
Microsoft launches Modern Log Management Program to help federal agencies accelerate Cyber EO compliance
 The Biden Administration released guidance in August 2021 requiring federal government customers to rapidly move towards standardized and comprehensive log event management to improve the ability to detect, investigate and remediate cyber threats. Known as M-21-31, the memorandum both sets forth a federal logging maturity model and provides a new standard that is broadly applicable across public sector and regulated industries.
The Biden Administration released guidance in August 2021 requiring federal government customers to rapidly move towards standardized and comprehensive log event management to improve the ability to detect, investigate and remediate cyber threats. Known as M-21-31, the memorandum both sets forth a federal logging maturity model and provides a new standard that is broadly applicable across public sector and regulated industries.
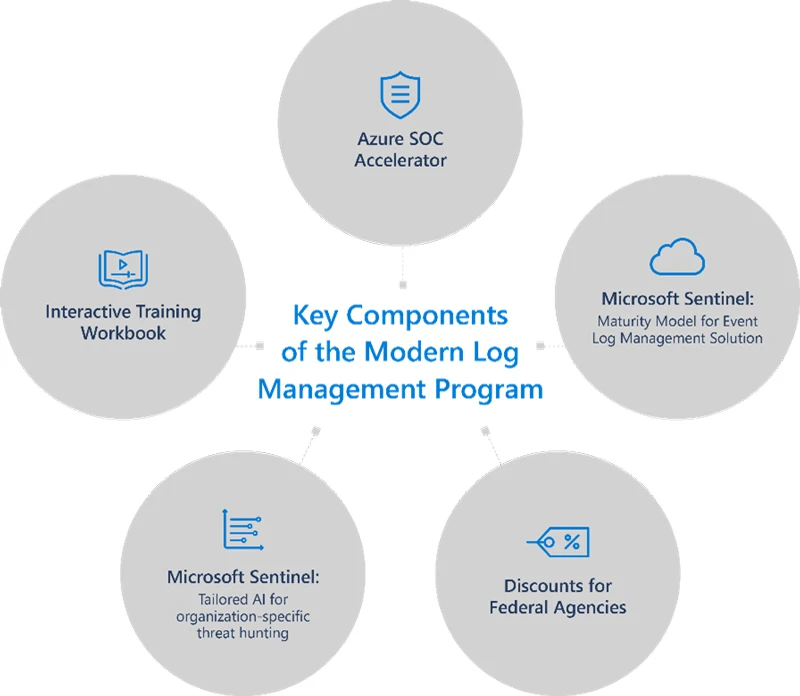
To help government agencies meet this requirement, Microsoft is launching Modern Log Management Program, a comprehensive solution that includes a Maturity Model for Event Log Management, Azure SOC Accelerator, custom cyber analytics, interactive training workbook and discounts for federal agencies.
Available at no cost and leveraging existing investments, the Modern Log Management Program delivers unprecedented visibility and remediation capabilities from a single pane of glass by pulling telemetry from over 50 Microsoft products. Agencies can now log more comprehensively across cloud providers and on-premises environments, resulting in the ability to operationalize data more effectively and realize greater investigation and response value.
Key components of the Modern Log Management Program
Microsoft Sentinel: Maturity Model for Event Log Management solution
The Maturity Model for Event Log Management solution is now available to help federal customers address complex requirements across the four Event Logging (EL) tiers defined in M-21-31.
Microsoft Sentinel’s AI-powered, cloud-native security information and event management (SIEM) capabilities provide a single pane of glass view for aggregating, managing and actioning data. It also allows agencies to seamlessly pivot between products to gain a more complete understanding of security and compliance posture. With one-click, customizable reporting, users can also gain more insights from log telemetry. Key components and benefits of the Sentinel solution include:
- Workbook: Provides actionable, continuous insights into log management posture and simple steps for remediation.
- Analytics Rules: Ensure compliance by tracking the agent, asset, data connector health and more to ensure log flow over time.
- Hunting Queries: Provide a proactive way to understand the logging environment relative to the four maturity levels outlined in M-21-31.
- Playbooks: Drive automated, consistent response, ensuring security teams can focus their time on what’s important.
Microsoft provides an array of more than 50 security capabilities that can address many of the monitoring needs in the EL0-3 requirements. From the basic Azure Activity logging that Microsoft includes in every Azure subscription, to more advanced workload monitoring and protection such as Defender for Cloud, Azure Monitor and User Entity Behavior Analytics, agencies can easily extend their monitoring coverage to fill in any existing gaps. One of the most crucial tools for investigations required by both the EO government-wide mandate for EDR and M-21-31 is Microsoft Defender for Endpoint. Defender for Endpoint was also approved by CISA for the Continuous Diagnostics and Mitigation (CDM) program, giving agencies additional procurement, deployment and integration options through DEFEND task orders.
Azure SOC Accelerator cloud-native logging
(Public Preview CY Q1)
M-21-31 establishes a framework for “ensuring centralized access and visibility for the highest-level enterprise security operations center (SOC) of each agency”, however getting all of the necessary components in place can be a daunting task. To jump-start native cloud logging enablement, Microsoft has created an Azure SOC Accelerator designed specifically to meet the requirements for CISA’s National Cyber Protection System (NCPS). The accelerator provides agencies a “one-click” solution to centralize security telemetry based on a fully-automated reference architecture. This accelerator is built on Microsoft Sentinel which is well-suited to meet M-21-31 log storage needs with cloud-native high performance and low-cost data storage tiers, dynamic and flexible caching and fully-automated capacity management. Microsoft Sentinel also provides built-in mechanisms for a subordinate SOC to give visibility to a higher-level SOC without the need for export or duplication of data which allows for faster response times and significant cost reduction.
Microsoft Sentinel: Tailored AI for organization-specific threat hunting
Beyond just basic log capture and archival, Microsoft Federal is currently working with several federal agencies to introduce new cyber AI capabilities uniquely designed for government customers. Utilizing the log data stored for M-21-31 compliance and the bring-your-own-ML capabilities of Microsoft Sentinel, agencies can further operationalize existing log data to realize additional value from archived logs by automatically tuning agency-specific threat hunting models. Sentinel’s bring-your-own ML provides familiar development environments, tools and programming languages to help agencies unlock insights faster by reducing the learning curve and development time of highly-tailored threat hunting analytics that can give organizations a distinct defensive advantage.
Interactive training workbook for empowering security analysts
Cybersecurity practitioners looking to learn Kusto Query Language (KQL), the core language used for intermediate and advanced investigations in Microsoft Defender and Sentinel, can now access Microsoft’s new interactive learning workbook. This interactive guide provides 100-200 level exercises and hands-on experience to help analysts of any skill level quickly increase their proficiency when executing real-world KQL queries.
Discounts for federal agencies
To help agencies accelerate log management modernization the Maturity Model for Event Log Management solution, Azure SOC Accelerator, and Interactive training workbooks are being made available to agencies as part of existing product offers. Microsoft is also offering discounts to agencies to help mitigate budget challenges from an increase in log source and log storage requirements required by M-21-31.
Working together to enhance investigation and remediation capabilities
Partnering with agencies to achieve great visibility while lowering the costs associated with meeting M-21-31 requirements is just one way Microsoft is dedicated to helping government raise its security baseline. Beyond the Modern Log Management Program, Microsoft continues to make significant investments to accelerate federal security modernization. Close collaboration with standards bodies such as National Institute of Standards and Technology on developing practical, interoperable approaches and participation in the Joint Cyber Defense Collaborative established by Cybersecurity & Infrastructure Security Agency (CISA) further underscores Microsoft’s deep commitment to promoting resilience and strengthening our nation’s cyber defenses.
Reach out to your dedicated Microsoft security specialist for assistance getting started with the Modern Log Management Program and visit the Cyber EO resource center to learn more.




