Post Doc Researcher
Microsoft Research India (MSR India) is inviting applications for Postdoctoral Researcher positions. The postdoc program at MSR India provides postdoctoral researchers an opportunity to work on impactful research problems while collaborating closely with Microsoft researchers…
SABER: Scaling-Aware Best-of-N Estimation of Risk
Scaling-Aware Best-of-N Estimation of Risk A Python package for predicting large-scale adversarial risk in Large Language Models under Best-of-N sampling. Paper: https://arxiv.org/pdf/2601.22636 (opens in new tab) Standard LLM safety evaluations use single-shot (ASR@1) metrics,…
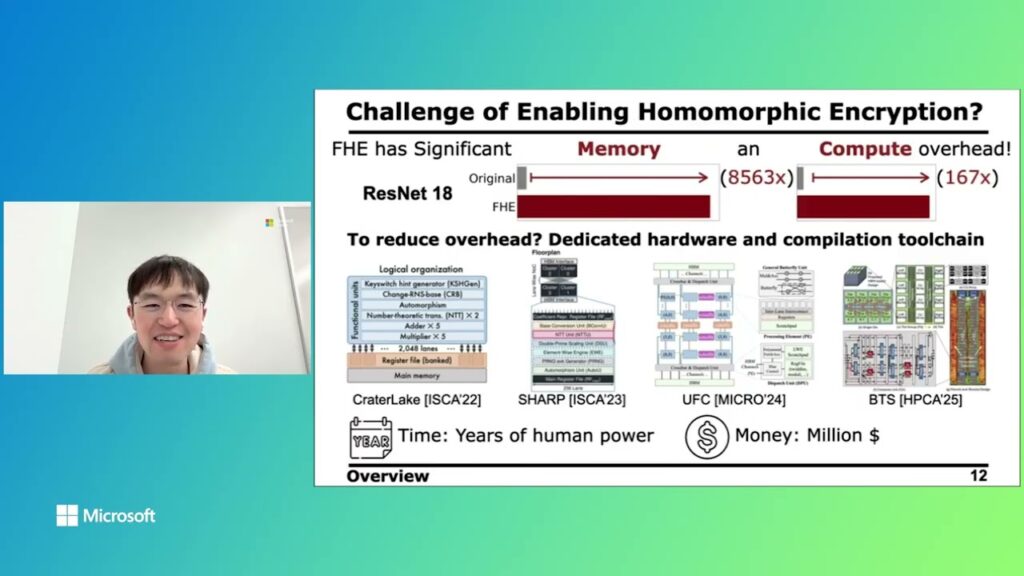
CROSS — Leveraging AI ASICs for Homomorphic Encryption
Artificial Intelligence (AI) is driving a new industrial revolution, transforming human workflows increasingly into digital tokens, i.e., tokenizing the entire world. However, this transformation exposes sensitive data at an unprecedented scale, leading to heavy privacy…
Research Intern – AI Safety and Security
Protecting large language models (LLMs) from malicious inputs is critical. LLMs can also be used to protect users from malicious attacks. The Deep Learning Team in Microsoft Research – Redmond is seeking Research Interns interested…