
Mapping the Cybersecurity Executive Order Milestones
 The recent Cybersecurity Executive Order lists July 11 as the first major deadline for all Federal civilian agencies to provide updated plans for adopting cloud technology and implementing a Zero Trust Architecture. To help agencies meet this immediate need and to accelerate their long-term journey towards secure cloud and Zero Trust, Microsoft has recently published our Zero Trust rapid modernization plan and Zero Trust Scenario Architectures. Based on insights from our own journey towards Zero Trust and decades of experience helping federal agencies, these resources present concrete next steps to help agencies meet aggressive EO timelines and improve their baseline cybersecurity posture so, together, we can answer the nation’s call to increased cyber resilience.
The recent Cybersecurity Executive Order lists July 11 as the first major deadline for all Federal civilian agencies to provide updated plans for adopting cloud technology and implementing a Zero Trust Architecture. To help agencies meet this immediate need and to accelerate their long-term journey towards secure cloud and Zero Trust, Microsoft has recently published our Zero Trust rapid modernization plan and Zero Trust Scenario Architectures. Based on insights from our own journey towards Zero Trust and decades of experience helping federal agencies, these resources present concrete next steps to help agencies meet aggressive EO timelines and improve their baseline cybersecurity posture so, together, we can answer the nation’s call to increased cyber resilience.
Deploying a proven three-phased modernization approach
Microsoft’s unique and comprehensive view of the cyber landscape allows us to simplify the complex in order to unlock the government’s full cyber capabilities. We have developed prescriptive guidance with each step of the journey designed to activate existing capabilities and optimize with new technologies so agencies can address sophisticated attacks with greater efficiency and efficacy than ever before.
At a high level, Microsoft recommends accelerating modernization by first focusing on identifying and monitoring risks. Organizations can get started by enabling single sign-on to applications, setting up conditional access to enforce MFA, and registering and provisioning devices to establish a dynamic asset inventory. This approach addresses several of the EO requirements and provides a solid foundation for additional phases. A key component to this phase is the implementation of identity solutions that most agencies already own, like Azure Active Directory (AD) single sign-on, and Azure Active Directory’s Application Proxy, which provides secure remote access to on-premises web applications. These capabilities offer high assurance authentication, connect existing on-premises infrastructure to the cloud, ensure every workload is assigned an identity, and provide better micro-segmentation and network security than is commonly achieved with VPNs.
Phase two builds on monitoring insights from the first phase to establish risk-prioritized actions. Adding a dynamic and risk-based context evaluation to authorization can be achieved through a simple and consistent centralized policy with Azure AD Conditional Access. Using a cloud-native, security information event management (SIEM) and security orchestration automated response (SOAR) solution like Azure Sentinel can provide additional insights through anomaly detection. Many agencies already have the capability to identify sensitive information in Office 365 and on-premises with Microsoft Information Protection. In phase two, agencies should focus on identifying this data more so than protecting it to address the EO requirements while also providing additional monitoring insights from the aggregation of sensitive data flows without impacting end users. Using Azure Virtual Desktop for remote administration via cloud SAW and segmenting privilege with cloud-only administrator accounts are also easy steps that significantly reduce risk.
The third phase is focused on increasing protection. Agencies can accomplish this by enforcing BYOD mobile device management (MDM) enrollment during authorization to provide an inventory of non-enterprise devices, proactively managing updates, patches, policies, and monitoring device health, and enabling additional telemetry and control with endpoint detection and response. Solutions like Azure Defender and Microsoft Cloud App Security provide deeper analytics and fine-grained control so agencies can gain greater visibility into cloud apps and services to control sessions and protect workloads in real-time.
Five reference architectures to demystify the Zero Trust journey
While reaching a high degree of Zero Trust maturity may initially seem daunting, many agencies are already well-positioned to adopt the three phases approach and reach upcoming milestones. Much of the technology required to execute the roadmap is already in place at many agencies — they simply need to activate and fine-tune existing capabilities.
To this end, Microsoft has identified five of the most impactful scenarios agencies should build towards across the three phases of modernization. The following reference architectures outline how to address those common Zero Trust scenarios and are mapped against key NIST requirements for Zero Trust while including other EO priorities such as endpoint detection and response (EDR), MFA, and continuous monitoring.
Scenario 1: Cloud-ready authentication apps
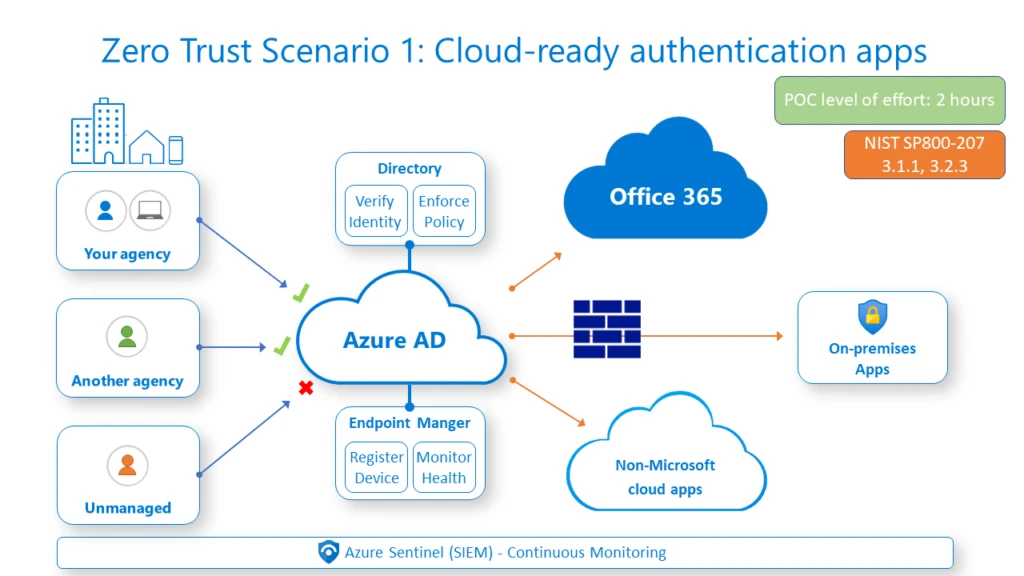
Modern authentication mechanisms are critical for securing SaaS applications by protecting identities, enforcing MFA requirements, and achieving comply-to-connect functionality. Many agencies are well on their way toward achieving secure baselines for SaaS using best practice approaches around ID configuration for Office 365, implementing strong MFA, and enforcing requirements with conditional access policies. This work can be easily extended to other SaaS applications and custom claims-based applications.
Scenario 2: Web apps with legacy authentication
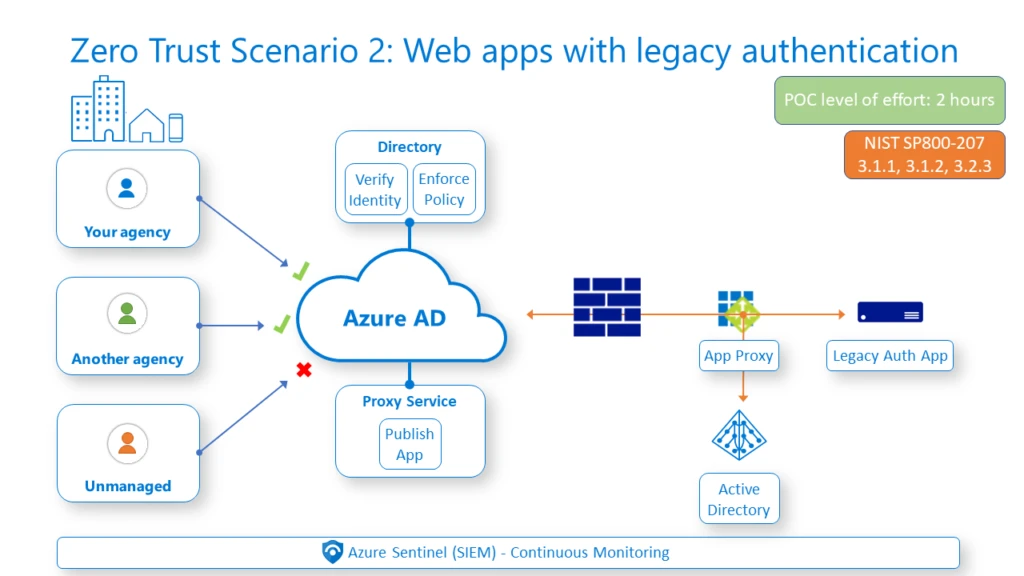
For hard-to-reach applications that can’t be easily rewritten for modern authentication, agencies can use Azure Active Directory’s Application Proxy. This architecture builds on the Azure AD foundation in scenario 1 to extend Zero Trust to legacy systems. Application Proxy also provides outbound-only connectivity and much more restrictive access than a VPN solution.
Scenario 3: Remote server administration
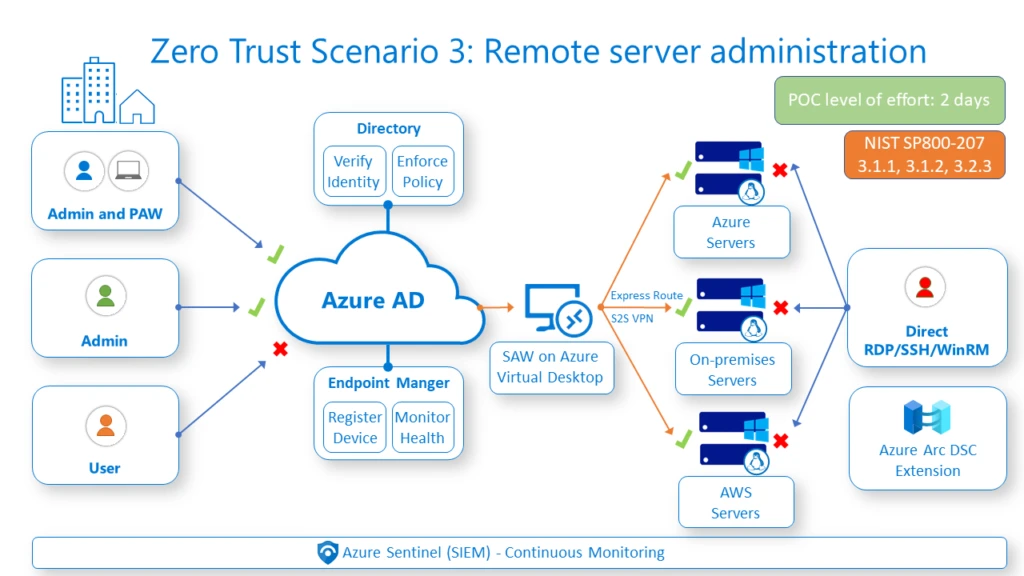
Remote server administration has become a popular threat vector as attackers utilize admin tools to move laterally across an environment and find new ways to compromise systems. The scenario 3 design pattern outlines how to simplify secure remote administration by layering the work done in scenario 1 with a strongly authenticated administrator account and privileged access workstation. This significantly reduces the attack surface area preventing unsanctioned server-to-server management by requiring modern authentication, MFA, and allow-listed admin devices for server administration via Azure AD conditional access policies. The result is a high level of assurance for multi-cloud and hybrid server administration.
Scenario 4: Segment cloud administration
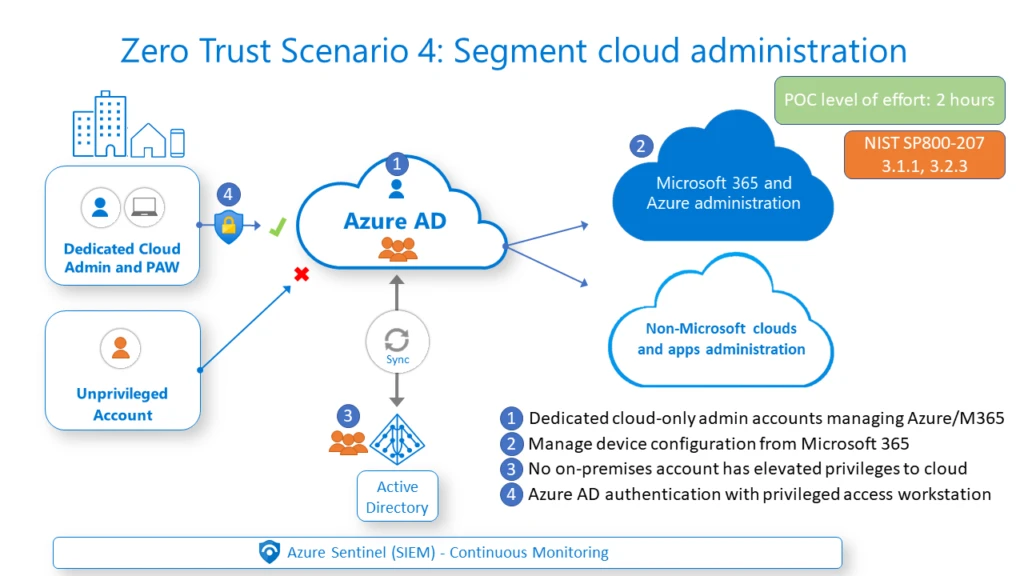
Recent attacks that used credentials compromised on-premises to attack the cloud underscore the need to ensure that no individual in an agency’s on-premises directory is privileged in the cloud. Building on scenario 1, this design pattern allows agencies to administer Microsoft and non-Microsoft workloads from isolated, dedicated, and segmented administrator accounts. Once this pattern is implemented, auditing controls should also be introduced to ensure that privilege segmentation remains in effect.
Scenario 5: Network micro-segmentation
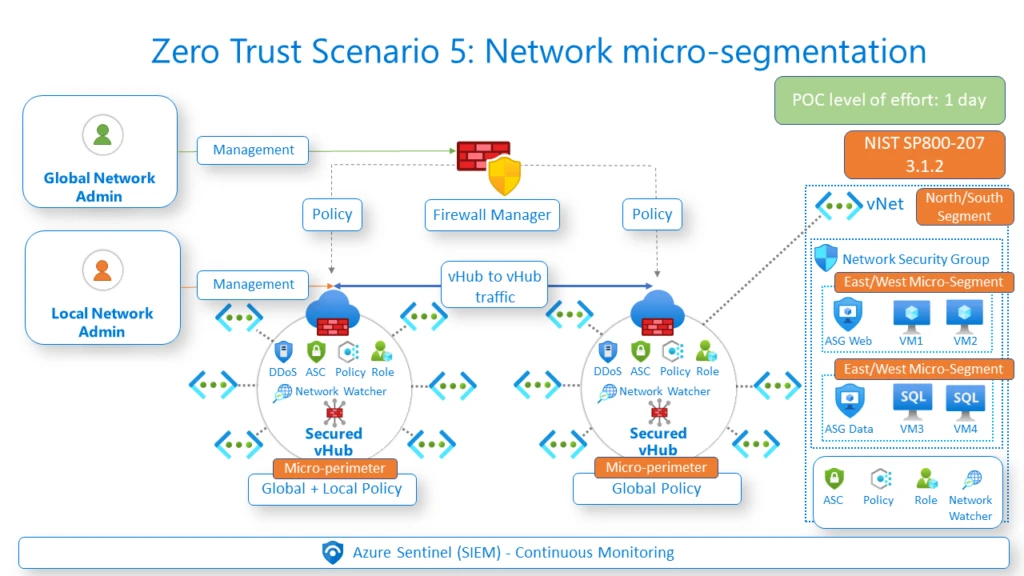
Agencies must establish multiple levels of segmentation to achieve both secure control and data planes. Azure native capabilities allow agencies to apply a consistent micro-segmentation strategy to protect against threats, implement defense in-depth, and achieve policy-enforced continuous monitoring at a granular level — including each perimeter, micro-perimeter, segment and microsegment.
Collaborating on continuous improvement
Microsoft’s deep understanding of the threat landscape, broad product capabilities, and vast experience helping our federal customers achieve their missions enables us to deliver a comprehensive approach to Zero Trust. Working in partnership, government and industry can come together to accelerate security modernization, meet short- and long-term EO requirements, and adopt a robust cyber posture that evolves with the complexity of modern government.




