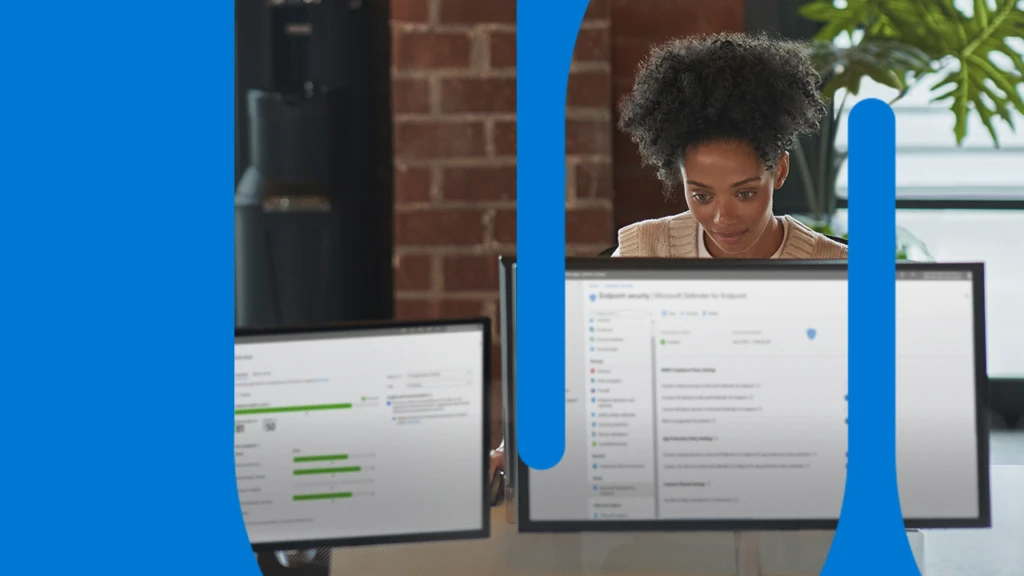
How comprehensive security simplifies the defense of your digital estate
End-to-end security is a modern, comprehensive approach to data protection that aligns data protection and incident response across devices, systems, and users. Read the blog post to explore why it’s an attractive option for organizations committed to strengthening their cybersecurity.