PNW PLSE Workshop: Featured Talk: Continuously Integrated Verified Cryptography
The PNW PLSE workshop provides an opportunity for programming languages and software engineering researchers throughout the Pacific Northwest to meet, interact, and share work in progress as well as recent results. The meeting on May…
Trusted Platform Module (TPM) Reference implementation – 2.0 specification
This is a Microsoft Visual Studio solution that contains reference implementation of the TPM 2.0 Specification by TCG available at https://trustedcomputinggroup.org/tpm-library-specification (opens in new tab). See the TPMCmd/tpm/include/TpmTypes.h header for the exact revision/date of the TPM…
Cryptographic Program Obfuscation: Current Capabilities and Challenges
Cryptographic program obfuscation (CPO) enables the evaluation of obfuscated programs/circuits for non-encrypted inputs using cryptographic approaches based on standard (or almost standard) security assumptions. CPO is a hot topic of cryptography that has recently seen…
Picnic
“Picnic” is the code name for a post-quantum digital signature algorithm, using a uses what is called a zero-knowledge proof concept.
qTESLA
qTESLA is a collaboration between researchers and engineers at ISARA Corporation, Microsoft Research, Ondokuz Mayis University, Technische Universität Darmstadt, University SãoPaulo and the University of Washington, Tacoma. qTESLA is a family of efficient post-quantum digital…
FrodoKEM
The FrodoKEM post-quantum cryptography project is a collaboration between researchers and engineers at CWI, Google, McMaster University, Microsoft Research, NXP Semiconductors, Stanford University, and the University of Michigan. FrodoKEM is a family of conservative yet…
Supersingular Isogeny Key Encapsulation (SIKE)
SIKE and SIDH are insecure and should not be used. For more information, please refer to the SIKE team’s statement to NIST. Supersingular Isogeny Key Encapsulation (SIKE) is a post-quantum cryptography collaboration between researchers and engineers at Amazon, Florida…
Post-quantum Cryptography
Cryptography in the era of quantum computers The private communication of individuals and organizations is protected online by cryptography. Cryptography protects our information as it travels over and is stored on the internet—whether making a…
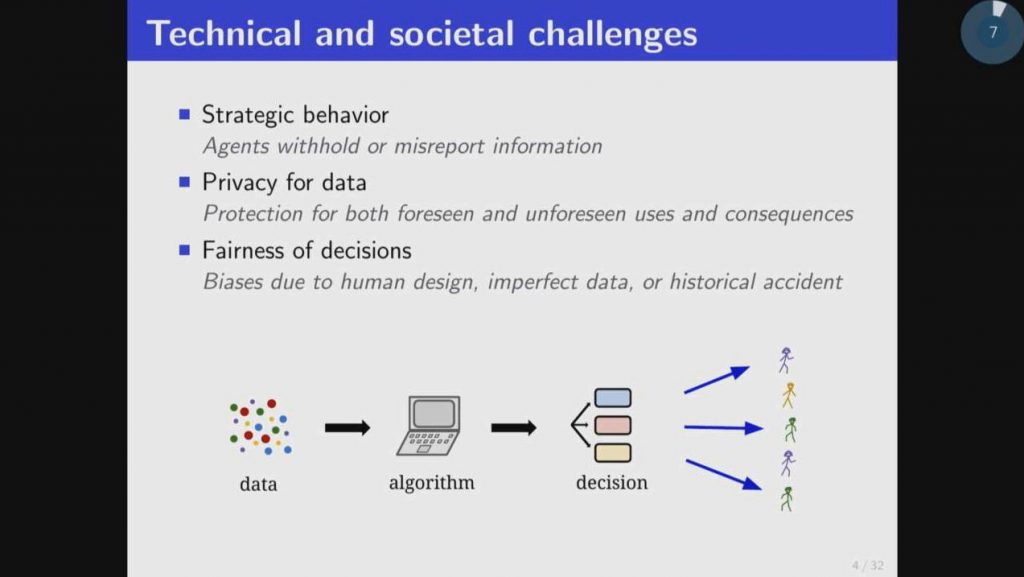
Acquiring and Aggregating Information in Societal Contexts
The modern world is full of algorithms that use data to make decisions. The data often come from people; the predictions or decisions often affect people. Yet classically, the study of e.g. learning algorithms does…