

Security operations
Explore the latest insights, tools, frameworks, and developments in security operations (SecOps).
Refine results
Topic
Products and services
Publish date
-
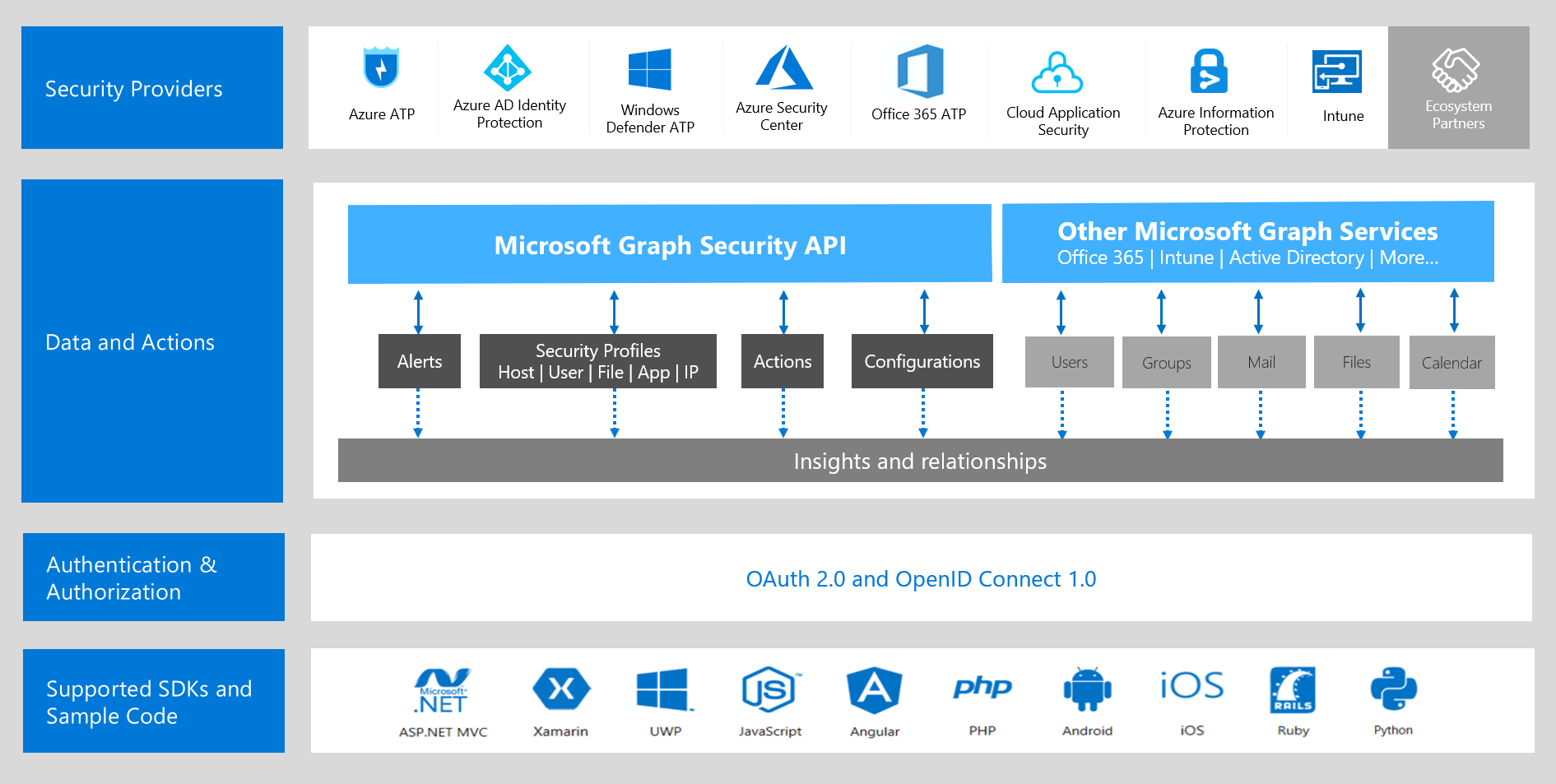
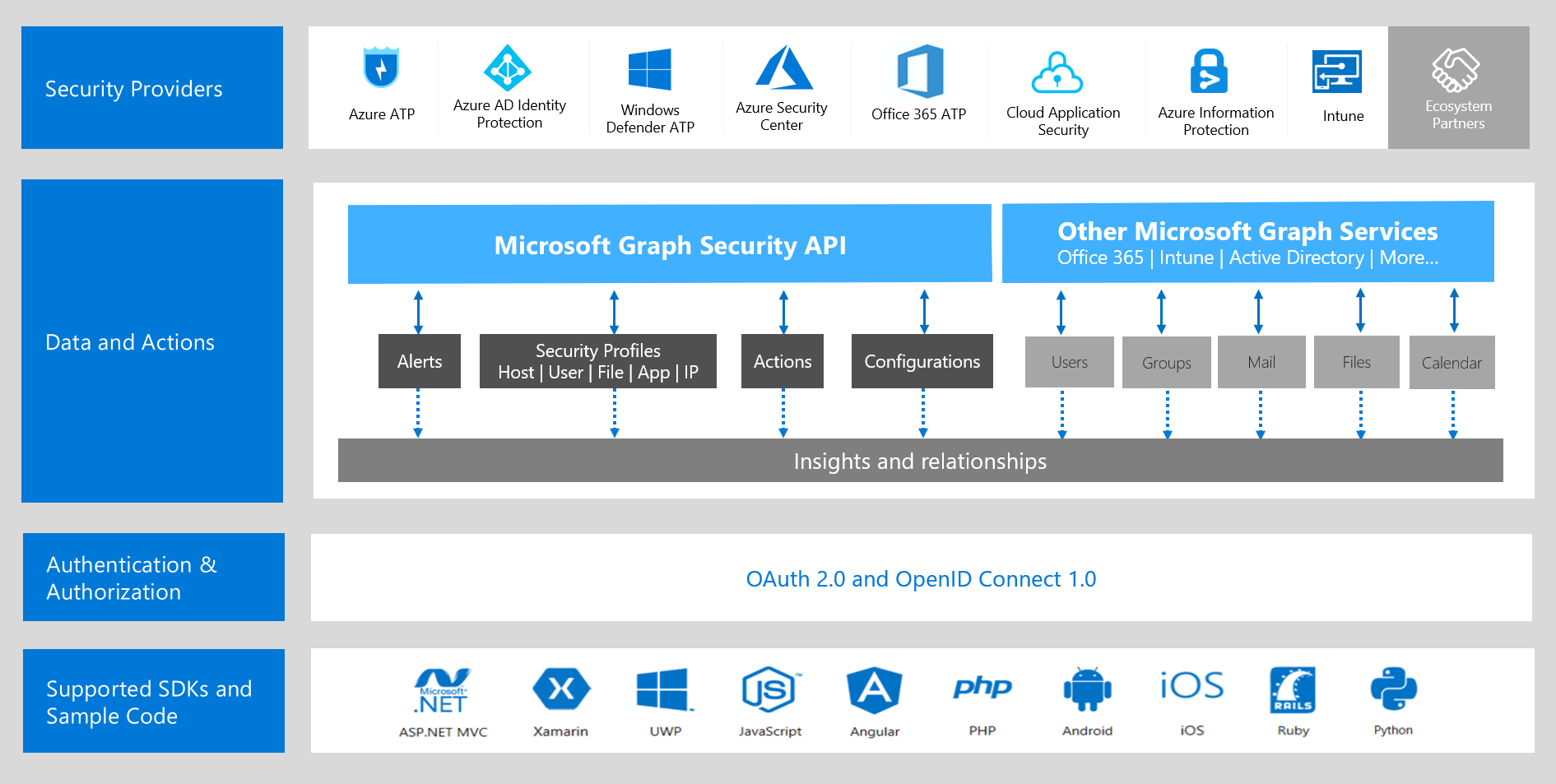 Most organizations deal with high volumes of security data and have dozens of security solutions in their enterprise, making the task of integrating various products and services daunting and complex.
Most organizations deal with high volumes of security data and have dozens of security solutions in their enterprise, making the task of integrating various products and services daunting and complex. -

Microsoft to deliver new products and strategies for security innovation at 2018 RSA Conference
At the 2018 RSA Conference, our senior leaders will dissect modern cyber defense strategies, and reveal new products to detect and block cyber attacks when they happen. -

Accelerate your security deployment with FastTrack for Microsoft 365
This blog is part of a series that responds to common questions we receive from customers about Microsoft 365 Security and Enterprise Mobility + Security. -

Tips for getting started on your security deployment
This blog is part of a series that responds to common questions we receive from customers about how to most effectively deploy Microsoft 365 Security. -
How to mitigate rapid cyberattacks such as Petya and WannaCrypt
Because of how critical security hygiene issues have become and how challenging it is for organizations to follow the guidance and the multiple recommended practices, Microsoft is taking a fresh approach to solving them. -

How a national cybersecurity agency can help avoid a national cybersecurity quagmire
This last October we saw more countries than ever participate in initiatives to raise cybersecurity awareness. -

Developing an effective cyber strategy
The word strategy has its origins in the Roman Empire and was used to describe the leading of troops in battle. -
Overview of Petya, a rapid cyberattack
In the first blog post of this 3-part series, we introduced what rapid cyberattacks are and illustrated how they are different in terms of execution and outcome. -
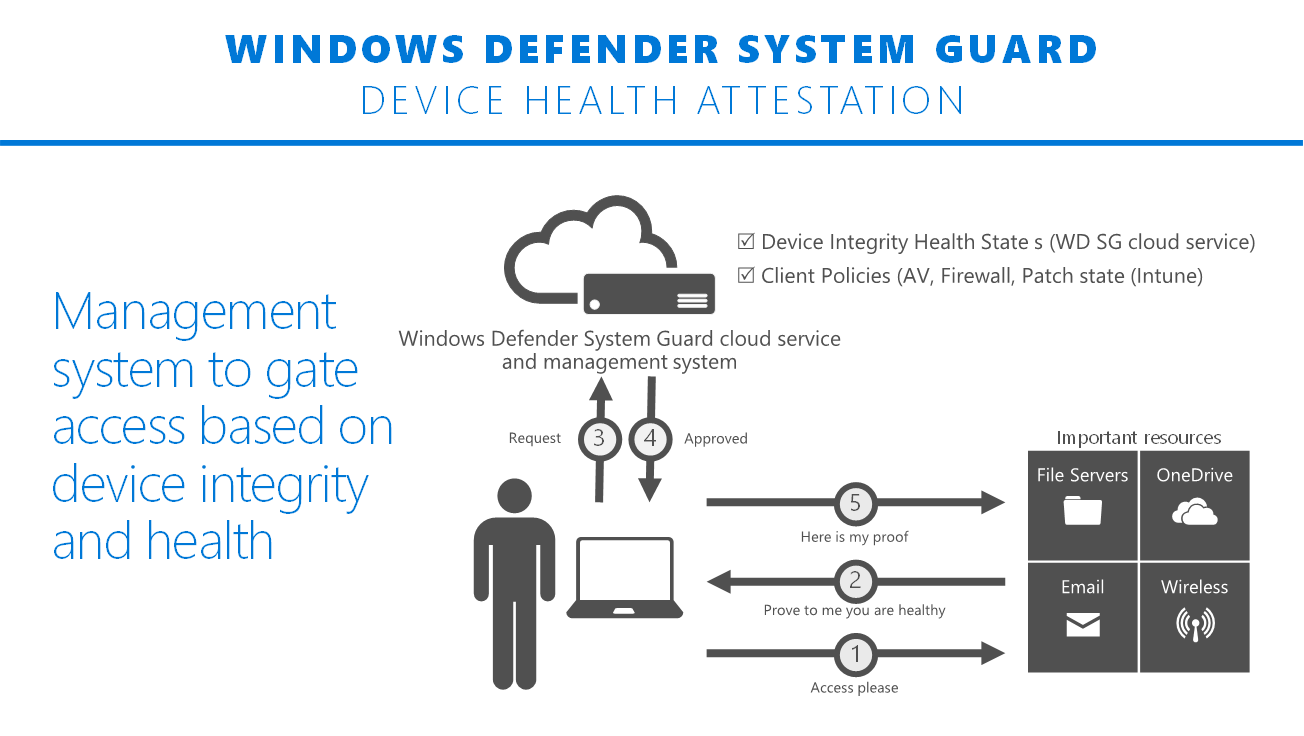
Hardening the system and maintaining integrity with Windows Defender System Guard
Just a few weeks ago at Ignite we announced Windows Defender System Guard, which ships in Windows 10, version 1709, also known as the Fall Creators Update. -

Stepping up protection with intelligent security
With digital transformation, technology becomes increasingly central to every business and organization. -
New IIS functionality to help identify weak TLS usage
IIS logs can already be used to correlate client IP address, user agent string, and service URI. -
Top 5 best practices to automate security operations
This post is authored by Jonathan Trull, Worldwide Executive Cybersecurity Advisor, Enterprise Cybersecurity Group.





