Patch me if you can: Cyberattack Series
The Microsoft Incident Response team takes swift action to help contain a ransomware attack and regain positive administrative control of the customer environment.

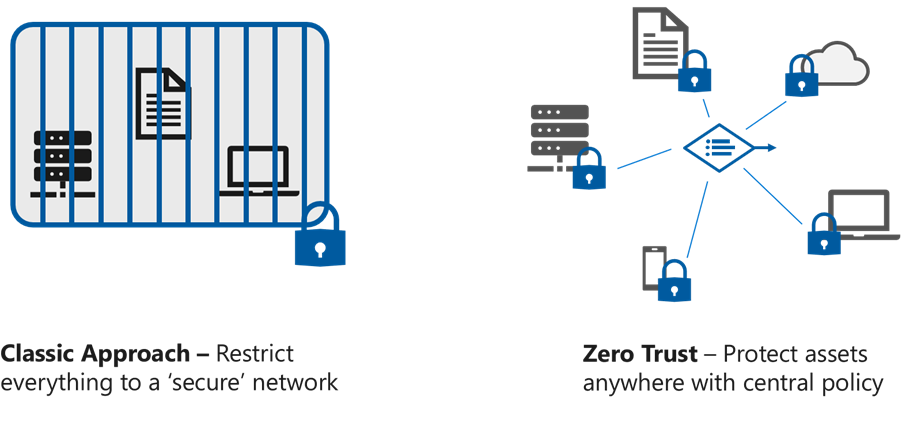
Some of the earliest formal work on what we now call Zero Trust started around in a security consortium known as the Jericho Forum (which later merged into The Open Group Security Forum). This started as a group of like-minded CISOs wrestling with the limitations of the dominant and unquestioned philosophy of securing all resources by putting them on a ‘secure’ network behind a security perimeter.
The Jericho Forum promoted a new concept of security called de-perimeterisation that focused on how to protect enterprise data flowing in and out of your enterprise network boundary instead of striving to convince users and the business to keep it on the corporate network. This shift to “secure assets where they are” proved quite prophetic, especially when you consider that the original iPhone didn’t release until 2007 (which triggered the sea change of user preferences shaping enterprise technology decisions that is now just normal).
One CISO: Our network has become a mini-internet
A lot has changed since the days when we knew exactly what is on our network. A CISO of a multinational organization once remarked that its corporate network has become a miniature internet. With hundreds of thousands of devices connected at all hours including many unmanaged devices, the network has lost its ability to create trust for the devices on it. While network controls still have a place in a security strategy, they are no longer the foundation upon which we can build the assurances we need to protect business assets.
In this blog, we will examine how these concepts (captured succinctly in the Jericho® Forum Commandments) have helped shape what has become Zero Trust today, including Microsoft’s Zero Trust vision and technology.
Accepting de-perimeterisation frees security architects and defenders to re-think their approach to securing data. Securing data where it is (vs. artificially confining it to a network) also naturally more aligned to the business and enables the business to securely operate.
While security folks love the idea of keeping an organization safe by blocking every risk, the real world needs flexible solutions to gracefully handle the grey areas and nuances.
The classic approach of applying security exclusively at the network level limits what context security sees (e.g. what the user/application trying to do at this moment) and usually limits the response options to only blocking or allowing.
This is comparable to a parent filtering content for their children by blocking specific TV channels or entire sites like YouTube. Just like blocking sites in security, the rough grain blocking causes issues when kids need YouTube to do their online classes or find websites and other TV channels with inappropriate content.
We have found that it’s better to offer users a safe path to be productive rather than just blocking a connection or issuing an “access denied.” Microsoft has invested heavily in zero trust to address both the usability and security needs in this grey area
While it’s tempting to think “but it’s just safer if we block it entirely”, beware of this dangerous fallacy. Users today control how they work and they will find a way to work in a modern way, even if they must use devices and cloud services completely outside the control of IT and security departments. Additionally, attackers are adept at infiltrating approved communication channels that are supposed to be safe (legitimate websites, DNS (Domain Name Servers) traffic, email, etc.).
The Jericho Forum recognized emerging trends that are now simply part of normal daily life. As we make security investments in the future, we must embrace new ways of working, stop confining assets unnaturally to a network they do not belong on, and secure those assets and users where they are and wherever they go.
Learn more about Why Zero Trust. To learn more about Microsoft Security solutions visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.