Microsoft SEAL—powered by open-source homomorphic encryption technology—provides a set of encryption libraries that allow computations to be performed directly on encrypted data. This enables software engineers to build end-to-end encrypted data storage and computation services where the customer never needs to share their key with the service.
Microsoft SEAL is open source (MIT license). Start using it today!
Citing Microsoft SEAL (opens in new tab) | Contact us
Homomorphic Encryption
Homomorphic Encryption refers to a new type of encryption technology that allows computation to be directly on encrypted data, without requiring any decryption in the process. The first homomorphic encryption scheme was invented in 2009 and several improved schemes were created over the following years. There were a few notable and publicly available implementations, but their use required extensive understanding of the complicated mathematics underlying homomorphic encryption and were not easily usable by normal software developers.
Our goal was different: making homomorphic encryption easy to use and available for everyone. Today, Microsoft SEAL reaches this goal by providing a simple and convenient API with state-of-the-art performance. Microsoft SEAL comes with several detailed and thoroughly commented examples, demonstrating how the library can be used correctly and securely, and explaining any necessary background material.
Scenarios: Secure cloud storage and computation
In traditional cloud storage and computation solution customers need to trust the service provider to store and manage their data appropriately, e.g., not to share it with third parties without the customer’s consent. Microsoft SEAL replaces this trust with state-of-the-art cryptography, allowing cloud services to provide both encrypted storage and computation capabilities, while still guaranteeing that their customer’s data will never be exposed to anyone in unencrypted form.
Traditional cloud storage and computation
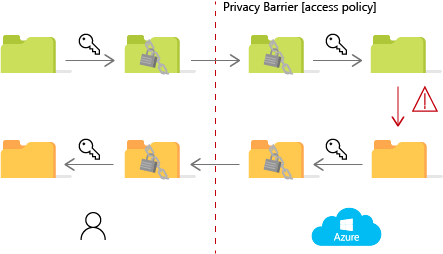
In traditional cloud storage and computation solutions the cloud need to have unencrypted access to customer data to compute on it, necessarily exposing the data to the cloud operators. Data privacy relies on access control policies implemented by the cloud and trusted by the customer.
Microsoft SEAL cloud storage and computation
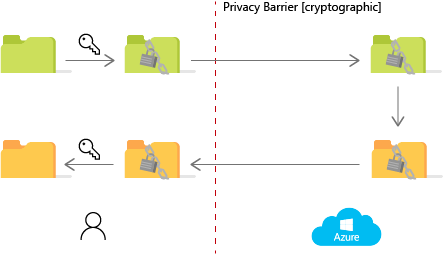
With Microsoft SEAL, the cloud operators will never have unencrypted access to the data they are storing and computing on. This is possible through homomorphic encryption technology, that allows computations to be performed directly on encrypted data. Data privacy relies on state-of-the-art cryptography (mathematics) and all information release will be controlled by the customer.

