


Microsoft Defender
Microsoft Defender helps prevent, detect, and respond to attacks across devices, identities, apps, email, data, workloads, and clouds. Explore threat intelligence, capabilities, and real-world guidance to help you get more out of Defender.
Refine results
Topic
Products and services
Publish date
-
 The trend towards increasingly sophisticated malware behavior, highlighted by the use of exploits and other attack vectors, makes older platforms so much more susceptible to ransomware attacks.
The trend towards increasingly sophisticated malware behavior, highlighted by the use of exploits and other attack vectors, makes older platforms so much more susceptible to ransomware attacks. -
Top 5 best practices to automate security operations
This post is authored by Jonathan Trull, Worldwide Executive Cybersecurity Advisor, Enterprise Cybersecurity Group. -
Windows Defender ATP machine learning: Detecting new and unusual breach activity
Microsoft has been investing heavily in next-generation security technologies. -
Tips for protecting your information and privacy against cybersecurity threats
This post is authored by Steven Meyers, security operations principal, Microsoft Cyber Defense Operations Center. -
Windows Defender ATP Fall Creators Update
UPDATE: For the latest information on Windows Defender ATP features and capabilities, read the blog post What’s new in Windows Defender ATP. -

Analysis of the Shadow Brokers release and mitigation with Windows 10 virtualization-based security
On April 14, a group calling themselves the Shadow Brokers caught the attention of the security community by releasing a set of weaponized exploits. -
The CISO Perspective: Putting lessons from WannaCrypt into practice to avoid future threats
Last month, customers and companies around the world were impacted by the WannaCrypt ransomware attack. -
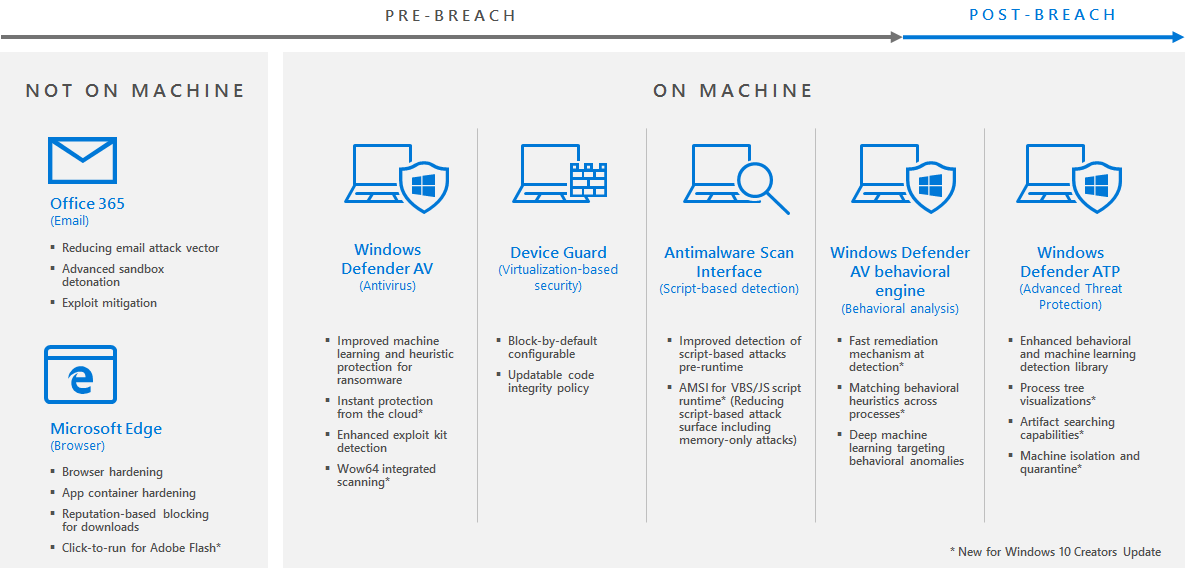
Windows 10 Creators Update provides next-gen ransomware protection
Multiple high-profile incidents have demonstrated that ransomware can have catastrophic effects on all of us. -
How the Asia-Pacific region is advancing cybersecurity
Earlier this year, my team and I had the great privilege and pleasure of spending several days in Japan, participating in the Information Technology Promotion Agency (IPA) Symposium. -
Use Enterprise Threat Detection to find “invisible” cyberattacks
This post is authored by Roberto Bamberger, Principal Consultant, Enterprise Cybersecurity Group. -
The two-pronged approach to detecting persistent adversaries
Advanced Persistent Threats use two primary methods of persistence: compromised endpoints and compromised credentials.





