The “Top 10 actions to secure your environment” series outlines fundamental steps you can take with your investment in Microsoft 365 security solutions. In “Step 6. Manage mobile apps,” you’ll learn how to complete your Unified Endpoint Management (UEM) strategy by using Microsoft Intune Mobile Application Management (MAM).
In our last blog, Step 5. Set up mobile device management, we introduced ContosoCars to illustrate the journey of implementing Intune as part of your UEM strategy. We continue their story to demonstrate how you can enhance endpoint security by managing mobile apps and tracking the deployment.
You will recall from our last post that ContosoCars already defined their scenarios and requirements, set their mobile device management (MDM) authority to Intune, and set up configuration policies to enroll their Windows 10 and other mobile devices (Figure 1).

Figure 1. ContosoCars defined Intune use case scenarios and requirements.
Protect sensitive data within apps
ContosoCars corporate and sales employees use their personal phones and tablets, which creates risk of data leakage.
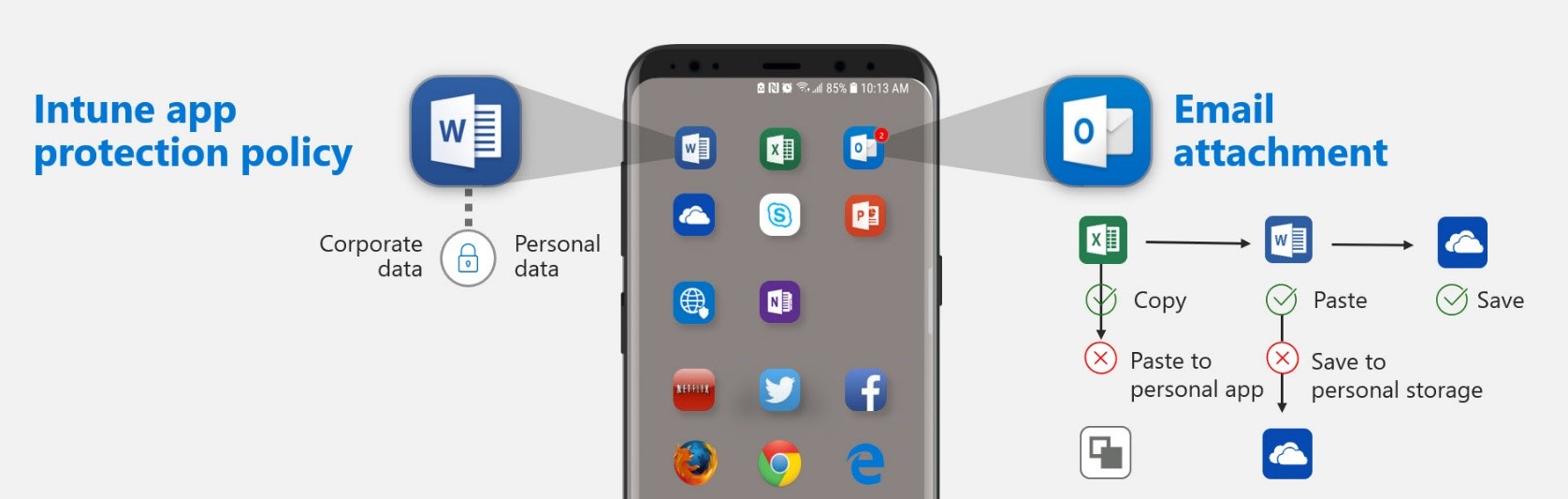
To protect company data that is accessed from devices that are not managed by the company, ContosoCars will use Intune app protection policies, which can apply to apps even if the devices are not managed by Intune. ContosoCars can create and assign app protection policies to policy-managed apps, which include a piece of Intune code, to enforce data protection policies (Figure 2).
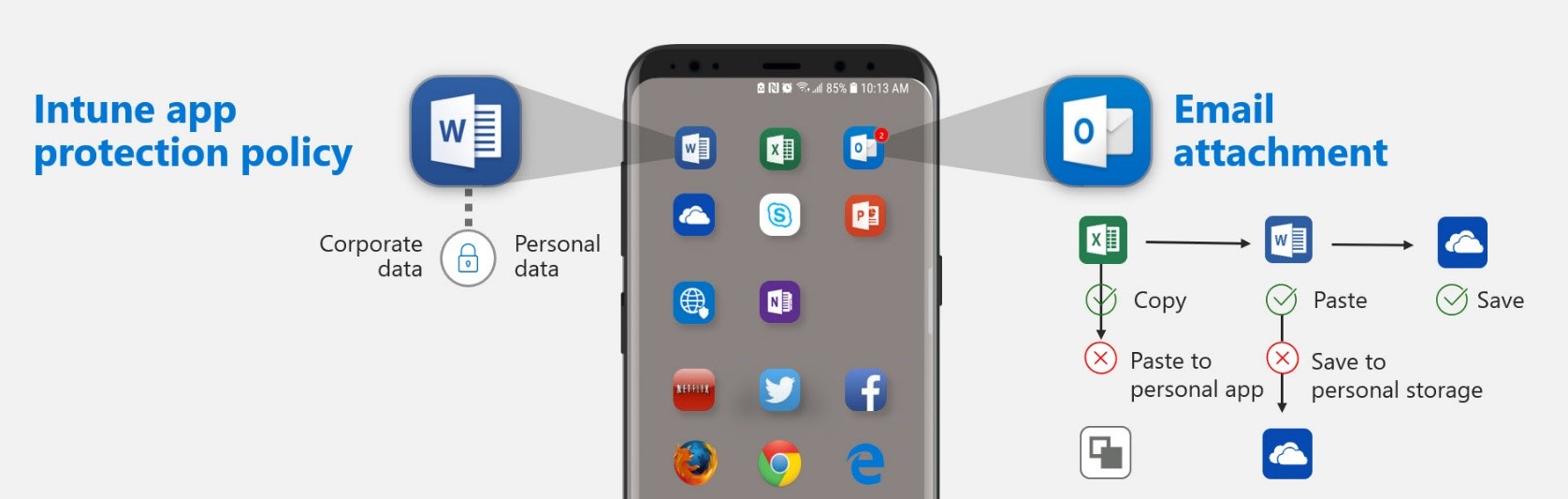
Figure 2. Data protection with app protection policies.
For example, an app protection policy can ensure that corporate data can only be saved to OneDrive for Business and SharePoint, and not to local storage. This prevents data leakage to unsecured, consumer cloud storage services and remains encrypted in the event of device loss (Figure 3).

Figure 3. App protection policy restricting cut, copy, and paste.
Protect customer data on unmanaged devices
Unlike the employee devices, ContosoCars does not enroll or manage the devices used by their franchisee technicians. To deliver the best customer experience, the technicians need real-time customer data on their tablets when they are working on the shop floor. Intune app protection policies work even if the devices are not enrolled in Intune.
ContosoCars can use Intune’s MAM to deliver and manage approved corporate apps on the technicians tablets, apply required app protection policies to protect the data, and selectively wipe the data if required so only the “managed apps and data” are removed, keeping the franchisee’s other data intact on the devices. They can also restrict data movement to apps that aren’t protected by app protection policies, while allowing data to be easily shared within policy-managed apps.
ContosoCars can enforce an app-level PIN and configure the app to launch only if the device-health meets the access requirements. Since they cannot ensure the tablets are kept in a secure location and cannot control OS upgrades and security updates to the device, they can ensure that the customer data is only available when authorized users enter the PIN. Access will be blocked upon multiple tries and a PIN will be required after a certain period of inactivity. This allows ContosoCars to maintain their high customer service standards at their franchise showrooms (Figure 4).

Figure 4. Customers can use an app-level PIN to restrict access to a specific app.
Strengthen Intune security with Microsoft 365 integration
Using Microsoft 365, ContosoCars benefits from security beyond device and app management. Intune integration with Azure Information Protection ensures that if franchise sales staff shares sensitive data with users outside the company, unauthorized users will be blocked from accessing it. Azure Active Directory conditional access policies allow only policy-managed apps access to Exchange online and other Office 365 services. This can prevent an unsecure email app on a mobile device from being exploited by a malicious attacker to gain access to the entire network.
Track and monitor your Intune deployment
Intune provides several ways that you can monitor your deployment. User group views, built-in reports and in-console alerts allow you to track how many users have enrolled devices after each phase of your rollout, so that you can:
- Evaluate the effectiveness of your communication plan.
- Estimate the impact of enforcing conditional access policies.
Learn more
Check back in a few weeks for our next blog post, “Step 7. Set up cloud discovery,” where we’ll discuss how you can discover apps in use, assess risk from those apps, and identify vulnerabilities.
Get deployment help now
FastTrack for Microsoft 365 provides end-to-end guidance to set up your security products. FastTrack is a deployment and adoption service that comes at no charge with your subscription. Get started at FastTrack for Microsoft 365.
Resources