Security and privacy are among the most significant concerns for enterprises and consumers using public cloud platforms. Azure Research – Security and Privacy is conducting pioneering research in the design of systems that guarantee strong security and privacy properties to cloud users, and in novel applications that are enabled by emerging security and privacy technology.
We work in close collaboration with external and internal research organizations, as well as with Microsoft product teams. Our current focus areas include secure distributed computing, privacy-preserving machine learning, secure hardware design, software security, and verified security and cryptography.
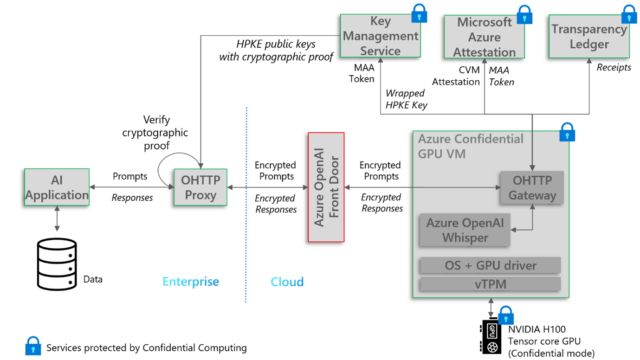
The team, which is in the Azure Office of the CTO, was formerly the Confidential Computing group in Microsoft Research’s Cambridge Lab. The team’s research and development has contributed directly to multiple Microsoft products, including Confidential Containers on Azure Container Instances (opens in new tab), Azure Confidential Ledger (opens in new tab) and Azure Managed Confidential Consortium (opens in new tab) Framework (which are based on CCF), Confidential Computing with GPUs (opens in new tab), Azure SQL-Always Encrypted (opens in new tab), and Control Flow Guard (opens in new tab) (which protects most of Microsoft’s systems and applications). The team also pioneered techniques for Memory Tagging, Malware Containment, and Confidential Data Cleanrooms, that have been adopted by several hardware and software products across the industry.




