Application control is a crucial line of defense for protecting enterprises given today’s threat landscape, and it has an inherent advantage over traditional antivirus solutions. Specifically, application control flips the model from one where all applications are assumed trustworthy by default to one where applications must earn trust in order to run. Many organizations, like the Australian Signals Directorate, understand this and frequently cite application control as one of the most effective means for addressing the threat of executable file-based malware (.exe, .dll, etc.).
While most customers inherently understand the value of application control, the reality is that few customers have been able to employ application control solutions in a manageable way. Consequently, adoption of application control solutions is low. In fact, we estimate that only about 20% of our customers are using any type of application control technology; in many cases these customers use it only on a subset of devices because of the difficulty of creating and maintaining a comprehensive Allow/Deny list. With Windows 10, version 1709, also known as the Fall Creators Update we think we have changed that, and now have a solution that is a viable option for most of our customers to adopt and deploy across nearly all of their devices.
Application Control in Windows 10
With Windows 10 we introduced Windows Defender Device Guard, a set of hardware and OS technologies that, when configured together, allow enterprises to lock down Windows systems so they operate with many of the properties of mobile devices. Device Guard would restrict devices to only run authorized apps using a feature called configurable code integrity (CI), while simultaneously hardening the OS against kernel memory attacks through the use of virtualization-based protection of code integrity (HVCI). With Device Guard’s configurable CI, specifically, customers gained access to a highly differentiated application control solution that provided several unique advantages not found in most other solutions.
First, configurable CI policy is enforced by the Windows kernel itself. As such, the policy takes effect early in the boot sequence before nearly all other OS code and before traditional antivirus solutions run. Second, configurable CI allows customers to set application control policy not only over code running in user mode, but also kernel mode hardware and software drivers and even code that runs as part of Windows. Third, customers could protect the configurable CI policy even from local administrator tampering by digitally signing the policy. This meant that changing the policy required not just administrative privilege, but also access to the organization’s digital signing process. This made it extremely difficult for an attacker or malware that managed to gain administrative privilege to alter the application control policy. And finally, the entire configurable CI enforcement mechanism could be protected by HVCI, which creates the condition where even if a vulnerability exists in kernel mode code, the likelihood that an attacker could successfully exploit it is significantly diminished. Why is this relevant? That’s because an attacker that compromises the kernel would otherwise have enough privilege to disable most system defenses and override the application control policies enforced by configurable CI or any other application control solution.
(Re-)Introducing Windows Defender Application Control
When we originally designed Device Guard it was built with a specific security promise in mind. Although there were no direct dependencies between its two main OS features, configurable CI and HVCI, we intentionally focused our marketing story around the Device Guard lockdown state you achieve when deploying them together. However, this unintentionally left an impression for many customers that the two features were inexorably linked and could not be deployed separately. And given that HVCI relies on the Windows virtualization-based security, it comes with additional hardware, firmware, and kernel driver compatibility requirements that some older systems can’t meet. As a result, many customers assumed that they couldn’t use configurable CI either. But configurable CI carries no specific hardware or software requirements other than running Windows 10, which means many customers were wrongly denied the benefits of this powerful application control capability.
Since the initial release of Windows 10, the world has witnessed numerous hacking and malware attacks where application control alone could have prevented the attack altogether. And so, with the Fall Creators Update we are promoting configurable CI within our security stack and giving it a name of its own: Windows Defender Application Control. We hope this branding change will help us communicate with customers about their options for application control in Windows and, in so doing, allow more of our customers to begin to approach application control within their organizations.
Does this mean Windows Defender Device Guard is going away? Not at all. Device Guard will continue to exist as a way to describe the fully locked down state achieved through the use of Windows Defender Application Control (WDAC), HVCI, and hardware and firmware security features. It also allows us to work with our OEM partners to identify specifications for devices that are “Device Guard capable” so that our joint customers can easily purchase devices that meet all of the hardware and firmware requirements of the original Device Guard scenario.
Making Application Control easier with managed installer
In the Windows 10 Creators Update (1703) released last spring we introduced an option to WDAC called managed installer to simplify the management of WDAC for organizations with centrally managed software libraries through solutions like System Center Configuration Manager. With the managed installer option, enterprises can declare trusted software distribution authorities so that any applications deployed by them are automatically authorized by the WDAC application control policy without the need to define explicit allow rules. System Center Configuration Manager 1706 added native support for WDAC and managed installer, making deployment of WDAC a two- to three-click action.
Application Control for allow list management made easy
Repositioning Windows Defender Application Control within our security stack eliminates the requirements confusion of Device Guard, and managed installer drastically simplifies options for organizations with well-managed software libraries. Yet many customers struggle to introduce application control due to business necessity or organizational resistance to central control. With these customers in mind, we are excited to introduce a new option for Windows Defender Application Control in the Fall Creators Update that will allow enterprises to leverage Microsoft’s cloud-powered Intelligent Security Graph (ISG) to automatically authorize well-known and reputable apps built from a catalog of billions of apps and binaries that run on Windows. When the ISG option is enabled, software that Microsoft’s ISG determines as being well-known and reputable will be automatically authorized without the need for specific, manually authored rules for each application or binary. This allows IT administrators to easily allow commonly used and prevalent software like Microsoft Office and Adobe Reader, while preventing unknown and known-bad software from running. This kind of cloud-driven application control will help customers protect their environments from attacks like WannaCry that run uncommon scripts or binaries, while still empowering their end users or business groups to manage their individual application needs.
Application Control for more tightly managed or centralized environments
All of the new policy options introduced in the Creators Update and the Fall Creators Update are meant to complement the WDAC policies from earlier Windows 10 releases. Code signing provides the most robust way to identify and authorize applications, and when used with explicit allow and deny rules code-signing provides enterprises the means to express the most secure application control policies. Newer controls like managed installer and ISG-driven application control give enterprises the flexibility they need to balance manageability and security demands. When these options are used with existing tools like signtool, Package Inspector and the Microsoft Store for Business’ Device Guard Signing Service, enterprises have everything they need to start the journey to more secure Windows 10 systems through application control. For apps that are in active development, Windows SDK tools like signtool are available to incorporate code signing into the build process of an application. For applications that are not in active development or acquired from third parties, Package Inspector provides a way to generate a catalog file by monitoring an application’s installation process. Once created, the catalog file can be signed using the organization’s own signature, thus allowing the organization to authorize existing applications without needing to rebuild or repackage them. Catalog signing can be done with certificates issued by the organization’s own internal PKI or by using the Device Guard Signing Service to manage code signing keys and sign catalog files. The Device Guard Signing Service automatically generates and secures organization-specific code signing keys and provides a convenient interface for uploading and signing application catalog files.
Windows Defender Application Control in Windows Defender ATP
With the Fall Creators update, Windows Defender Advanced Threat Protection (Windows Defender ATP) is getting a significant update, one of which is related to integrated management of the Windows preventive protection stack, meaning features like Windows Defender Application Control, Antivirus, Firewall, and others will all provide full optics into the malware and other types of attacks that have been encountered but successfully blocked by the Windows preventive protection stack. All of this information will be surfaced in Windows Defender ATP’s Security Center Console, which acts as a single pane of glass for the security operations team.
To test how Windows Defender ATP can help your organization detect, investigate, and respond to advanced attacks, sign up for a free trial.
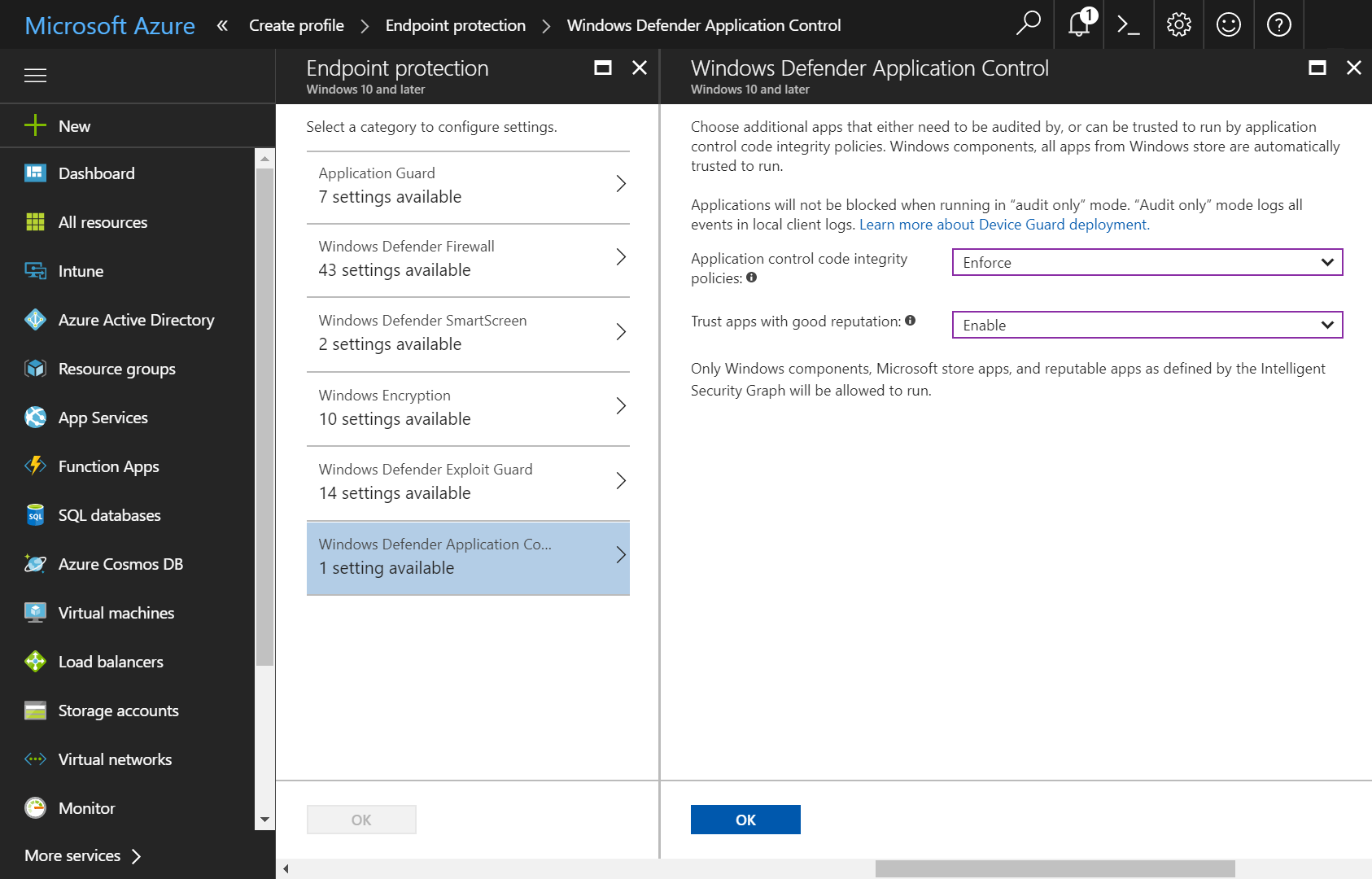
In addition, these same preventive protection features can also be centrally enabled and configured in either System Center Configuration Manager or in Intune, as shown in the image below.
With the Fall Creators Update we believe that we have democratized application control by being one of the first solutions in the market that makes it easy to manage and enables it to work on any device running the Enterprise edition of Windows 10. Please download the Fall Creators update and begin proof of concept testing to see if Windows Defender Application Control is a good fit for your organization. We look forward to hearing your feedback so we can continue to make it a better solution for your organization and users.
Nazmus Sakib
Program Manager, Windows & Devices Group, Security & Enterprise
Talk to us
Questions, concerns, or insights on this story? Join discussions at the Microsoft community and Windows Defender Security Intelligence.
Follow us on Twitter @WDSecurity.







