

Device management
Device management allows organizations to secure, and maintain devices like virtual machines, earn the latest in device management and how solutions like Microsoft Intune and Microsoft Entra help keep devices secure, up to date, and compliant.
Refine results
Topic
Threat intelligence
Products and services
Publish date
-
 Microsoft maintains a continuous effort to protect its platforms and customers from fraud and abuse.
Microsoft maintains a continuous effort to protect its platforms and customers from fraud and abuse. -

How cyberattackers exploit domain controllers using ransomware
Read how cyberattackers exploit domain controllers to gain privileged system access where they deploy ransomware that causes widespread damage and operational disruption. -

How Microsoft Defender for Office 365 innovated to address QR code phishing attacks
This blog examines the impact of QR code phishing campaigns and the innovative features of Microsoft Defender for Office 365 that help combat evolving cyberthreats. -

New Microsoft Security innovations expand multicloud visibility and enhance multiplatform protection
Gain greater visibility into your multicloud environments to better understand your security posture, minimize risk, and detect and respond to threats in real time. -

Introducing security for unmanaged devices in the Enterprise network with Microsoft Defender for IoT
Microsoft Defender IoT is generally available to help organizations challenged with securing unmanaged Internet of Things devices connected to the network. -

Securing your IoT with Edge Secured-core devices
To simplify your IoT security journey, today, we’re announcing the availability of Windows IoT Edge Secured-core devices available in the Azure Certified Device catalog from Lenovo, ASUS and AAEON, additionally we’re also announcing the availability of devices that meet the Microsoft sponsored Edge Compute Node protection profile which is governed with industry oversight, from Scalys and Eurotech. -

Secure unmanaged devices with Microsoft Defender for Endpoint now
New Microsoft Defender for Endpoint capabilities let organizations discover and secure unmanaged workstations, mobile devices, servers, and network devices. -

Blue Cedar partners with Microsoft to combat BYOD issues
IT and security teams have been searching for a solution to accommodate BYOD that won’t compromise network security. -

Cybersecurity best practices to implement highly secured devices
If an internet-connected device performs a non-critical function, why does it need to be highly secured? Because any device can be the target of a hacker, and any hacked device can be weaponized. -

Delivering major enhancements in Windows Defender Application Control with the Windows 10 May 2019 Update
With the Windows 10 May 2019 Update we delivered several important features for Windows Defender Application Control. -

Windows Defender ATP has protections for USB and removable devices
We recommend a layered approach for device control security, which incorporates multiple avenues of protection, including each of the above. -
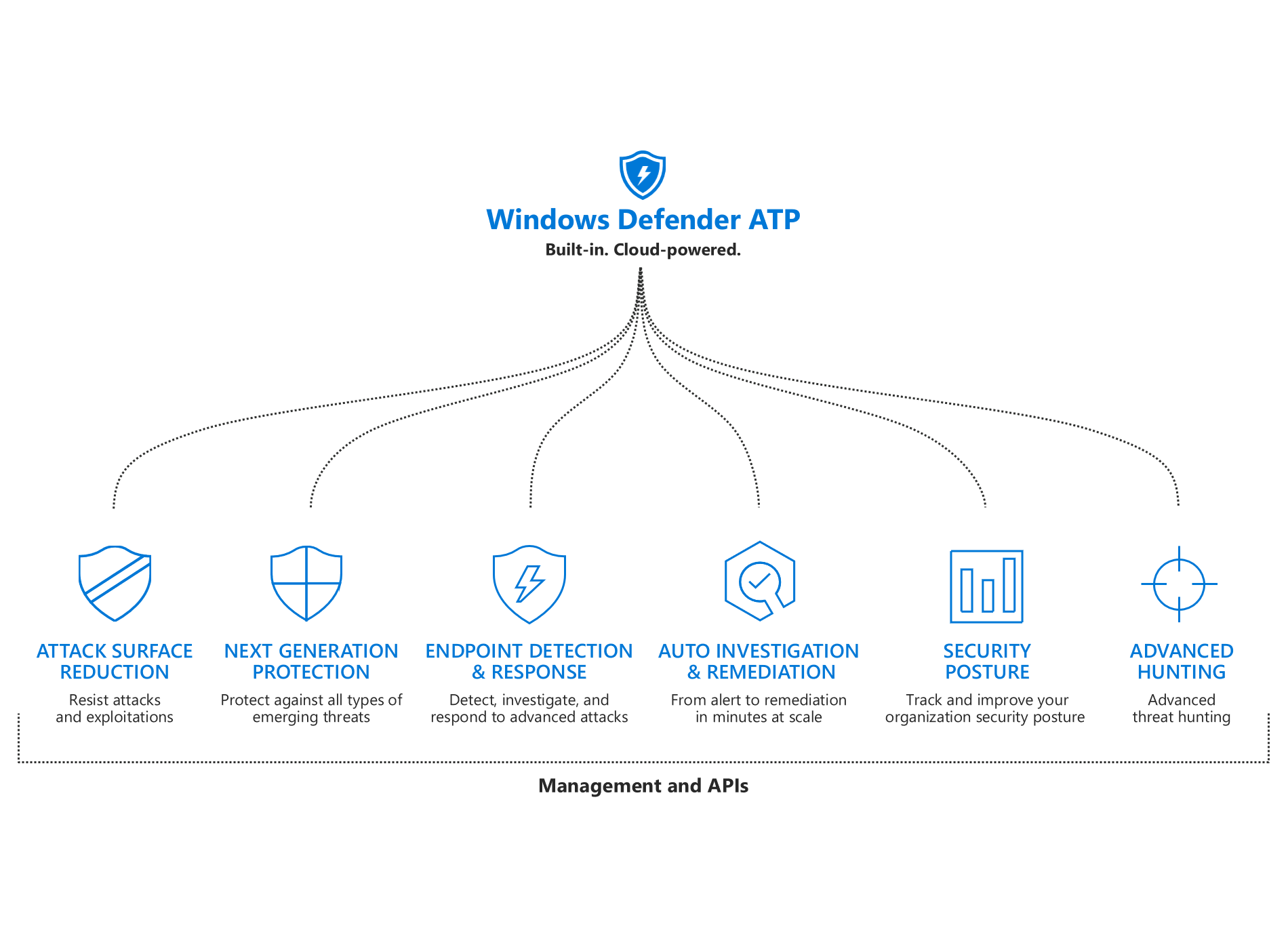
What’s new in Windows Defender ATP
We added new capabilities to each of the pillars of Windows Defender ATP’s unified endpoint protection platform: improved attack surface reduction, better-than-ever next-gen protection, more powerful post-breach detection and response, enhanced automation capabilities, more security insights, and expanded threat hunting.




