Microsoft Security Blog
Your source for the latest in cybersecurity

Applying security fundamentals to AI: Practical advice for CISOs
Read actionable advice for CISOs on securing AI, managing risk, and applying core security principles in today’s AI‑powered environment.
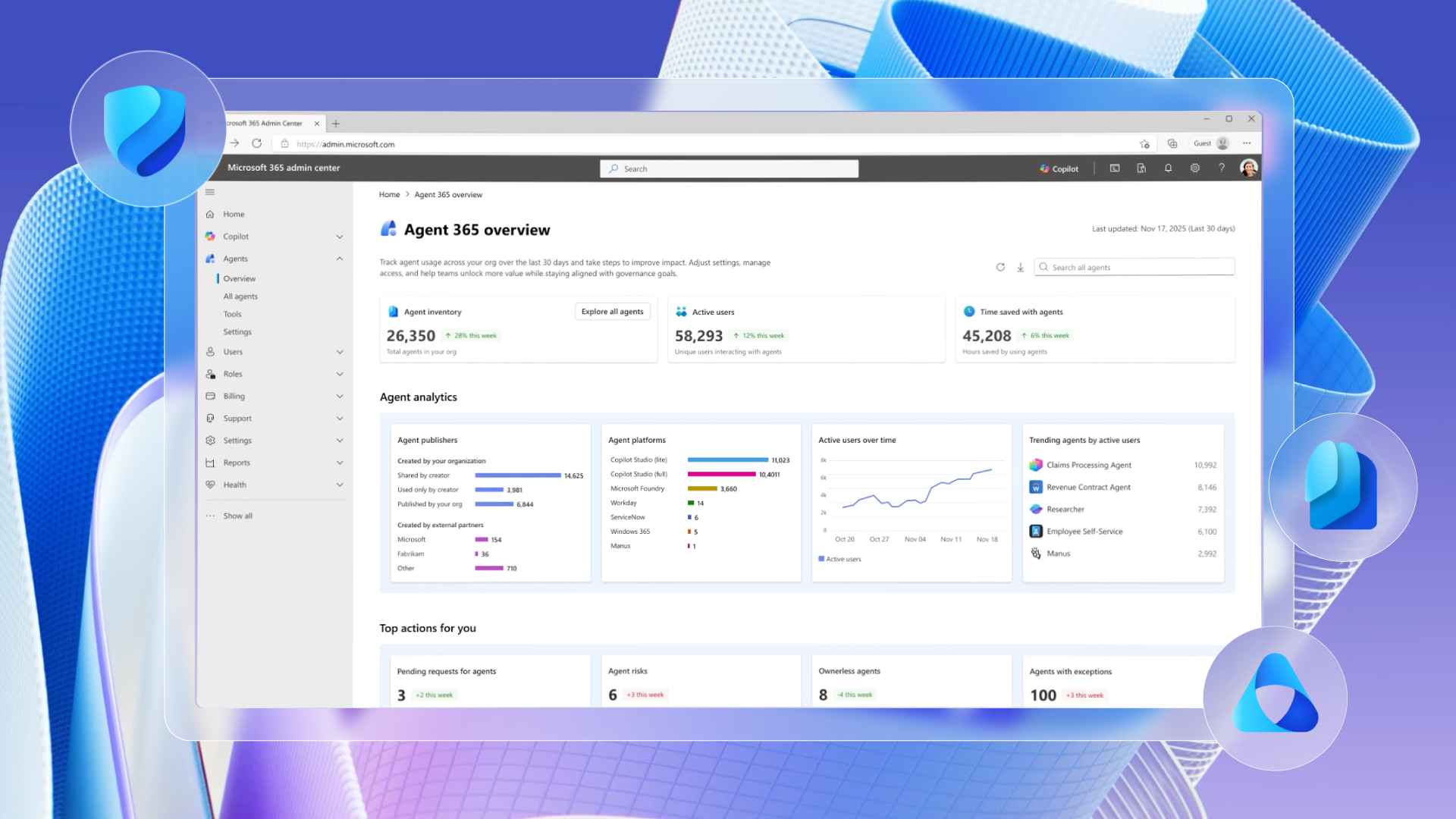
Secure agentic AI for your Frontier Transformation
We are announcing the next step to make Frontier Transformation real for customers across every industry with Wave 3 of Microsoft 365 Copilot, Microsoft Agent 365, and Microsoft 365 E7: The Frontier Suite.

Mitigating the Axios npm supply chain compromise
On March 31, 2026, the popular HTTP client Axios experienced a supply chain attack, causing two newly published npm packages for version updates to download from command and control (C2) that Microsoft Threat Intelligence has attributed to the North Korean state actor Sapphire Sleet.
Stay ahead of threats
Get expert insights, threat intelligence, and the latest cybersecurity reports from Security Insider.
AI and machine learning
-

Threat actor abuse of AI accelerates from tool to cyberattack surface
Generative AI is upgrading cyberattacks, from 450% higher phishing click‑through rates to industrialized MFA bypass. -

Applying security fundamentals to AI: Practical advice for CISOs
Read actionable advice for CISOs on securing AI, managing risk, and applying core security principles in today’s AI‑powered environment. -

Addressing the OWASP Top 10 Risks in Agentic AI with Microsoft Copilot Studio
Agentic AI introduces new security risks.
Modernize your security operations center
Confidently secure your multicloud, multiplatform environment with Microsoft Sentinel – a cloud-native security information and event management (SIEM) solution.
Latest posts
-

Inside an AI‑enabled device code phishing campaign
A new wave of device code phishing shows how threat actors are scaling account compromise using AI and end‑to‑end automation. -

Storm-1175 focuses gaze on vulnerable web-facing assets in high-tempo Medusa ransomware operations
The financially motivated cybercriminal threat actor Storm-1175 operates high-velocity ransomware campaigns that weaponize recently disclosed vulnerabilities to obtain initial access, exfiltrate data, and deploy Medusa ransomware. -

Threat actor abuse of AI accelerates from tool to cyberattack surface
Generative AI is upgrading cyberattacks, from 450% higher phishing click‑through rates to industrialized MFA bypass. -

Cookie-controlled PHP webshells: A stealthy tradecraft in Linux hosting environments
Cookie-gated PHP webshells use obfuscation, php-fpm execution, and cron-based persistence to evade detection in Linux hosting environments. -

Mitigating the Axios npm supply chain compromise
On March 31, 2026, the popular HTTP client Axios experienced a supply chain attack, causing two newly published npm packages for version updates to download from command and control (C2) that Microsoft Threat Intelligence has attributed to the North Korean state actor Sapphire Sleet. -

The threat to critical infrastructure has changed. Has your readiness?
Five facts critical infrastructure (CI) leaders need to act on in 2026, grounded in what Microsoft Threat Intelligence is observing across sectors right now.


