Across Windows Defender Advanced Threat Protection (Windows Defender ATP) engineering and research teams, innovation drives our mission to protect devices in the modern workplace. Our goal is to equip security teams with the tools and insights to protect, detect, investigate, and automatically respond to attacks. We continue to be inspired by feedback from customers and partners, who share with us the day-to-day realities of security operations teams constantly keeping up with the onslaught of threats.
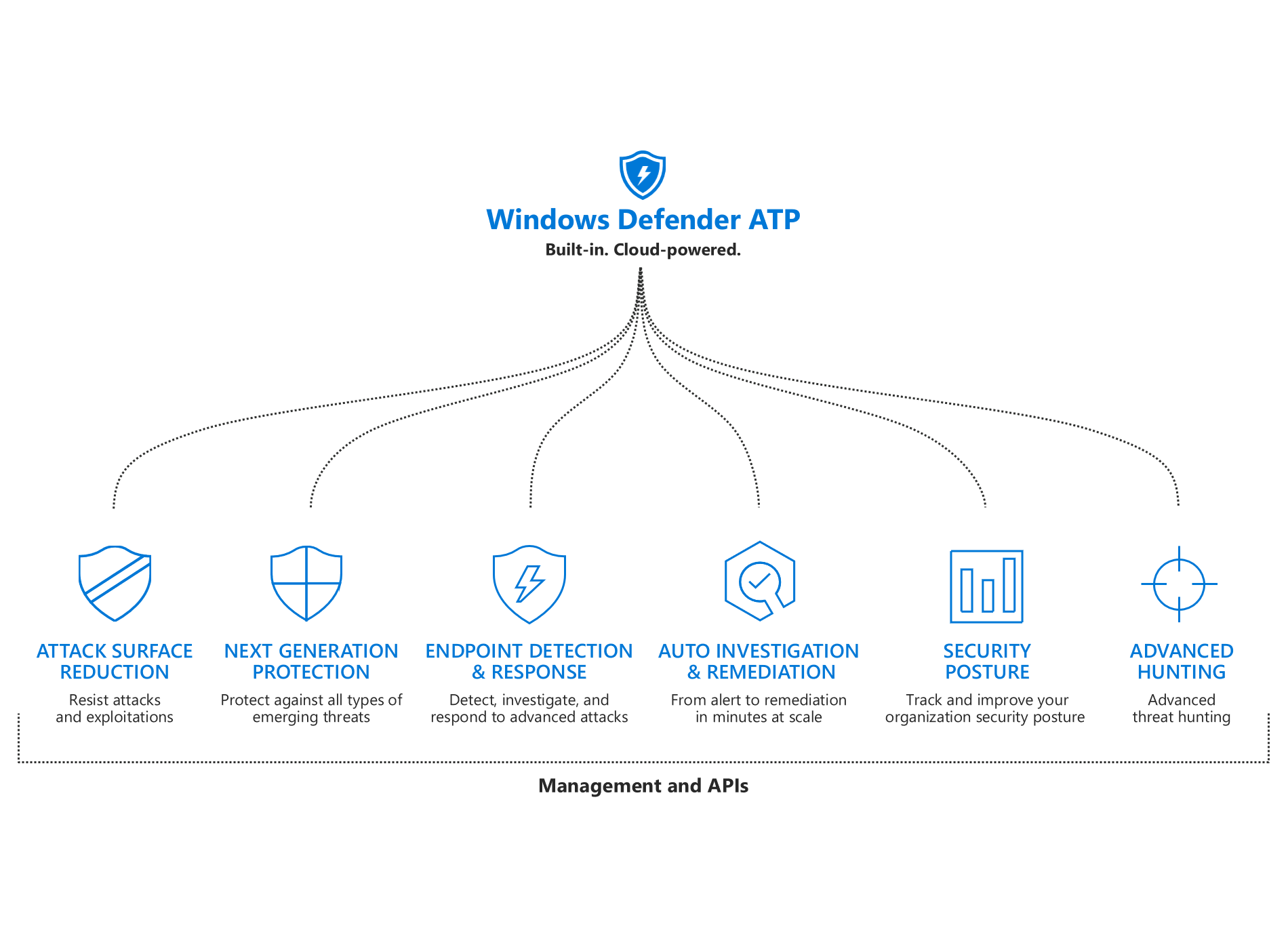
Today I’m excited to share with you some of the latest significant enhancements to Windows Defender ATP. We added new capabilities to each of the pillars of Windows Defender ATP’s unified endpoint protection platform: improved attack surface reduction, better-than-ever next-gen protection, more powerful post-breach detection and response, enhanced automation capabilities, more security insights, and expanded threat hunting. These enhancements boost Windows Defender ATP and accrue to the broader Microsoft Threat Protection, an integrated solution for securing identities, endpoints, cloud apps, and infrastructure.
Let’s look now at some of the new enhancements to Windows Defender ATP:
New attack surface reduction rules
Attack surface reduction forms the backbone of our answer to a host intrusion and prevention system (HIPS). Attack surface reduction protects devices directly, by controlling and limiting the ways in which threats can operate on a device. Today we are announcing two new rules:
- Block Office communication application from creating child processes
- Block Adobe Reader from creating child processes
These new rules allow enterprises to prevent child processes from being created from Outlook and from Adobe Reader, right at the workstation level. These help eliminate many types of attacks, especially those using macro and vulnerability exploits. We have also added improved customization for exclusions and allow lists, which can work for folders and even individual files.
Emergency security intelligence updates
Emergency security intelligence updates are new, super-fast delivery method for protection knowledge. In the event of an outbreak, Windows Defender ATP research team can now issue an emergency request to all cloud-connected enterprise devices to immediately pull dedicated intelligence updates directly from the Windows Defender ATP cloud. This reduces the need for security admins to take action or wait for internal client update infrastructure to catch up, which often takes hours or even longer, depending on configuration. There’s no special configuration for this other than ensuring cloud-delivered protection is enabled on devices.
Top scores in independent industry tests
Machine learning and artificial intelligence drive our Windows Defender ATP solution to block 5 billion threats every month and to consistently achieve top scores in independent industry tests: perfect scores in protection, usability, and performance test modules in the latest evaluation by AV-TEST; 99.8% protection rate in the latest real-world test by AV-Comparatives; and AAA accuracy rating in the latest SE Labs test.
We have added dedicated detections for cryptocurrency mining malware (coin miners) which have increasingly become a problem, even for enterprises. We have also increased our focus on detecting and disrupting tech support scams while they are happening.
Protecting our security subsystems using sandboxing
We’ve also continued to invest in hardening our platform to make it harder for malicious actors to exploit vulnerabilities and bypass the operating system’s built-in security features. We’ve done this by putting Windows Defender ATP’s antivirus in a dedicated sandbox. Sandboxing makes it significantly more difficult for an attacker to tamper with and exploit the antivirus solution as a means to compromise the device itself.
Evolving from individual alerts to Incidents
We are introducing Incidents, an aggregated view that helps security analysts to understand the bigger context of a complex security event. As attacks become more sophisticated, security analysts face the challenge of reconstructing the story of an attack. This includes identifying all related alerts and artifacts across all impacted machines and then correlating all of these across the entire timeline of an attack.
With Incidents, related alerts are grouped together, along with machines involved and the corresponding automated investigations, presenting all collected evidences and showing the end-to-end breadth and scope of an attack. By transforming the queue from hundreds of individual alerts to a more manageable number of meaningful aggregations, Incidents eliminate the need to review alerts sequentially and to manually correlated malicious events across the organization, saving up to 80% of analyst time.
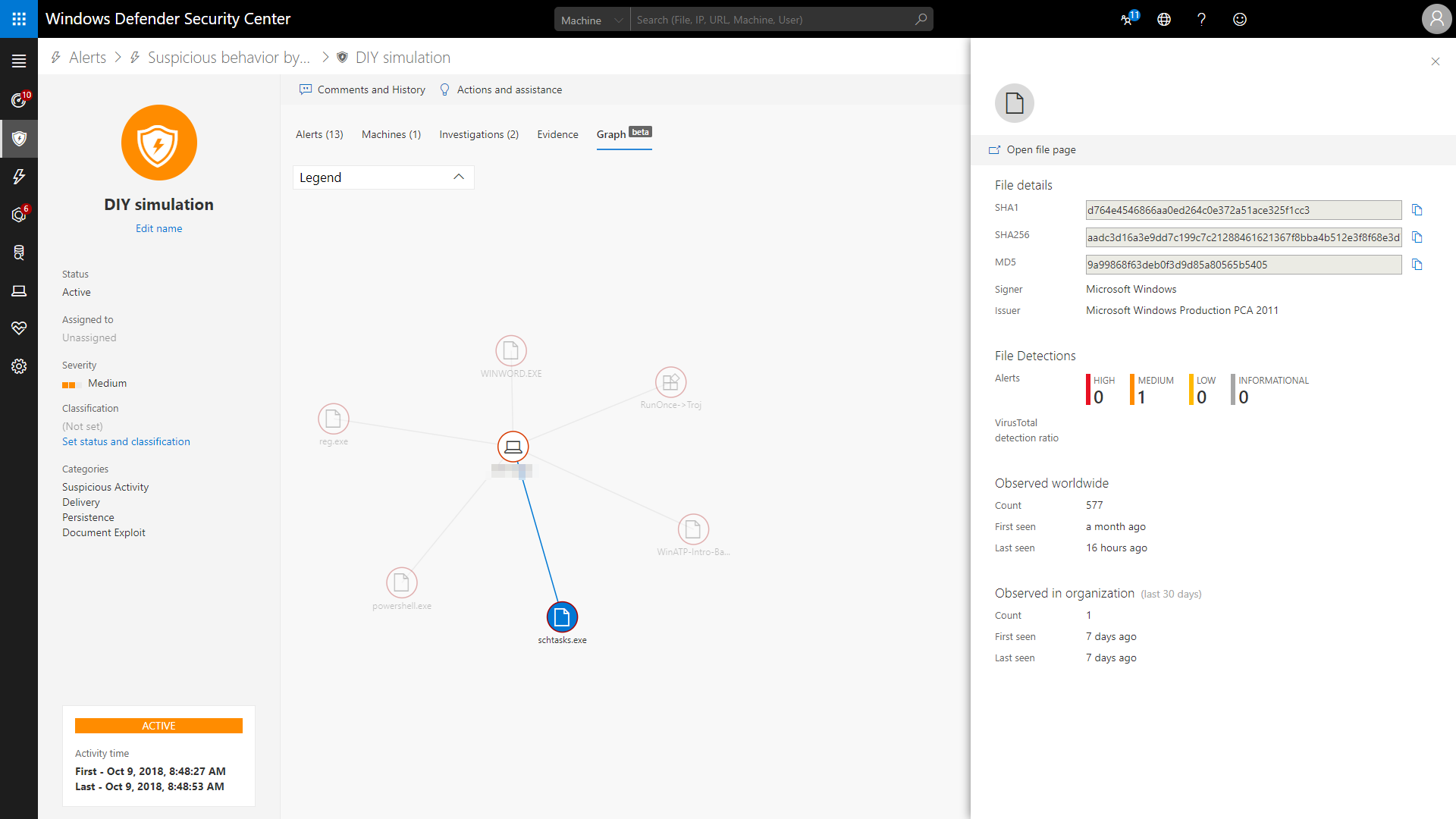
The Incident graph view shows you the relations between the entities, with additional details in the side pane when click on an item.
Automating response for fileless attacks
We expanded automation in Windows Defender ATP to automatically investigate and remediate memory-based attacks, also known as fileless threats. We see more and more of these memory-based threats, and while we’ve had the optics to detect them, security analysts needed special investigation skills to solve them. Windows Defender ATP can now leverage automated memory forensics to incriminate memory regions and perform required in-memory remediation actions.
With this new unique capability, we are shifting from simply alerting to a fully automated investigation and resolution flow for memory-based attacks. This increases the range of threats addressable by automation and further reduces the load on security teams.
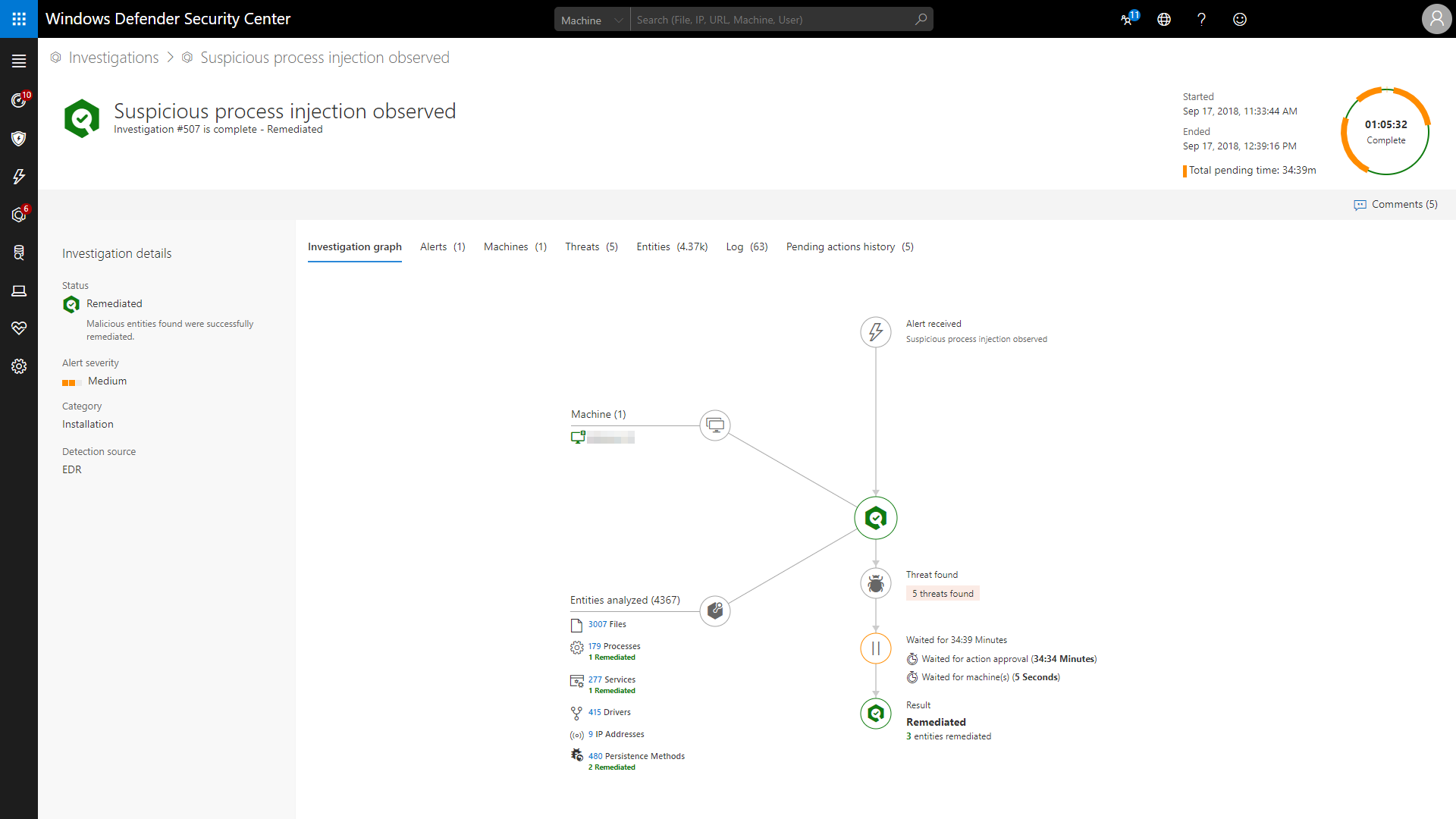
Process injection automatically investigated and remediated
Threat analytics
Threat analytics is a set of interactive threat intelligence reports published by our research team as soon as emerging threats and outbreaks are identified. The Threat analytics dashboard provides technical description and data about a threat, and answer the key question, “Does WDATP detect this threat?”. It also provides recommended actions to contain and prevent specific threats, as well as increase organizational resilience.
But we don’t stop there. We also provide an assessment of the impact of threats on your environment (“Am I hit?”), as well as show a view of how many machines were protected (“Were you able to stop this?”) and how may are exposed to the threat because they are not up-to-date or are misconfigured (“Am I exposed?”).
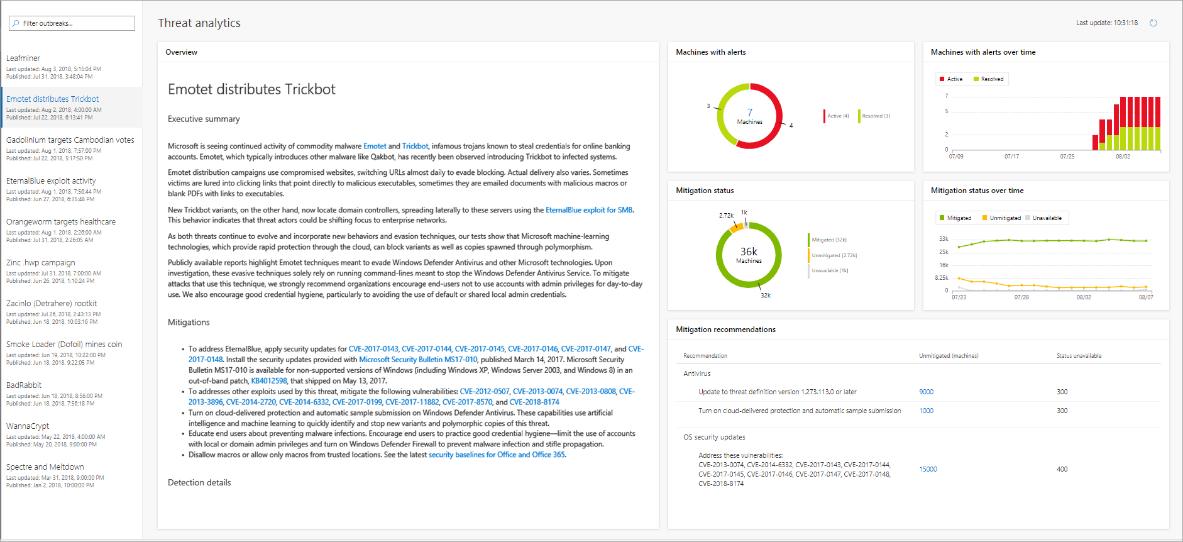
Threat analytics dashboard
Custom detection rules
With Advanced hunting, security analysts love the power they now have to hunt for possible threats across their organization using flexible queries. A growing community of security researchers share their queries with others using the GitHub community repository. These queries can now also be used as custom detection rules, which means that these queries will automatically create and raise an alert when a scheduled query returns a result.
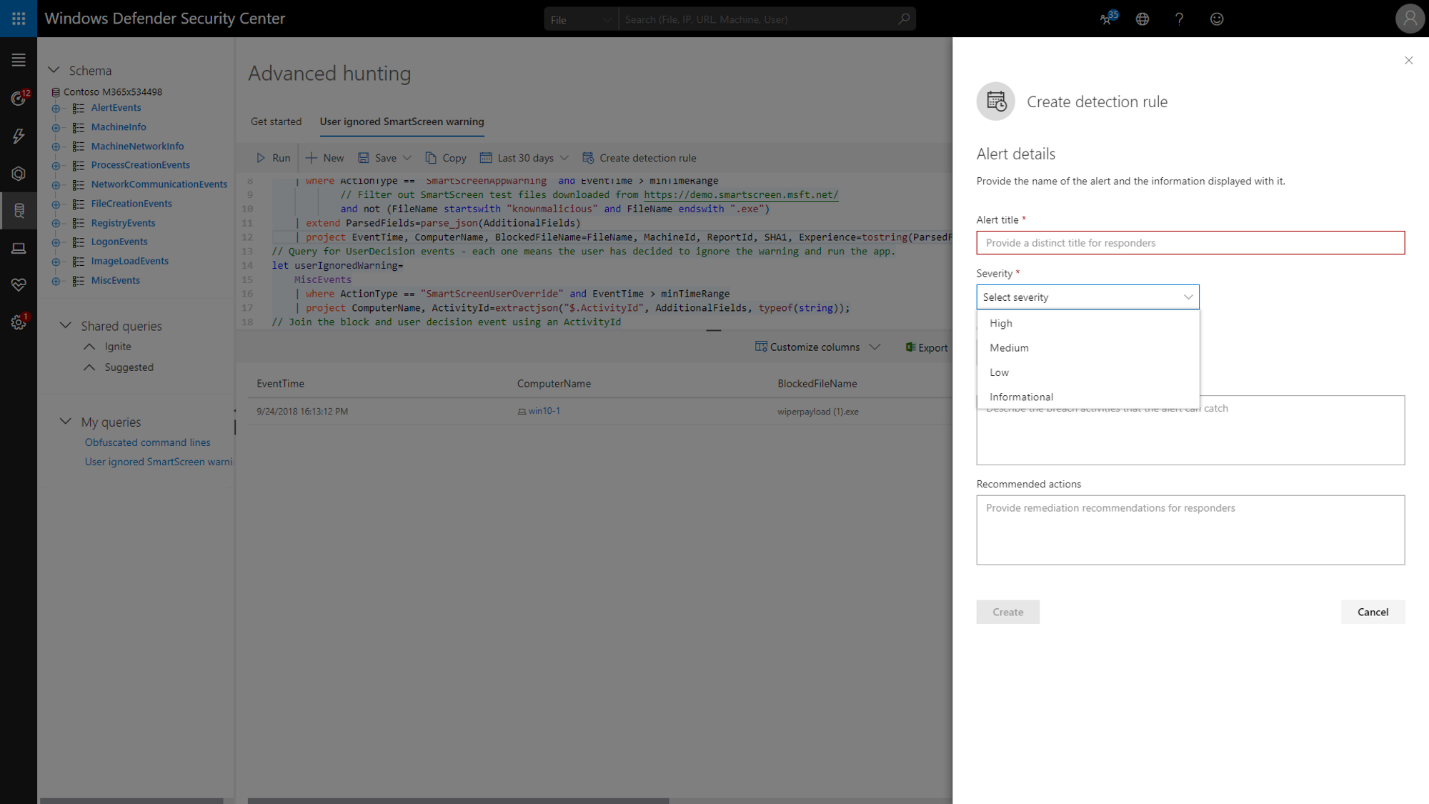
Creating custom detection rules from advance hunting queries
Integration with Microsoft Information Protection
Windows Defender ATP now provides built-in capabilities for discovery and protection of sensitive data on enterprise endpoints. We have integrated with Azure Information Protection (AIP) Data Discovery, providing visibility to labeled files stored on endpoints. AIP dashboard and log analytics will include files discovered on Windows devices alongside device risk info from Windows Defender ATP, allowing customers to discover sensitive data at risk on Windows endpoints.
Integration with Microsoft Cloud App Security
Windows Defender ATP uniquely integrates with Microsoft Cloud App Security to enhance the discovery of shadow IT in an organization as seen from enterprise endpoints. Windows Defender ATP provides a simplified rollout of Cloud App Security discovery as it feeds Cloud App Security with endpoints signals, reducing the need for collecting signals via corporate proxies and allowing seamless collection of signals even when endpoints are outside of the corporate network.
Through this integration, Microsoft Cloud App Security leverages Windows Defender ATP to collect traffic information about client-based and browser-based cloud apps and services being accessed from IT-managed Windows 10 devices. This seamless integration does not require any additional deployment and gives admins a more complete view of the usage of cloud apps and services in their organization.
Innovations that work for you today and the future
These new features in Windows Defender Advanced Threat Protection unified security platform combine the world-class expertise inside Microsoft and the insightful feedback from you, our customers, who we built these solutions for. We ask that you continue to engage and partner with us as we continue to evolve Windows Defender ATP.
You can test all new and existing features by signing up to a free 60-day fully featured Windows Defender ATP trial. You can also test drive attack surface reduction and next-gen protection capabilities using the Windows Defender demo page or run DIY simulations for features like Incidents, automated investigation and response, and others directly from the Windows Defender security center portal to see how these capabilities help your organization in real-world scenarios.
In MITRE’s evaluation of endpoint detection and response solutions, Windows Defender Advanced Threat Protection demonstrated industry-leading optics and detection capabilities. The breadth of telemetry, the strength of threat intelligence, and the advanced, automatic detection through machine learning, heuristics, and behavior monitoring delivered comprehensive coverage of attacker techniques across the entire attack chain. Read the blog: Insights from the MITRE ATT&CK-based evaluation of Windows Defender ATP.
Meanwhile, the work to stay ahead of threats doesn’t stop. You can count on the Windows Defender ATP team to continue innovating, learning from our own experiences, and partnering with you to empower you to confidently protect, detect, and respond to advanced attacks.
Moti Gindi
General Manager, Windows Cyber Defense
Talk to us
Questions, concerns, or insights on this story? Join discussions at the Microsoft community and Windows Defender Security Intelligence.
Follow us on Twitter @WDSecurity and Facebook Windows Defender Security Intelligence.