Microsoft Threat Protection continues to energize the threat protection market with our most recent announcements. Customers are excited about the launch of Microsoft Defender Advanced Threat Protection (ATP), which extends Microsoft’s best in class endpoint security to Mac and adds powerful new capabilities of Threat and Vulnerability Management.
These new features provide significant value to security administrators and operations teams with:
- Real-time endpoint protection, plus detection and response (EDR) insights across Windows and Mac, correlated with endpoint vulnerabilities.
- Invaluable vulnerability and misconfiguration context during incident investigations on machine or organization level.
- Built-in remediation processes through a tight integration with Microsoft Intune and Microsoft System Center Configuration Manager.
We’re committed to maintaining this pace of innovation as we continue our journey towards our ideal vision of Microsoft Threat Protection.
Watch Rob Lefferts deliver an update on the latest enhancements:
This strong vision can only be built on a solid foundation. We want to share the details of this foundation, which enables Microsoft Threat Protection to deliver a powerful, effective, and unique threat protection solution to customers.
The foundation of our vision begins with a Zero Trust approach
Microsoft Threat Protection is built to support a Zero Trust security strategy because we believe the fundamental goal for any threat protection solution is to ensure bad actors don’t gain access to your corporate assets. Traditional threat protection relied primarily on firewalls securing on-premises assets in a defined corporate perimeter.
Today, most organizations are migrating to the cloud and have hybrid environments. Data is spread across multiple applications, on-premises and in the cloud, and is accessed by multiple devices (often personal devices) and users. Most organizations no longer have a defined network perimeter making traditional security tools obsolete. For today’s world, Microsoft recommends organizations adopt a Zero Trust model where it’s assumed that everything is on the open internet and no resources are “safe.”
Zero Trust eliminates the concept of users, endpoints, or apps being trusted sources simply because they are located within the corporate network perimeter. Identity becomes the essential element connecting organizations in a Zero Trust world. Threat actors realize this and direct many campaigns at user identities, leading to 81 percent of breaches occurring through identity theft or compromise.
With this growing trend of cyberattacks targeting identities, coupled with identity being the control plane connecting a user to all aspects of the organization (Figure 1), securing the user identity has become fundamental to business success. Because identity security is so critical, Microsoft Threat Protection is rooted to Azure Active Directory (Azure AD), the most sophisticated, comprehensive, and secure identity service on the market.
With the specific features offered as part of Azure AD Identity Protection, organizations can enhance identity security with:
- Monitoring every sign-in to determine sign-in risk and user risk, and assess identity compromise.
- Detection of potential threats affecting your organization’s cloud and on-premises identities.
- Configurations for automated protection and remediation against malicious authentications and compromised credentials.
- Investigation of suspicious incidents and appropriate actions to resolve them.
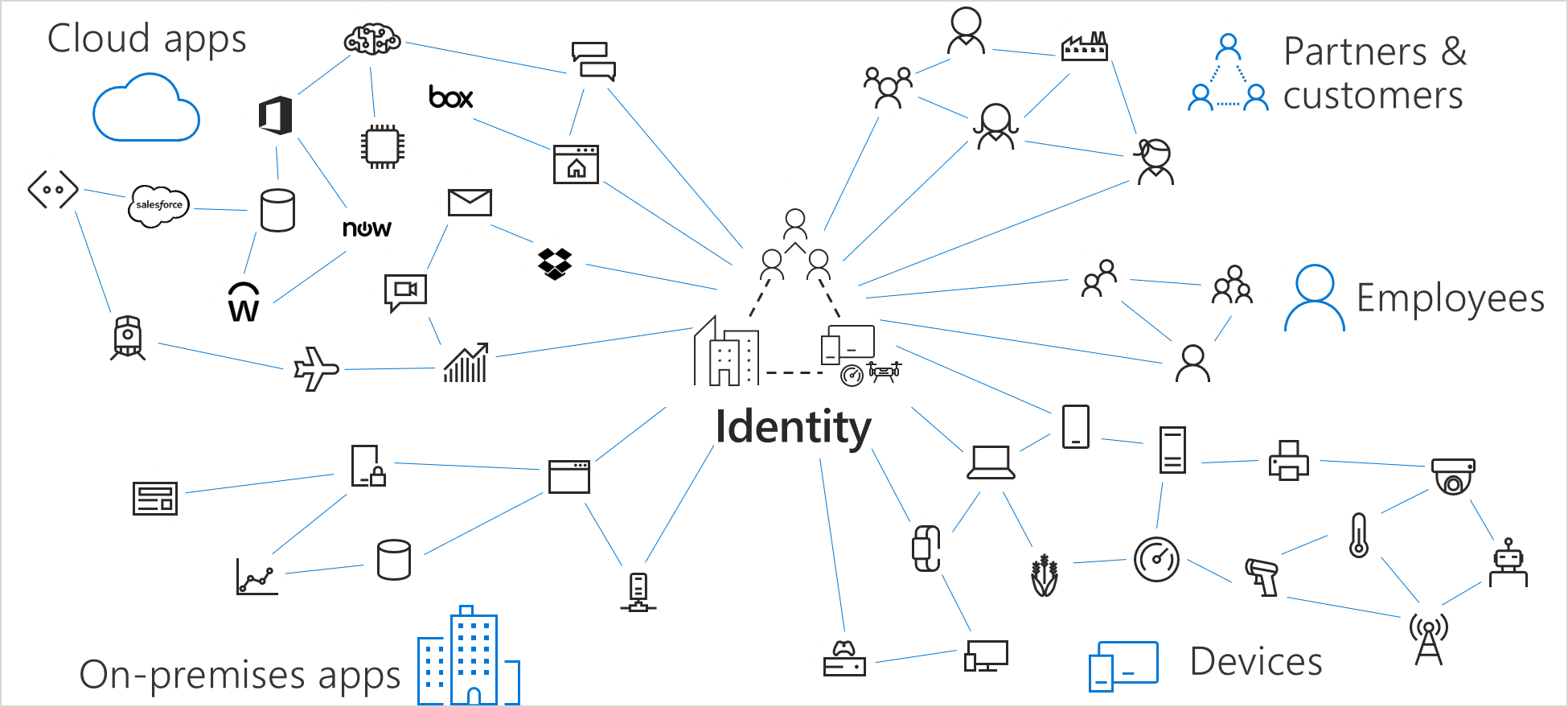
Figure 1. Identity is the control plane that connects all the elements of an organization in the new world of no perimeters.
Azure AD allows admins to create a single identity for each user from which to manage access to corporate data and apps, whether on-premises or in the cloud. Additionally, Azure AD protects internal and external users while optimizing for user productivity.
With Azure AD as its foundation, Microsoft Threat Protection further supports a Zero Trust strategy with native integrations between Azure AD and:
- Cloud App Security Broker (CASB) and Microsoft Cloud App Security, which secure cloud apps and services.
- Azure ATP, which helps detect and investigate advanced attacks on-premises and in the cloud.
- Microsoft Intune (which further integrates with Microsoft Defender ATP).
The signal shared between Azure AD and these services stitches security across the entire estate, empowering organizations using Microsoft Threat Protection to adopt a best in class Zero Trust strategy while benefitting from a seamless, fully integrated threat protection solution.
Executing a Zero Trust strategy with the industry’s most powerful conditional access policies
The first layer of a powerful threat protection solution begins with securing access to organizational assets. It is imperative to ensure only the right users have access to your critical corporate assets. This task is more difficult today as more organizations adhere to a mobile-first, cloud-first strategy, allowing users to access corporate resources using myriad devices and apps from anywhere. Admins must always balance user productivity with securing corporate assets. This requires not only controlling who can access a resource, but also under what conditions a resource is accessed when making an access control decision. Azure AD conditional access enables admins to make this critical determination with conditional access policies (Figure 2).
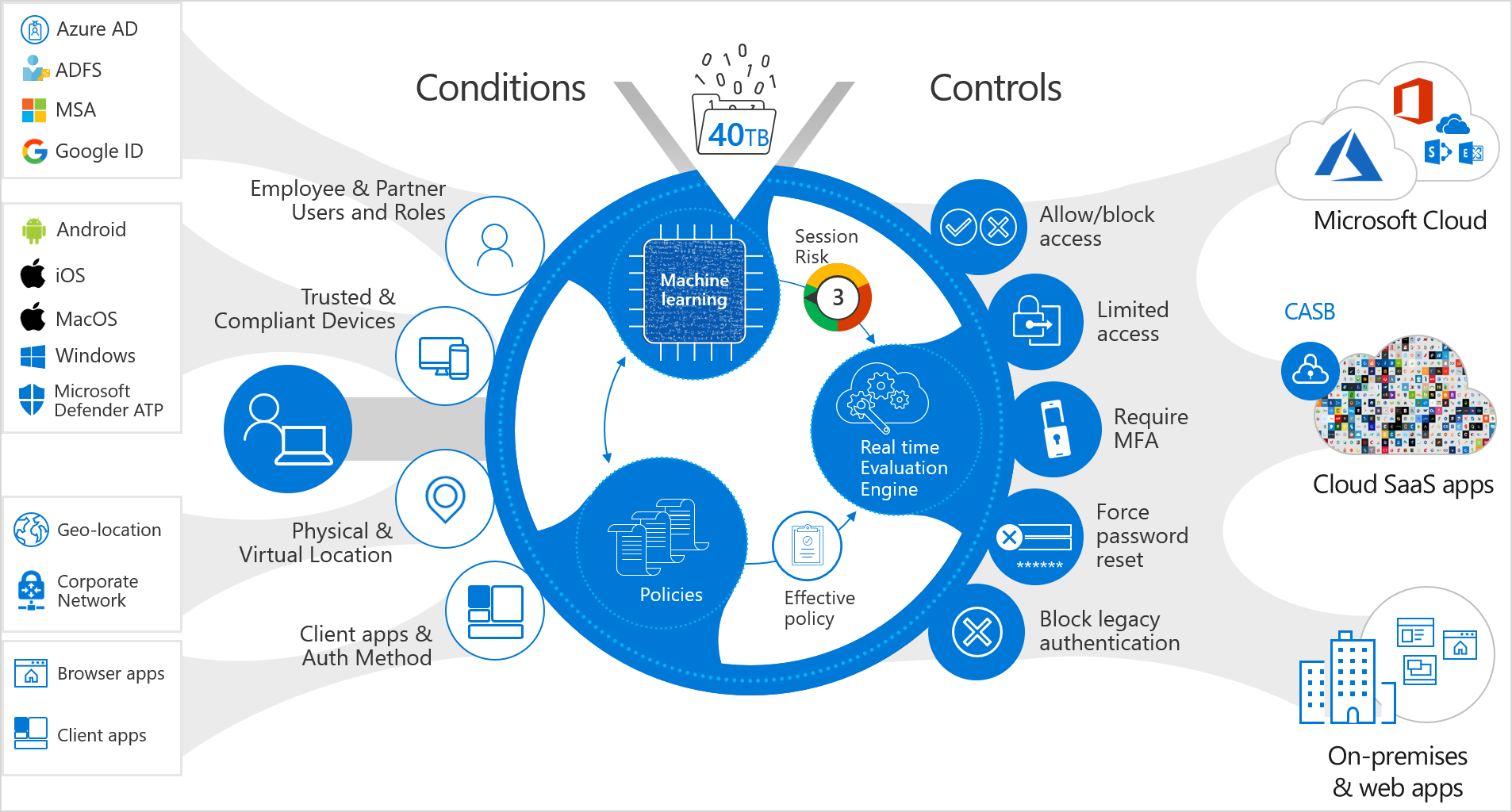
Figure 2. Conditional access policy showing the possible conditions (which user, on what device, from where, which app), the 40 TB of real-time data assessment, and the controls applied to the access request based on conditions.
Conditional access supports various conditions. Azure AD’s advanced machine learning models assess each authentication coming into the service to determine the risk level. This risk evaluation feeds into conditional access policies to determine if the policy’s conditions are met. Risk can be attributed to a sign-in (sign-in risk) or a user (user risk). Sign-in risk represents the probability of the identity owner authorizing the sign-in, while user risk represents the probability the user is compromised. Admins can set up automated policies (conditional access policies or Azure AD risk policies) to:
- Remediate risky sign-ins by blocking or challenging them (sign-in risk policy).
- Remediate risky users by blocking or forcing them to securely reset their credentials during the next sign-in (user risk policy).
When a user attempts to access any corporate asset, 40TB of data—which includes detections for users with leaked credentials, sign-ins from anonymous IP addresses, impossible travel to atypical locations, sign-ins from unfamiliar locations, and sign-ins from infected devices—is assessed to determine the real-time risk level. Based on the risk level, access is granted or blocked, helping ensure an organization’s most important and critical assets are only accessed by users who meet the conditional access policy criteria.
As shown in Figure 3, blocked access is considered a new risk event, raising the user risk level. For any subsequent access request, the user must meet criteria for a stricter conditional access policy to gain access. All the other services in Microsoft Threat Protection build from this dynamic and powerful layer of security. This secure foundation ensures only the least risky users have access to critical corporate assets. Conditional access is extremely powerful because when only the least risky users are granted access, the overall risk to the organization is significantly reduced.
Figure 3. Azure AD conditional access assigns a risk score to an access request and updates the risk score based on any new detections.
Risk-based in-session controls
Microsoft Threat Protection’s identity security also offers continuous monitoring and control of user activities in real-time. This critical capability enables organizations to decide on the actions users can carry out across cloud apps, based on the user risk determined at time of sign-in. Continuous monitoring of in-session user behavior and dynamic, real-time evaluation of risk levels helps to ensure the user is not a potential threat actor using a compromised identity. The integration between Azure AD conditional access and Microsoft Cloud App Security unlocks the ability to monitor user behavior and control activities in real-time, after they gain access to a cloud application, and will therefore also protect organizational resources in the event an account is compromised.
The example in Figure 4 demonstrates a scenario where an external user, on an unmanaged device, attempts to access a file in Box. The sign-in is authenticated by Azure AD, which calculates both sign-in and user risk. Azure AD defines the user risk level based on factors such as device compliance and location to determine whether Microsoft Cloud App Security will limit any in-session user activities or provide full access to cloud apps. As a result of the session level risk, the user session is routed via Microsoft Cloud App Security where potentially risky user actions such a downloading sensitive information or uploading files are blocked, preventing data exfiltration or infiltration. In the case shown below, the policy allows the user to view the file, but does not allow for file download due to the higher risk of an external user on an unmanaged device.
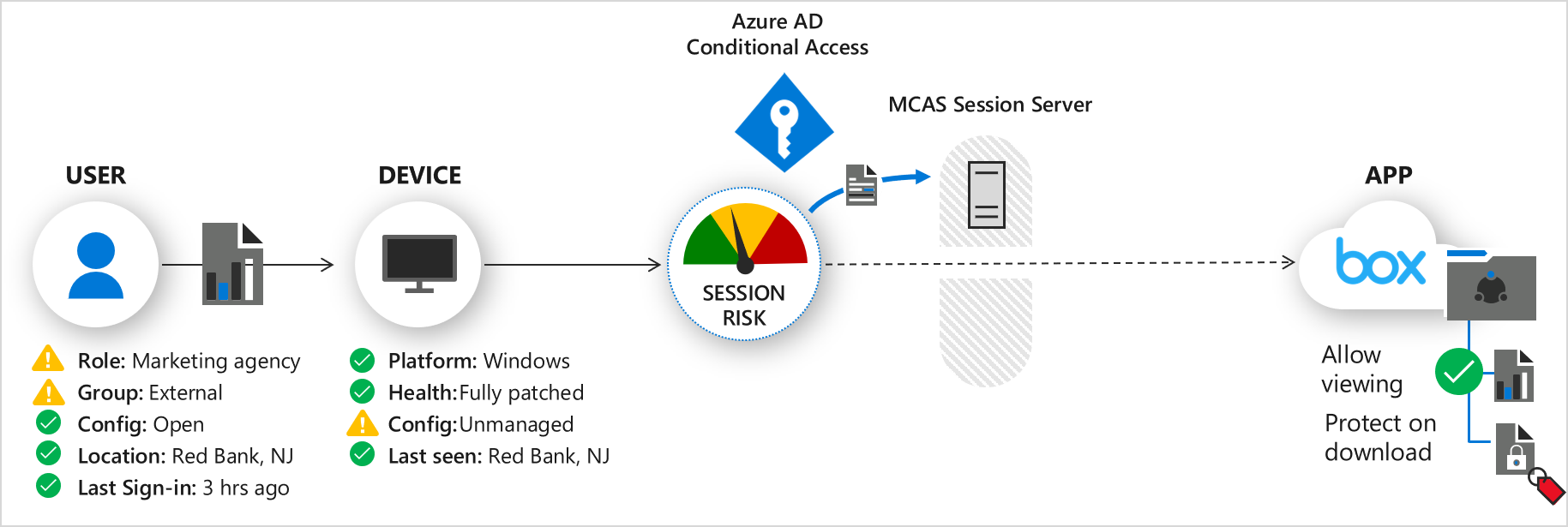
Figure 4. Blocking an external user from downloading a file with an unmanaged device.
Powerful threat investigation and response capabilities for potentially compromised identities
Threat protection is only complete with effective response for the inevitable threats which penetrate your environment. Azure AD’s new integration with Azure ATP offers a powerful SecOps capability for threat response (in preview). As noted, integration between Azure AD and Microsoft Cloud App Security enables continuous monitoring of user behavior from sign-in through the entire session. Microsoft Threat Protection’s identity services leverage user behavior analytics to create a dynamic investigation priority score based off signal from Azure AD, Microsoft Cloud App Security, and Azure ATP. The investigation priority is calculated from assessing security alerts, abnormal activities, and potential business and asset impact related to each user.
This score can help SecOps teams focus and respond to the top user threats in the organization. Azure ATP also provides recommendations on what actions to take to effectively remediate the threat. This new investigation and response capability, plus the protection and detection capabilities we described earlier, together offer customers truly comprehensive identity security with Microsoft Threat Protection.
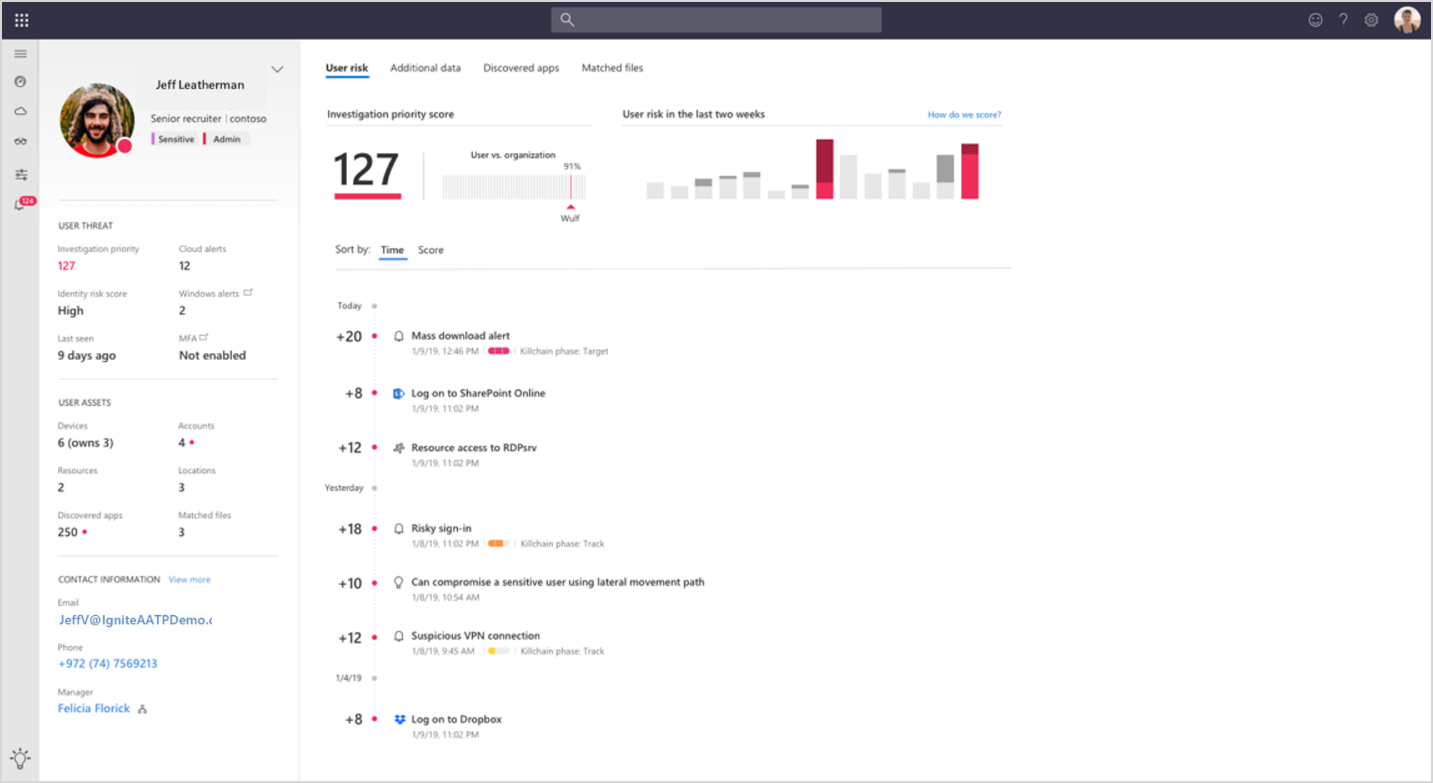
Figure 5. Investigation priority score of a user with a summary of the user alerts.
Experience the evolution of Microsoft Threat Protection
Take a moment to learn more about Microsoft Threat Protection, read our previous monthly updates, and visit our website.
Organizations have already transitioned to Microsoft Threat Protection and partners are leveraging its powerful capabilities. Begin a trial of Microsoft Threat Protection services today to experience the benefits of the most comprehensive, integrated, and secure threat protection solution for the modern workplace.
- Microsoft Threat Protection trial
- Microsoft Threat Protection’s new SIEM, Microsoft Azure Sentinel








