Patch me if you can: Cyberattack Series
The Microsoft Incident Response team takes swift action to help contain a ransomware attack and regain positive administrative control of the customer environment.

This blog post is part of the Microsoft Intelligent Security Association guest blog series. Learn more about MISA.
Computer-aided design (CAD) files are used by design professionals in the manufacturing, engineering, architecture, surveying, and construction industries. These highly valuable files contain confidential information and form their core intellectual property (IP).
Loss of such proprietary information to an outsider or a competitor can have disastrous effects leading to a loss in sales, market share, and reduced profit margins. However, such industries often collaborate with other design partners or vendors or they share their design parts with smaller manufacturers. Product blueprints and designs are regularly exchanged, both within and outside the organization’s network boundaries. In such cases, there is a high possibility of a data leak.
Data loss or theft can occur in any one of the following ways:
Organizations may use encryption programs, secure file transfer protocol, and other access control methods to prevent data leaks and data theft. However, once these files leave their original repository it is very difficult to keep track of their usage.
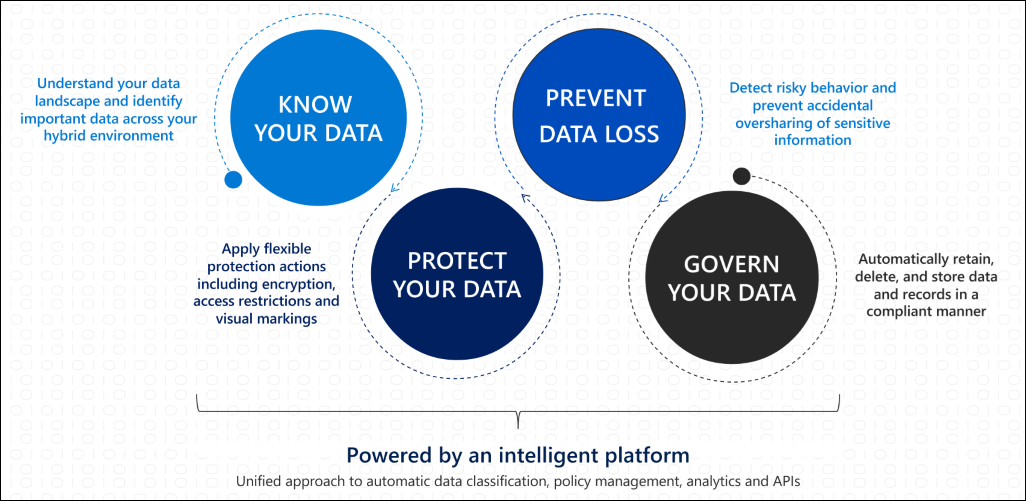
To solve this problem, organizations have invested in Microsoft Information Protection (MIP) an intelligent, unified, and extensible solution to protect sensitive data across your enterprise—in Microsoft 365 cloud services, on-premises, third-party software as a service (SaaS) applications, and more. MIP provides a unified set of capabilities to know your data, protect your data, and help prevent data loss across Microsoft 365 apps (such as Word, PowerPoint, Excel, and Outlook) and services (such as Teams, SharePoint, and Exchange).
When you have already invested in an excellent information protection system, it isn’t a prudent decision to go in for another information protection system. But what can be done to solve the above problem?
SECUDE has integrated their HALOCAD solution with Microsoft’s MIP SDK which extends the data protection beyond the organization’s IT perimeter. HALOCAD not only integrates as a MIP SDK add-in into the content authoring environment but also works as an add-on into the content repository and implements information protection policies across supported repositories.
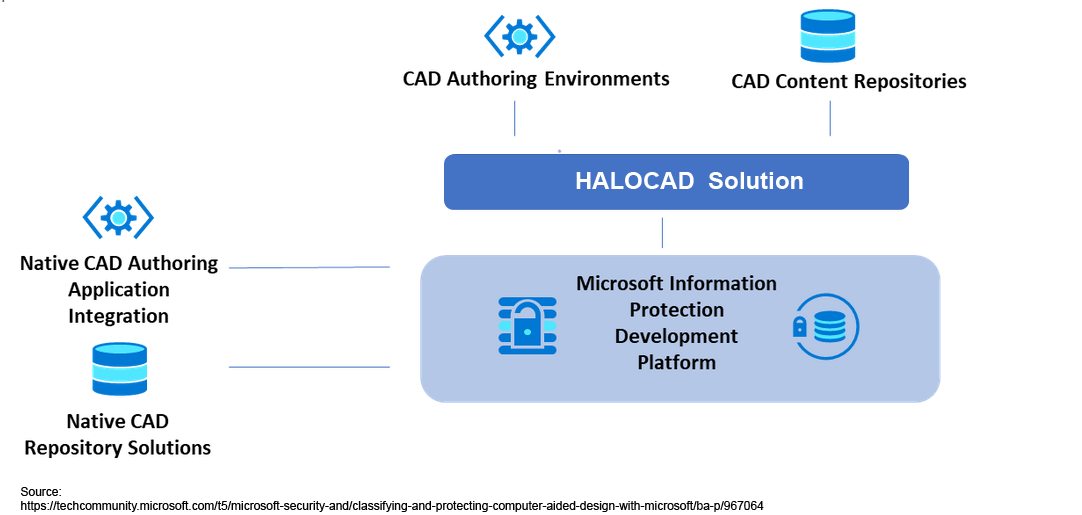
With over two decades of experience in the data security field, SECUDE has a track record of adding value to the MIP capabilities to SAP environments, especially when exporting sensitive information from SAP environments. HALOCAD helps to seamlessly leverage MIP labeling templates for CAD files and does so simply and cost-effectively. It also applies the label to the content repository where the engineering processes for storing and sharing CAD files are kept.
Let us look at a hypothetical scenario on how data collaboration happens between the engineering team and the external third party vendors and suppliers with HALOCAD and MIP:

In the above scenario, the design files move seamlessly across the supply chain with MIP sensitivity labels applied automatically and user privileges as defined by the organization.
The user is the designer who owns the design files. Based on the user privilege defined, the designer can view, edit, copy, print, and export the files
The user is an engineer who consumes the design file shared with them by the engineering team. The engineer can view and edit the files. They can make modifications to the original file and share it. They do not have the privilege to copy, print, export, and use the snipping tool to make a copy.
In a typical manufacturing environment, the CAD drawings are shared with a lot of third-party partners and vendors across the supply chain for day-to-day operations. In this scenario, the partner who has purchased the SECUDE solution can only view the CAD files per the set privilege enforcement.
If an unauthorized user outside of the organization tries to open the CAD drawings, the files are encrypted, and he will not be able to open the file.
For more information about the HALOCAD solution, please visit the SECUDE HALOCAD website. You can also find HALOCAD in Azure Marketplace.
To learn more about the Microsoft Intelligent Security Association (MISA), visit our website where you can learn about the MISA program, product integrations, and find MISA members. Visit the video playlist to learn about the strength of member integrations with Microsoft products.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.