The agentic SOC—Rethinking SecOps for the next decade
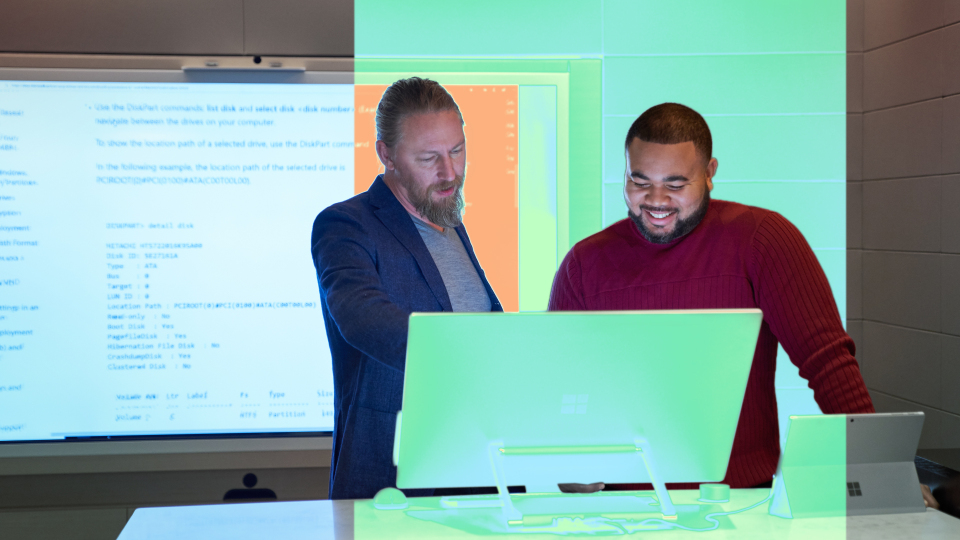
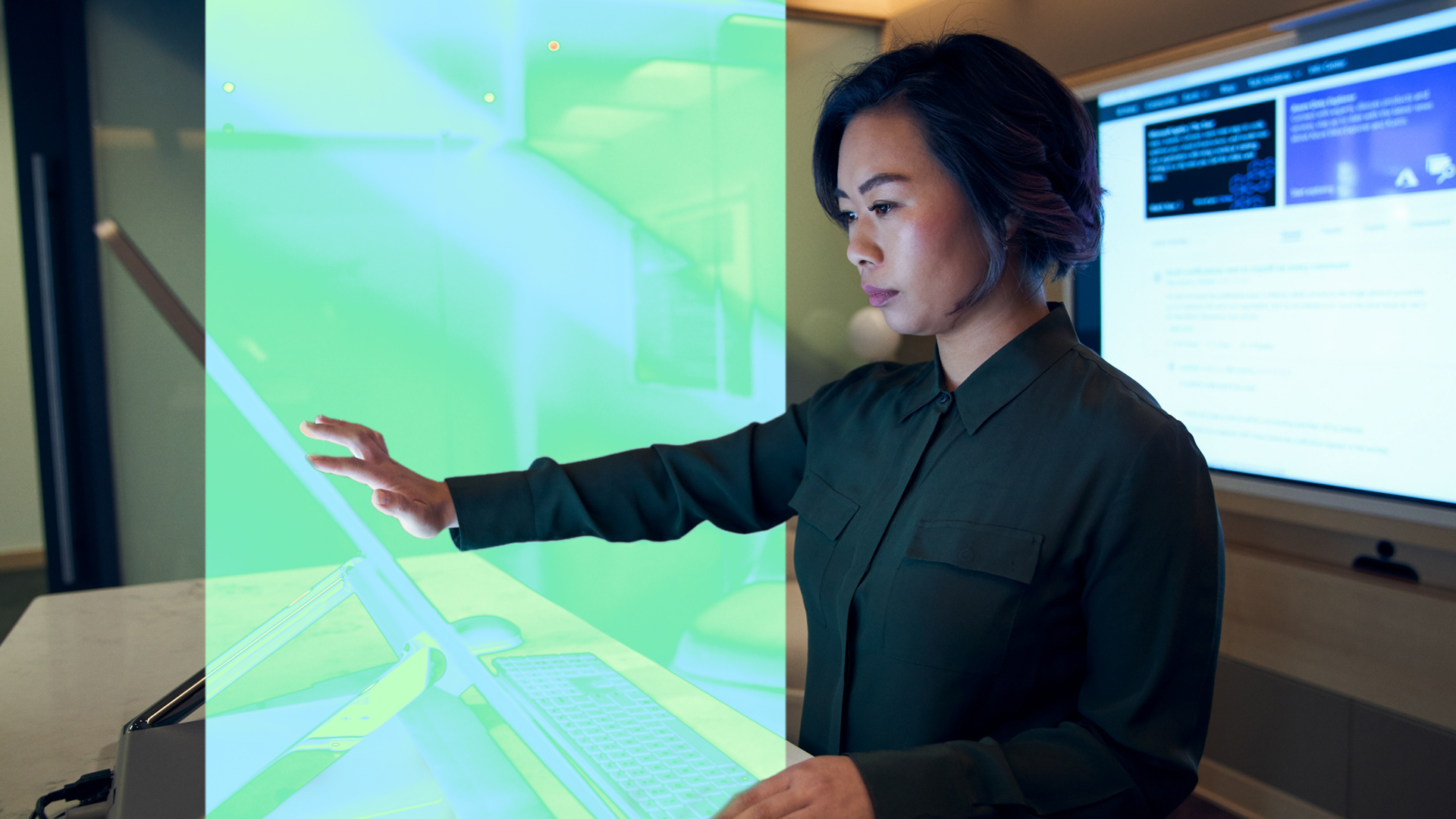
In the SOC of the future, autonomous defense moves at machine speed, agents add context and coordination, and humans focus on judgment, risk, and outcomes.


Microsoft Security Copilot agents help you detect, investigate, and respond faster. Stay up to date on how AI is reshaping security, learn best practices, and explore new capabilities.