


Threat intelligence
The Microsoft Threat Intelligence community is made up of world-class experts, security researchers, analysts, and threat hunters who analyze 100 trillion signals daily to discover threats and deliver timely and timely, relevant insight to protect customers. See our latest findings, insights, and guidance.
Refine results
Topic
Products and services
Publish date
-
 To keep government agencies secure in the cloud, we must keep pace and stay ahead of cyber attackers by defending the cyber supply chain with Microsoft Azure.
To keep government agencies secure in the cloud, we must keep pace and stay ahead of cyber attackers by defending the cyber supply chain with Microsoft Azure. -

Insights from one year of tracking a polymorphic threat
We discovered the polymoprhic threat Dexphot in October 2018. -

Microsoft works with researchers to detect and protect against new RDP exploits
The new exploit attacks show that BlueKeep will be a threat as long as systems remain unpatched, credential hygiene is not achieved, and overall security posture is not kept in check. -

Top 6 email security best practices to protect against phishing attacks and business email compromise
What should IT and security teams be looking for in an email security solution to protect all their users, from frontline workers to the C-suite? Here are 6 tips to ensure your organization has a strong email security posture. -

Guarding against supply chain attacks—Part 1: The big picture
Paying attention to every link in your supply chain is vital to protect your assets from supply chain attacks. -
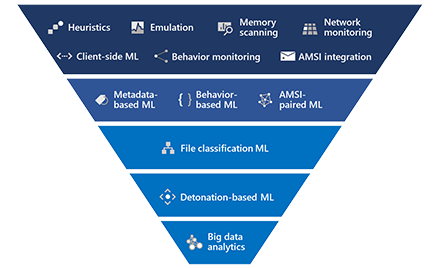
In hot pursuit of elusive threats: AI-driven behavior-based blocking stops attacks in their tracks
Two new machine learning protection features within the behavioral blocking and containment capabilities in Microsoft Defender ATP specialize in detecting threats by analyzing behavior, adding new layers of protection after an attack has started running. -

TLS version enforcement capabilities now available per certificate binding on Windows Server 2019
Microsoft is pleased to announce a powerful new feature in Windows to make your transition to a TLS 1. -

Bring your own LOLBin: Multi-stage, fileless Nodersok campaign delivers rare Node.js-based malware
A new fileless malware campaign we dubbed Nodersok delivers two very unusual LOLBins to turn infected machines into zombie proxies. -

Deep learning rises: New methods for detecting malicious PowerShell
We adopted a deep learning technique that was initially developed for natural language processing and applied to expand Microsoft Defender ATP’s coverage of detecting malicious PowerShell scripts, which continue to be a critical attack vector. -

One simple action you can take to prevent 99.9 percent of attacks on your accounts
Learn about common vulnerabilities and what you can do to protect your company from attacks. -

From unstructured data to actionable intelligence: Using machine learning for threat intelligence
Machine learning and natural language processing can automate the processing of unstructured text for insightful, actionable threat intelligence. -

Protect against BlueKeep
DART offers steps you can take to protect your network from BlueKeep, the “wormable” vulnerability that can create a large-scale outbreak due to its ability to replicate and propagate.





