This post is authored by Milad Aslaner, Senior Program Manager, Windows & Devices Group.
A decade ago, most cyber-attacks started with a piece of malware or a complex method to directly attack the infrastructure of a company. But this picture has changed and today all it takes is a sophisticated e-mail phishing for an identity.

Figure 1: Trying to identify a loophole in the complex infrastructure
Digitalization is happening and there is no way around it. It’s a necessity for all industries and a natural evolutionary step in society. It’s not about when or if digital transformation is happening, but how. Our Microsoft security approach is targeted to enable a secure digital transformation. We achieve that by enabling our customers to protect, detect and respond to cybercrime.
The art of social engineering is nothing new itself and was already present in the age where broadband connections didn’t even exist. At that time, we used to call these kinds of threat actors not hackers but con men. Frank Abagnale, Senior Consultant at Abagnale & Associates once said “In the old days, a con man would be good looking, suave, well dressed, well-spoken and presented themselves really well. Those days are gone because it’s not necessary. The people committing these crimes are doing them from hundreds of miles away.”
Threat actor groups such as STRONTIUM are nothing else than a group of modern con men. They follow the same approach as traditional con men, but they do it in the digital world. They prefer this approach because it has become easier to send a sophisticated phishing email than to find a new loophole or vulnerability allowing them to access critical infrastructure directly.
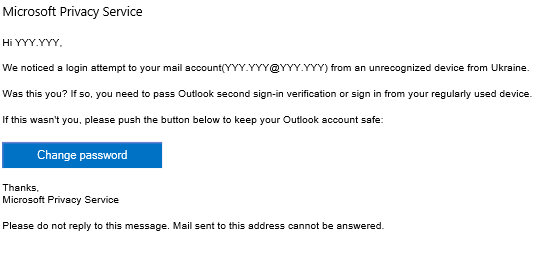
Figure 2: Example of a STRONTIUM phishing email
Keith A. Rhodes, Chief Technologist at the U.S. General Account Office says, “There’s always the technical way to break into a network but sometimes it’s easier to go through the people in the company. You just fool them into giving up their own security.”
According to the Verizon data breach investigation report from 2016, 30 percent of phishing emails were opened. It took a recipient an average of only 40 seconds to open the email and an additional 45 seconds to also open the malicious attachment. 89 percent of all phishing emails were sent by organized crime syndicates and 9 percent by state-sponsored threat actors.
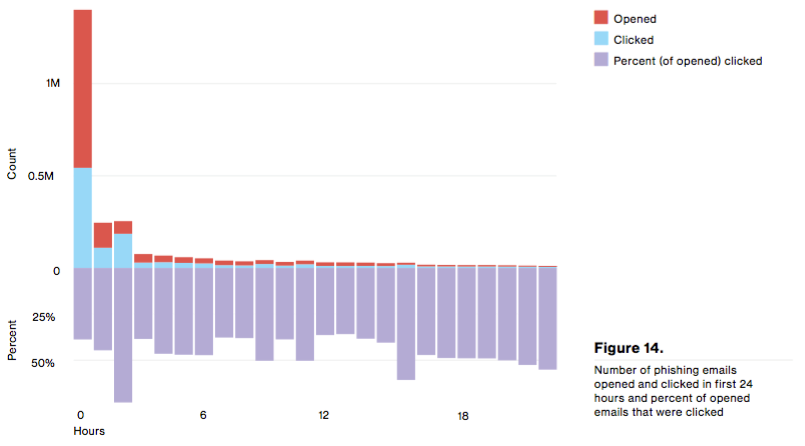
Figure 3: Verizon Data Breach Report 2016
The weakest link remains the human. But while some could argue and say the user is to blame, the reality is that many of the targeted phishing emails are so sophisticated that it is impossible for the average user to notice the difference between a malicious and a legitimate email.
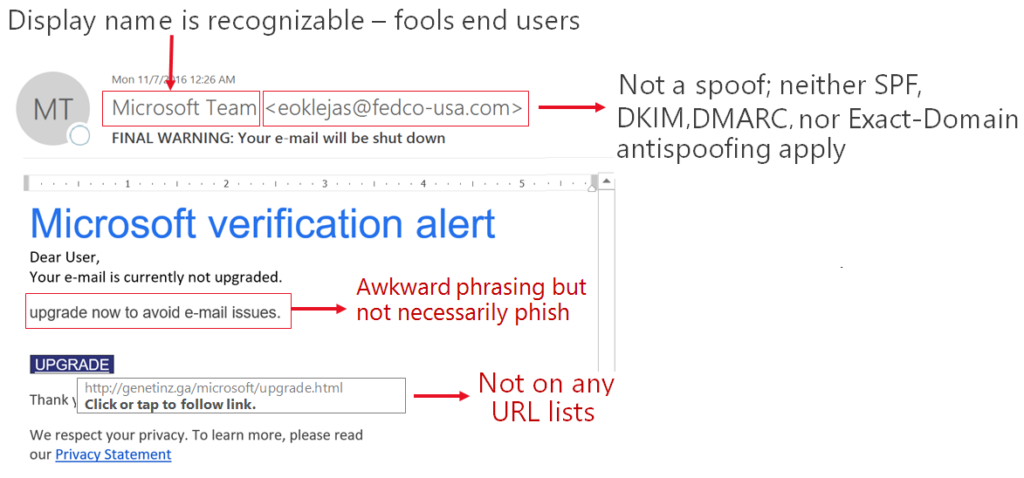
Figure 4: Example phishing emails that look legitimate at first look
Preparing a phishing email can take only a few minutes. First, the threat actors crawl social and professional networks and find as much personal information about the victim as possible. This could include organizational charts, sample corporate documents, common email headlines, pictures of the employee badge and more. There are professional tools available that pull much of this information from public or leaked databases. In fact, if needed, the threat actor can purchase the information from the dark web. For example, one million compromised email and passwords can be traded for approximately $25, bank account logins can be traded for $1 per account, and social security numbers cost approximately $3, including birth date verification. Second, the threat actor prepares an e-mail template that will look familiar to the recipient, such as for example a password reset email, and lastly, they will send it to the user.
Social engineering has become a very powerful way for many threat actors and depending on the objective of the threat actors they either leverage computer-based, mobile-based, or human-based social engineering.

Figure 5: Stages of a phishing attack
- Phase 1: Threat actor targets employee(s) via phishing campaign
- Phase 2: An employee opens the attack email which allows the threat actor access to load the malicious payload or compromise the user identity
- Phase 3: The workstation is compromised, threat actor persists malware, threat actor gathers credentials
- Phase 4: Threat actors use stolen credentials to move laterally and gain unsolicited access and compromise key infrastructure elements
- Phase 5: Threat actors exfiltrate PII and other sensitive business data
The built-in functionality of Enterprise Mobility + Security, Windows 10, Office 365, and Microsoft Azure enables organizations to disrupt these attacks. Below is a visualization allowing you to quickly understand which functionality helps in which phase:

Today, the entry level for threat actors to launch a cyber-attack is very low, therefore, it is critical that cybersecurity is a CEO matter. Organizations need to move away from “We have a firewall, anti-virus, and disk encryption technology so we are secure” mentality to a “cyber-attacks will happen, therefore we can no longer only focus on building walls but also become able to detect and responds breaches quickly” mindset. Assuming breach is key. It doesn’t matter how large or in which industry an organization is, every company has data that can be valuable for a threat actor or in some cases even a nation-state.
A consistent approach to information security is critical in today’s world. It includes having the right incident response processes in place, technologies that help protect, detect and respond cyber-attacks and lastly IT and end-user readiness.
For more information about Microsoft security products and solutions, as well as resources to help you with your security strategy, visit https://www.microsoft.com/secure.