One of the things we spend a great deal of time thinking about here at Microsoft is how attackers will attempt to persist and evade detection once they’ve successfully compromised a device. With Windows 10 we’ve made it more difficult to find ways to exploit potential entry points, and it’s clear that its harder than it’s ever been before.
The ability for an attacker to persist and evade detection is a critical part of the trade craft; compromising the integrity of the platform and defenses is the best way to get there. With Windows 7 we included a number of perimeter defenses that could be augmented with third-party solutions, but the reality is that all of those defenses could be rendered ineffective if the integrity of the platform itself is compromised. For this reason, creating the condition where the platform’s integrity can be maintained and monitored is mission-critical.
Just a few weeks ago at Ignite we announced Windows Defender System Guard, which ships in Windows 10, version 1709, also known as the Fall Creators Update. It reorganizes the existing Windows 10 system integrity features under one roof and sets us up for the next set of investments that we will make in the future. With it we hope to create the condition that the integrity of the system can’t be compromised, and if it is, you will know about it.
So, what security guarantees is Windows Defender System Guard designed to make? They include the ability to:
- Protect and maintain the integrity of the system as it starts up
- Protect and maintain the integrity of the system after it’s running
- Validate that system integrity has truly been maintained through local and remote attestation
Maintaining the integrity of the system as it starts up
With Windows 7, one of the means attackers would use to persist and evade detection was to install what is often referred to as a bootkit or rootkit on the system. This malicious software would start before Windows started, or during the boot process itself, enabling it to start with the highest level of privilege.
With Windows 10 running on modern hardware (i.e., Windows 8-certified or greater) we have a hardware-based root of trust that helps us ensure that no unauthorized firmware or software (e.g., bootkit) can start before the Windows bootloader. This hardware-based root of trust comes from the device’s Secure Boot feature, which is part of the Unified Extensible Firmware Interface (UEFI). After successful verification and startup of the device’s firmware and Windows bootloader, the next opportunity for attackers to tamper with the system’s integrity is while the rest of the Windows operating system and defenses are starting. As an attacker, embedding your malicious code using a rootkit within the boot process enables you to gain the maximum level of privilege and gives you the ability to more easily persist and evade detection. This is where Windows Defender System Guard protection begins with its ability to ensure that only properly signed and secure Windows files and drivers, including third party, can start on the device. At the end of the Windows boot process, System Guard will start the system’s antimalware solution which scans all third party drivers, at which point the system boot process is completed. In the end, Windows Defender System Guard helps ensure that the system securely boots with integrity and that it hasn’t been compromised before the remainder of your system defenses start.
Maintaining integrity of the system after it’s running (run time)
Prior to Windows 10, if an attacker exploited the system and gained SYSTEM level privilege or they compromised the kernel itself, it was game over. The level of control that an attacker would acquire in this condition would enable them to tamper with and bypass many, if not all, of your system defenses. While we have number of development practices and technologies (e.g., Windows Defender Exploit Guard) that have made it difficult to gain this level of privilege in Windows 10, the reality is that we needed a way to maintain the integrity of the most sensitive Windows services and data, even when the highest level of privilege has been secured by an adversary.
With Windows 10 we introduced the concept of virtualization-based security (VBS), which enables us to hardware isolate the most sensitive Windows services and data; starting with the Fall Creators Update have named this environment the Windows Defender System Guard container. This secure environment provides us with the hardware-based security boundary we need to be able to secure and maintain the integrity of critical system services at run time like Credential Guard, Device Guard, Virtual TPM and parts of Windows Defender Exploit Guard, just to name a few.
Validating platform integrity after Windows running (run time)
While Windows Defender System Guard provides advanced protection that will help protect and maintain the integrity of the platform during boot and at run time, the reality is that we must apply an assume breach mentality to even our most sophisticated security technologies. We should be able to trust that the technologies are successfully doing their jobs, but we also need the ability to verify that they were successful in achieving their goals. When it comes to platform integrity, we can’t just trust the platform, which potentially could be compromised, to self-attest to its security state, and so Windows Defender System Guard includes a series of technologies that enable remote analysis of the device’s integrity.
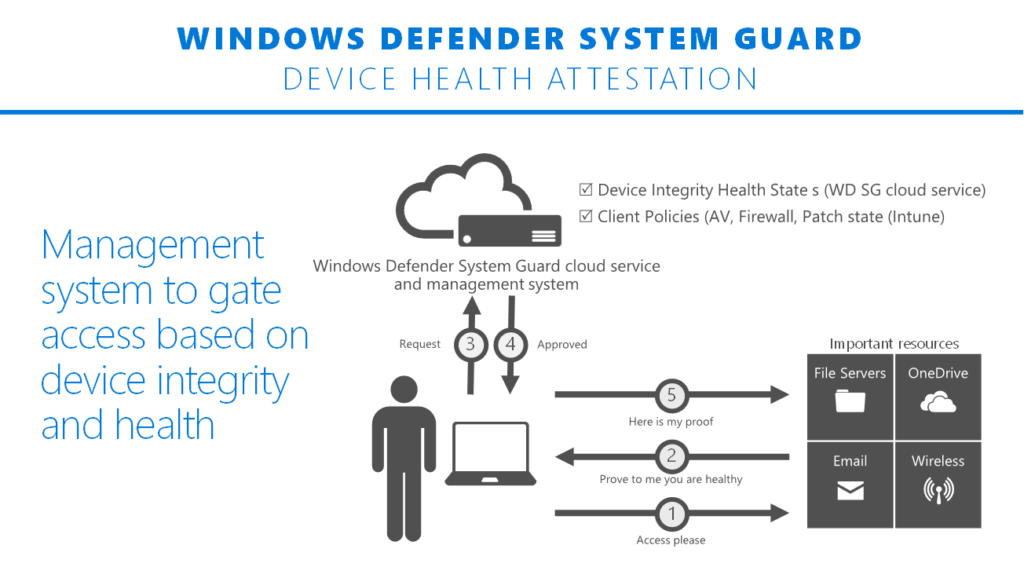
As Windows 10 boots, a series of integrity measurements are taken by Windows Defender System Guard using the device’s Trusted Platform Module 2.0 (TPM). This process and data are hardware isolated away from Windows to help ensure that the measurement data is not subject to the type of tampering that could happen if the platform was compromised. From here, the measurements can be used to determine the integrity of the device’s firmware, hardware configuration state, and Windows boot-related components, just to name a few. After the system boots, Windows Defender System Guard signs and seals these measurements using the TPM, and, upon request a management system, like Intune or System Center Configuration Manager, can acquire them for remote analysis. From here the management system can take a series of actions, such as denying the device access to resources, if Windows Defender System Guard indicates that the device lacks integrity.
With the Fall Creators Update, Windows Defender System Guard is, for the most part, a new way of talking about a number of existing Windows 10 technologies, but it was designed to be much more than that. With the Fall Creators Update, Windows Defender System Guard enabled us to simplify both the Windows design itself and our message on how we maintain and validate platform integrity. More importantly, it helped us lay the groundwork for adding new platform integrity innovations in the future. We look forward to sharing more about the roadmap for Windows Defnder System Guard in the months to come.
Chris Hallum
Senior Product Manager, Windows & Devices Group, Security & Enterprise
Learn more about Windows 10 Fall Creators Update
Windows Defender Exploit Guard: Reduce the attack surface against next-generation malware
Stopping ransomware where it counts: Protecting your data with Controlled folder access
Making Microsoft Edge the most secure browser with Windows Defender Application Guard
Introducing Windows Defender Application Control
Hardening the system and maintaining integrity with Windows Defender System Guard
Move away from passwords, deploy Windows Hello. Today!
What’s new in Windows Defender ATP Fall Creators Update
Antivirus evolved
Talk to us
Questions, concerns, or insights on this story? Join discussions at the Microsoft community and Windows Defender Security Intelligence.
Follow us on Twitter @WDSecurity.