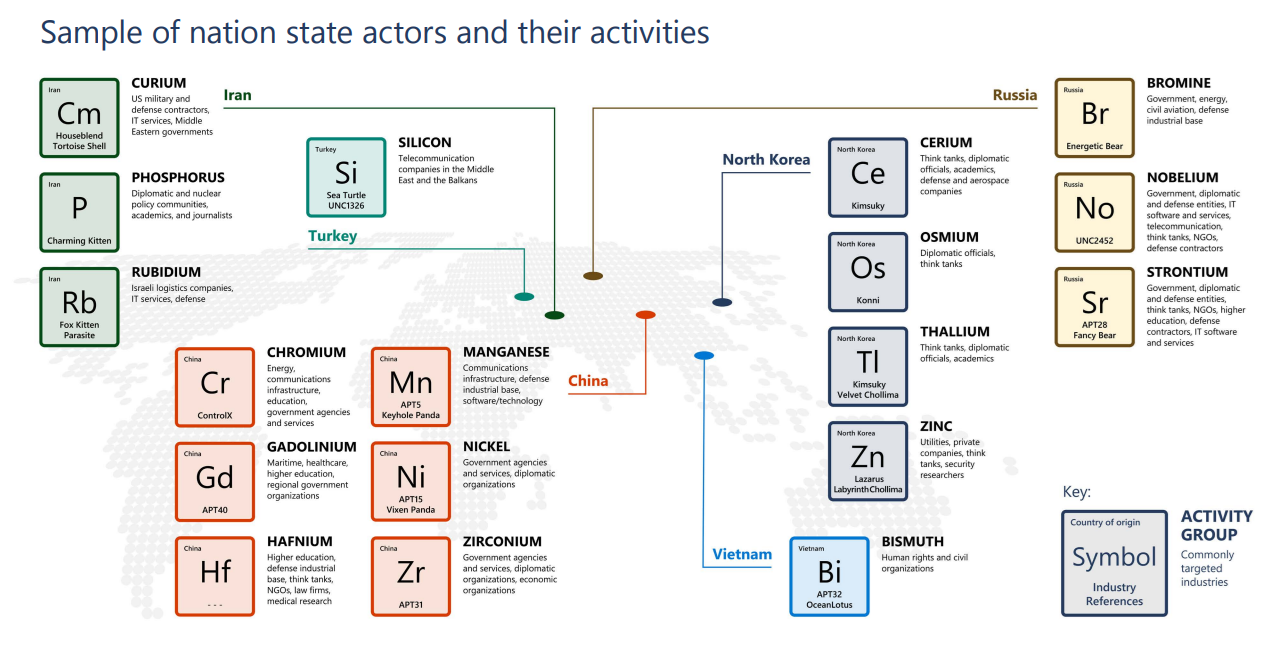
Microsoft identifies nation-state activities by chemical element names, some of which are shown in the table below, along with their countries of origin. This small sample of the total nation-state actors tracked by Microsoft represents several of the most active in the last year.
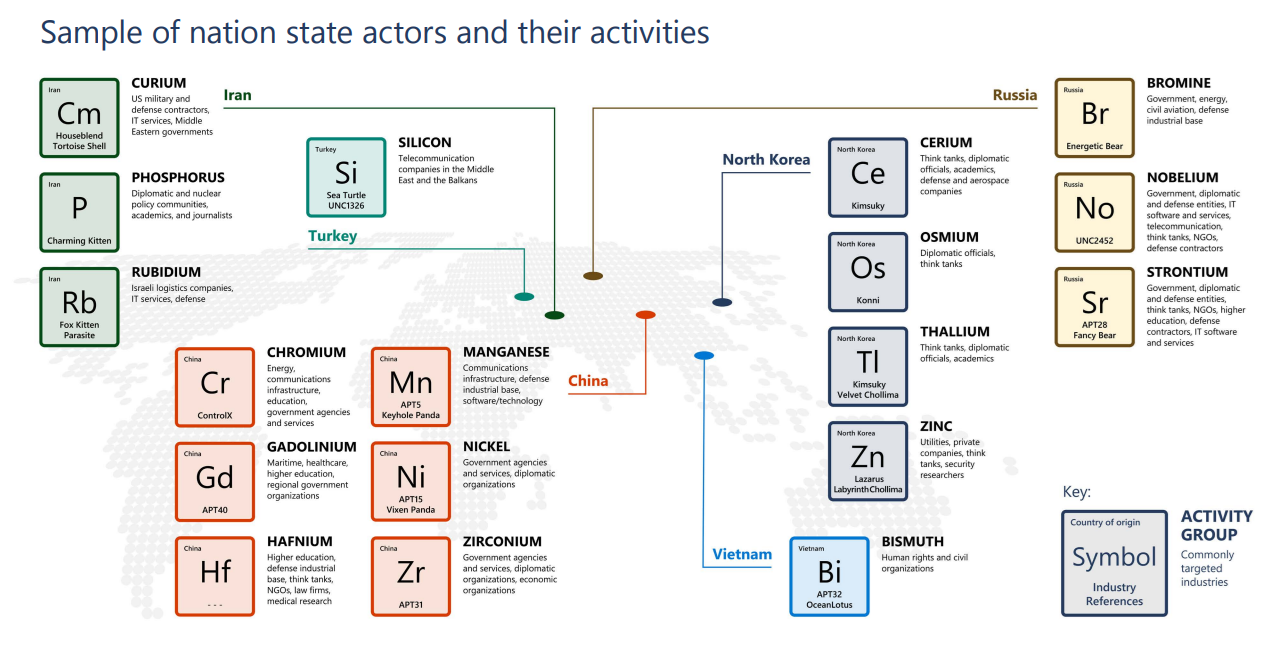
Figure 3: Reference map for nation-state actors.
Volume versus precision
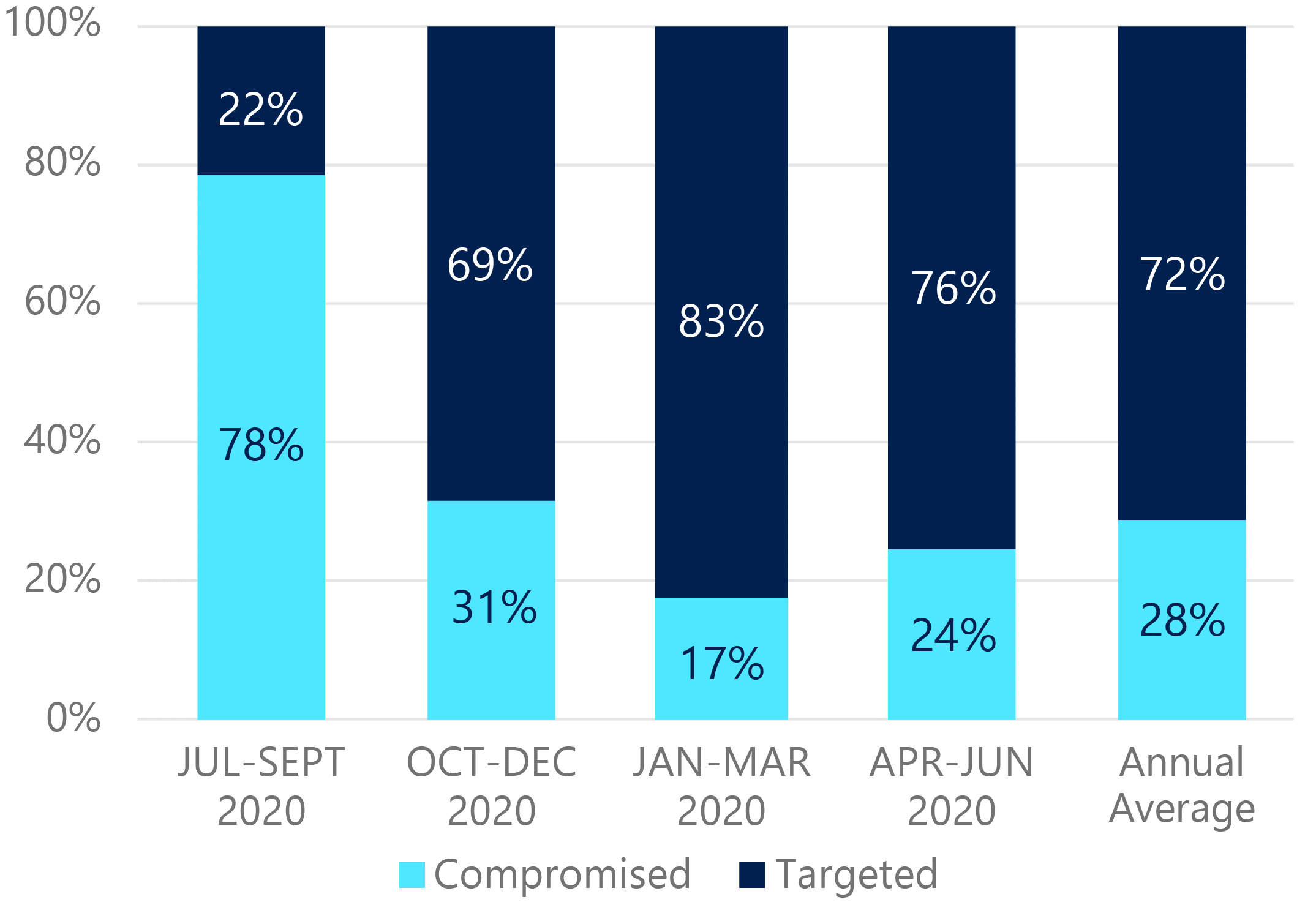
Rates of successful compromises varied widely among threat groups this year. Some, such as North Korea-based THALLIUM, had a low rate of successful compromise likely because their common tactic of large-scale spear-phishing campaigns has become easier to detect and deter as users become increasingly aware of these lures and organizations use security solutions to detect them more effectively. Russia-based NOBELIUM, in contrast, had more successful compromises as a result of their more targeted attack against software supply chains coupled with more high-volume password spray campaigns in pursuit of credential theft. Nation-state actors appear to be increasing the scale of these blunt attacks in an attempt to evade detection and improve their chances of a successful breach. The first fiscal quarter of 2020 (July to September) saw a proportionally higher compromise rate; not necessarily because threat actors were more successful, but because we saw fewer high-volume campaigns during this time.
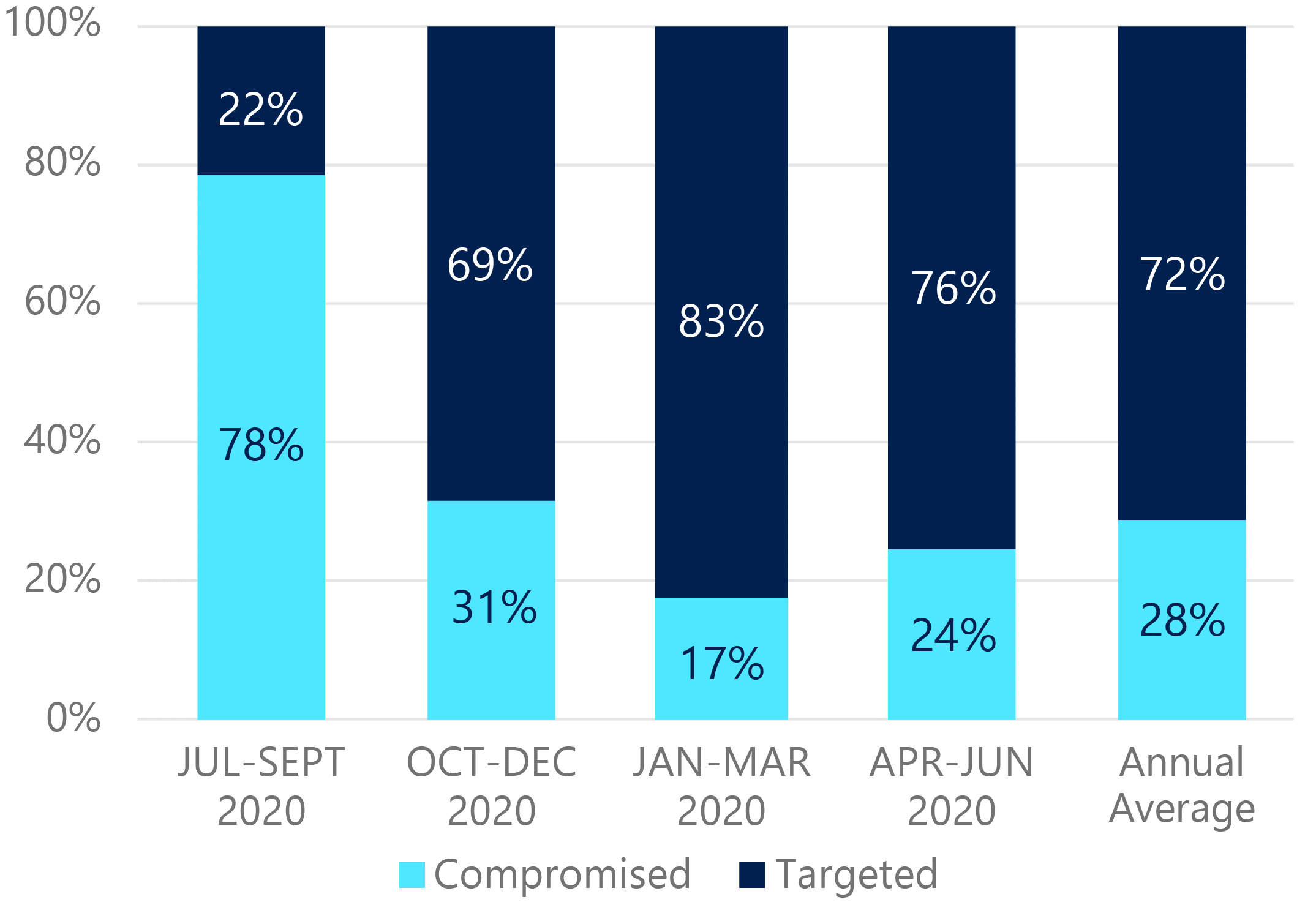
Figure 4: Average rates of compromise (all tactics, July 2020 to June 2021).
Snapshot: Nation-state activity
Russia
Russia-based NOBELIUM proved how insidious software supply chain attacks can be with its devastating compromise of the SolarWinds Orion software update.2 Although the group limited its follow-up exploitation to approximately 100 organizations, its backdoor malware was pushed to roughly 18,000 entities worldwide. In other incidents, NOBELIUM has employed password spray and phishing attacks to compromise third-party providers and facilitate future compromises. This threat actor targeted cloud solution providers (CSPs) and leveraged the backdoor to steal a Mimecast private key.3 Get the full account from world-class defenders on what it took to respond to the most advanced nation-state attack in history by watching the Decoding NOBELIUM docuseries.
China
Chinese nation-state threat actors have been targeting the United States political landscape for insight into policy shifts. In early March 2021, Microsoft blogged about HAFNIUM and the detection of multiple zero-day exploits used to attack on-premises versions of Microsoft Exchange Server. HAFNIUM operates primarily from leased virtual private servers in the United States and targets entities across a number of industry sectors, including infectious disease researchers, law firms, higher education institutions, defense contractors, policy think tanks, and NGOs.
Iran
Iran continued its streak of destructive cyberattacks against regional adversaries, including a string of ransomware attacks against Israeli entities. Iran-linked threat actor RUBIDIUM has been implicated in the Pay2Key4 and N3tw0rm5 ransomware campaigns that targeted Israel in late 2020 and early 2021. A common element in Iranian nation-state cyberattacks was the targeting of Israeli logistics companies involved in maritime transportation. Despite Tehran’s less aggressive approach toward the United States in the wake of last year’s election, United States entities remained Iranian threat actors’ top target, comprising nearly half of the NSNs Microsoft delivered to cloud-service customers.
North Korea
Just over half the NSNs Microsoft issued were for North Korea-based state actors during the last three months of 2020. The majority of the North Korean targeting was directed at consumer account targets, based on the likelihood of obtaining non-publicly available diplomatic or geopolitical intelligence. As Microsoft reported in November 2020, ZINC and CERIUM targeted pharmaceutical companies and vaccine researchers in several countries, probably to speed up North Korea’s own vaccine research. North Korea also continued to target financial companies with the intent of stealing cryptocurrency and intellectual property.6
Private sector actors supply the tools
Though not nation-state actors themselves, private sector offensive actors (PSOAs) create and sell malicious cyber technologies to nation-state buyers. PSOA tools have been observed targeting dissidents, human rights defenders, journalists, and other private citizens. In December 2020, Microsoft’s efforts to protect our customers led us to file an amicus brief in support of WhatsApp’s case against Israel-based NSO Group Technologies.7 The brief asks the court to reject NSO Group’s position that it’s not responsible for the use of its surveillance and espionage products by governments. Microsoft also worked with Citizen Lab to disable malware used by Israel-based PSOA, SOURGUM (aka Candiru), which created malware and zero-day exploits (fixed in CVE-2021-31979 and CVE-2021-33771) as a part of a hacking-as-a-service package sold to government agencies and other malicious actors.
Comprehensive protection starts with individuals
One thing is clear: nation-state actors are well-funded and employ techniques of tremendous breadth and sophistication. More than other adversaries, nation-state attackers will also target individuals specifically for access to their connections, communications, and information. These attackers are constantly refining their tactics and techniques; therefore, defense-in-depth strategies should include educating employees on how to avoid being targeted themselves. Most importantly, applying Zero Trust principles across corporate resources helps secure today’s mobile workforce—protecting people, devices, applications, and data no matter their location or the scale of threats faced.
Learn more
For a deep dive into our latest information on nation-state threats, download the 2021 Microsoft Digital Defense Report and watch the Decoding NOBELIUM docuseries. Also, look for more blog posts providing information for each themed week of Cybersecurity Awareness Month 2021. Read our latest posts:
Be sure to visit our Cybersecurity Awareness Month page for links to additional resources and information on protecting your organization year-round. Do your part. #BeCyberSmart
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
1Awareness Briefing: Chinese Cyber Activity Targeting Managed Service Providers, Cybersecurity Infrastructure Security Agency.
2A ‘Worst Nightmare’ Cyberattack: The Untold Story Of The SolarWinds Hack, Monika Estatieva, NPR. 16 April 2021.
3Mimecast attributes supply chain attack to SolarWinds’ hackers, David Jones, Cybersecurity Dive. 14 January 2021.
4Pay2Key Ransomware Joins the Threat Landscape, Tomas Meskauskas, Security Boulevard. 30 November 2020.
5N3TW0RM ransomware emerges in wave of cyberattacks in Israel, Lawrence Abrams, Bleeping Computer. 2 May 2021.
6North Korean hackers charged in massive cryptocurrency theft scheme, Dan Mangan, CNBC. 17 February 2021.
7Google, Cisco and VMware join Microsoft to oppose NSO Group in WhatsApp spyware case, Zack Whittaker, Tech Crunch. 21 December 2020.