How Microsoft Defender protects high-value assets in real-world attack scenarios
High-value assets including domain controllers, web servers, and identity infrastructure are frequent targets in sophisticated attacks.


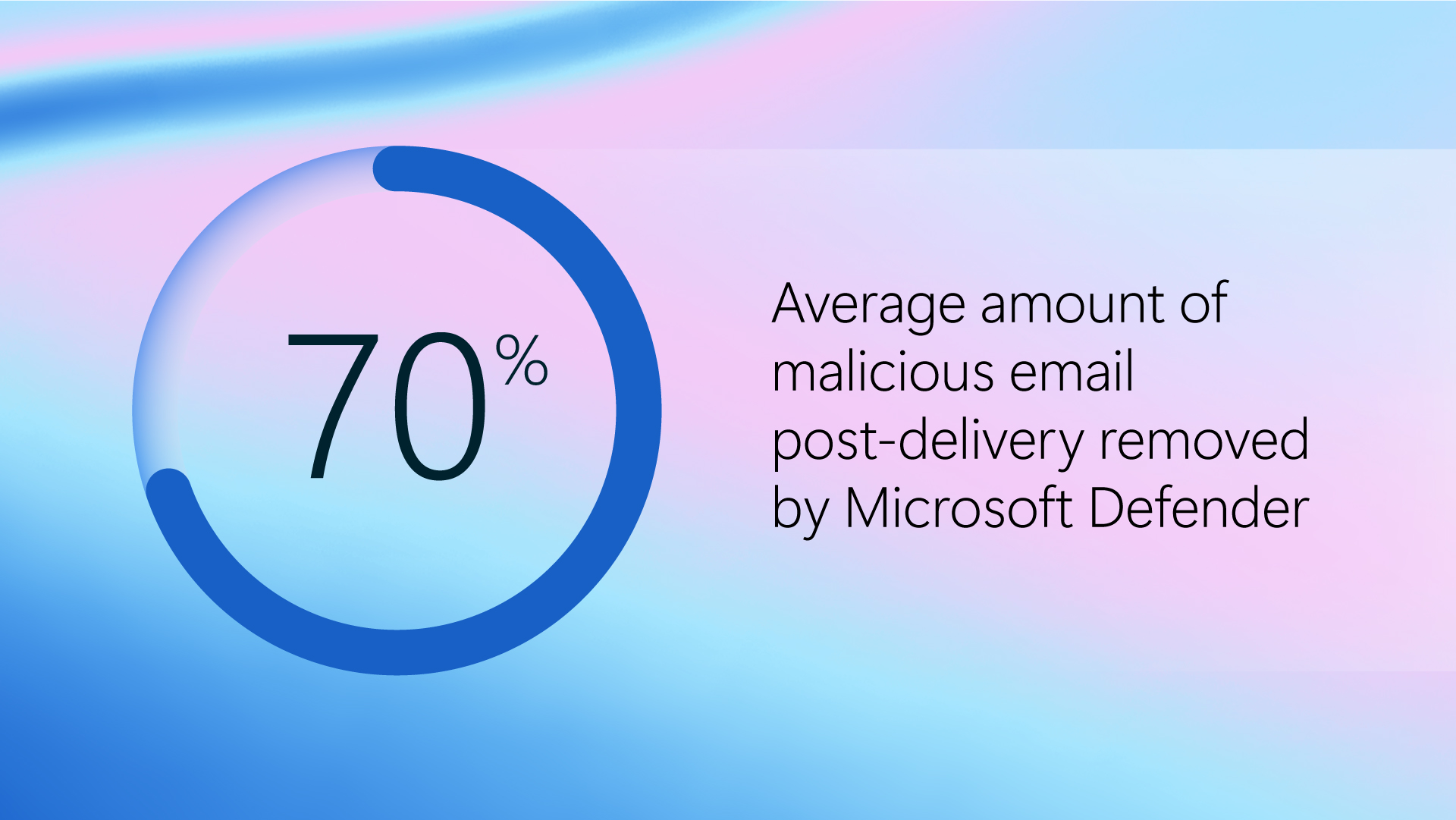
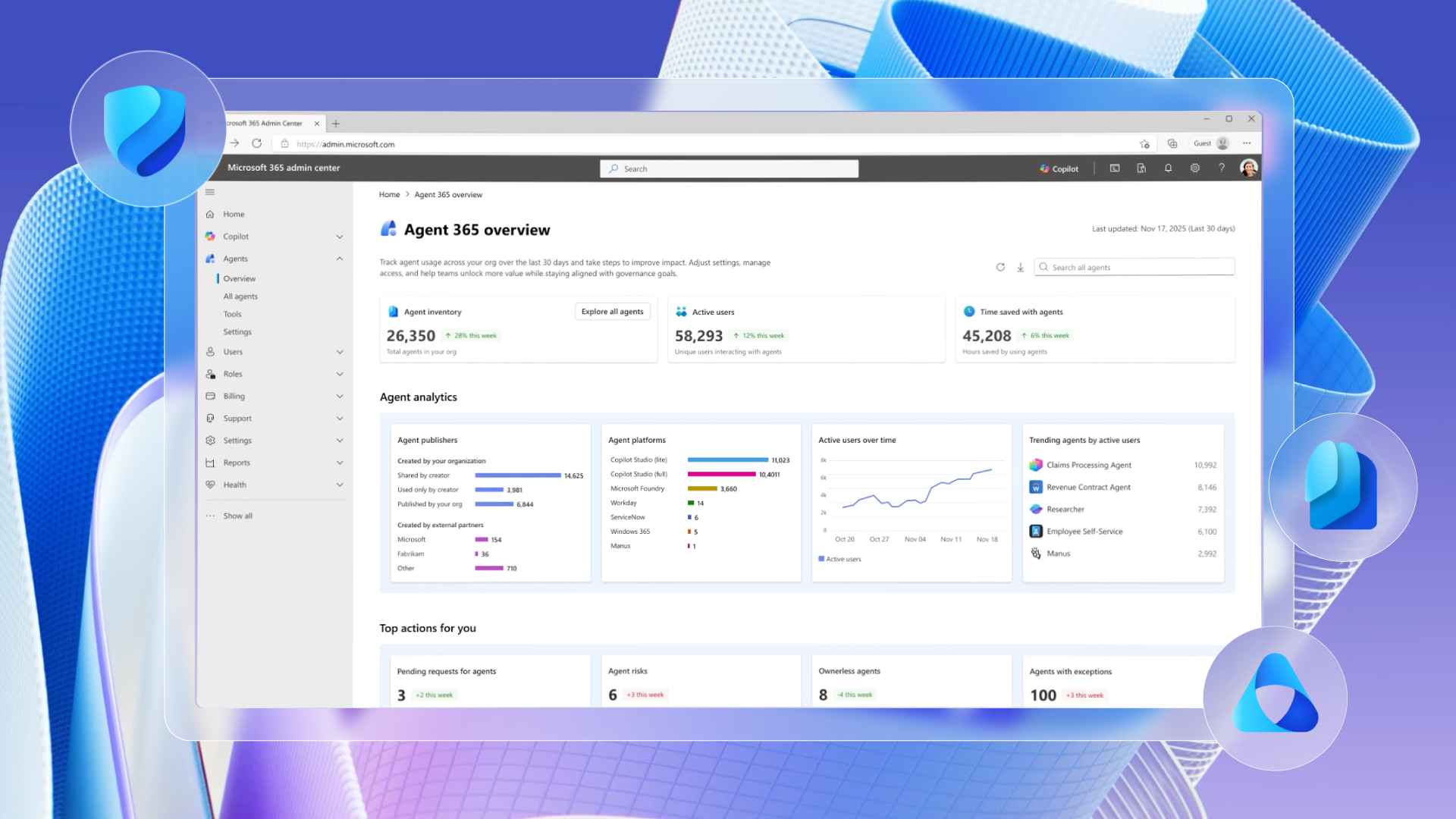
Microsoft Defender helps prevent, detect, and respond to attacks across devices, identities, apps, email, data, workloads, and clouds. Explore threat intelligence, capabilities, and real-world guidance to help you get more out of Defender.