


Microsoft Defender
Microsoft Defender helps prevent, detect, and respond to attacks across devices, identities, apps, email, data, workloads, and clouds. Explore threat intelligence, capabilities, and real-world guidance to help you get more out of Defender.
Refine results
Topic
Products and services
Publish date
-
 Cybersecurity hygiene is about maintaining cyberhealth by developing and implementing a set of tools, policies, and practices to increase your organization’s resiliency in the face of attacks and exploits.
Cybersecurity hygiene is about maintaining cyberhealth by developing and implementing a set of tools, policies, and practices to increase your organization’s resiliency in the face of attacks and exploits. -

Insights from the MITRE ATT&CK-based evaluation of Windows Defender ATP
In MITRE’s evaluation of endpoint detection and response solutions, Windows Defender Advanced Threat Protection demonstrated industry-leading optics and detection capabilities. -

Windows Defender ATP device risk score exposes new cyberattack, drives Conditional access to protect networks
Several weeks ago, the Windows Defender Advanced Threat Protection (Windows Defender ATP) team uncovered a new cyberattack that targeted several high-profile organizations in the energy and food and beverage sectors in Asia. -

How to help maintain security compliance
This is the last post in our eight-blog series on deploying Intelligent Security scenarios. -
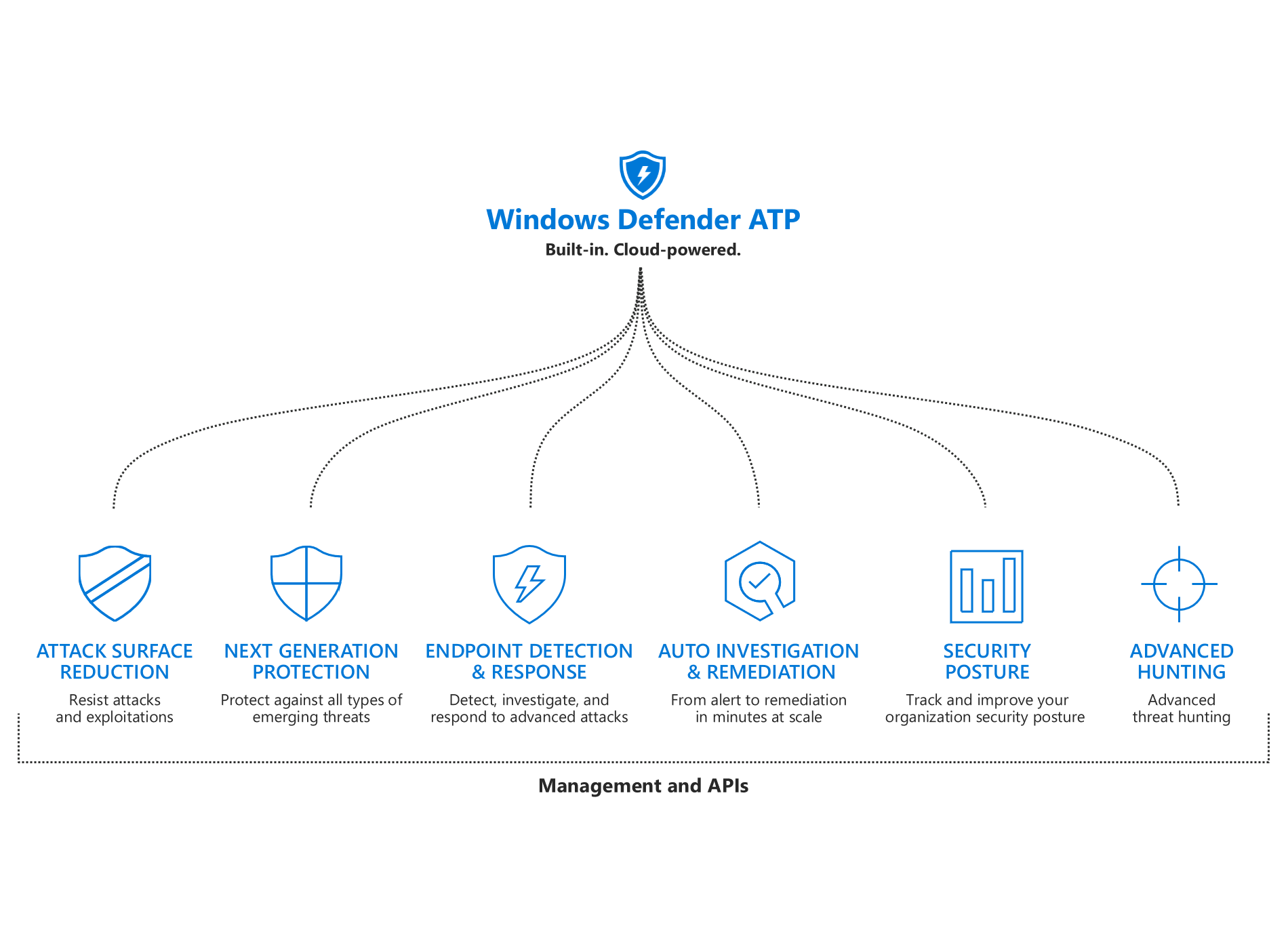
What’s new in Windows Defender ATP
We added new capabilities to each of the pillars of Windows Defender ATP’s unified endpoint protection platform: improved attack surface reduction, better-than-ever next-gen protection, more powerful post-breach detection and response, enhanced automation capabilities, more security insights, and expanded threat hunting. -

The evolution of Microsoft Threat Protection, November update
Learn about the latest enhancements to Microsoft Threat Protection, the premier solution for securing the modern workplace across identities, endpoints, user data, apps, and infrastructure. -

CISO series: Lessons learned—4 priorities to achieve the largest security improvements
In this blog, Jonathan Trull shares methods he uses to prioritize where and how he spends his resources to achieve the largest security improvements. -

CISO series: Build in security from the ground up with Azure enterprise
Shawn Anderson, a former CISO, now meets with CISOs every other week to answer their questions on moving to the cloud and where to start. -

How to share content easily and securely
This post is part of our blog series on deploying Intelligent Security scenarios. -

CISO series: Partnering with the C-Suite on cybersecurity
In my last blog, we looked at five communication techniques that can help engage business managers in the work of cybersecurity. -

How Office 365 learned to reel in phish
Find out how Office 365 learned to mitigate phishing attacks. -
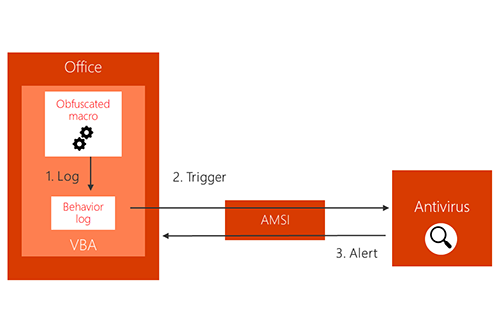
Office VBA + AMSI: Parting the veil on malicious macros
As part of our continued efforts to tackle entire classes of threats, Office 365 client applications now integrate with Antimalware Scan Interface (AMSI), enabling antivirus and other security solutions to scan macros and other scripts at runtime to check for malicious behavior.





