Towards a Unified Bayesian Model for Cyber Security
With the realisation that Cyber attacks present a significant risk to an organisation’s reputation, efficiency, and profitability, there has been an increase in the instrumentation of networks; from collecting netflow data at routers, to host-based…
Cryptography for the post-quantum world with Dr. Brian LaMacchia
Episode 38, August 22, 2018 You know those people who work behind the scenes to make sure nothing bad happens to you, and if they’re really good, you never know who they are because nothing…
Verification and Secure Systems
Bugs in security-critical system software already cost society billions of dollars, and the need for secure software is increasing as more devices are connected to the Internet. This session will outline the security needs of…
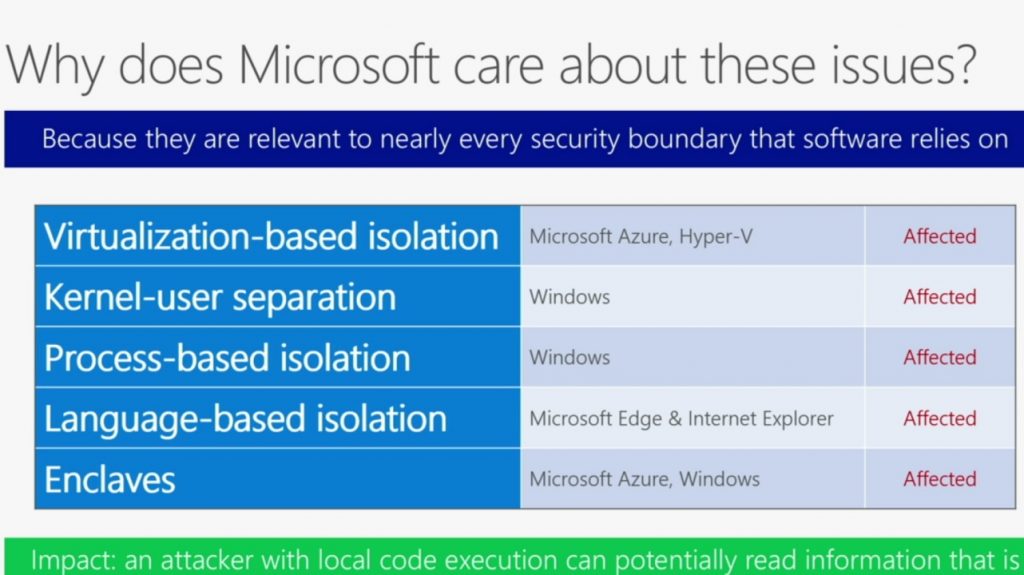
CPU & DRAM Bugs: Attacks & Defenses
In the quest for higher performance, modern CPUs make heavy use of speculative execution. Unfortunately, speculative execution opens the possibility of side-channel attacks in which malicious parties can read the memory of co-located processes, OSes,…
Tech Showcase: Confidential AI: Secure Multi-Party Artificial Intelligence
This project proposes a combination of new secure hardware for acceleration of machine learning (including custom silicon and GPUs), and cryptographic techniques to limit or eliminate information leakage in multi-party AI scenarios. This project is…
Confidential Computing
Confidential computing allows users to upload encrypted code and data to the cloud and get encrypted results back with guaranteed privacy. Confidential computing means cloud providers can’t see customers’ secrets even if cloud administrators are…
Tech Showcase: High-Fidelity Network Validation for Cloud Scale Networks
We propose a platform to validate networks with high-fidelity emulations. On a computing cluster such as Azure, we run the full stack (including real operating system, software, and chip emulators) of each network device in…
Tech Showcase: Private Compute
Microsoft has established itself as a pioneer in trustworthy computing. Features such as Always Encrypted in SQL Server show how we continue to keep trust while making world-class products. We imagine a world where user…