Microsoft Research India 2025 Highlights
Here are some highlights of the research and impact at Microsoft Research India in 2025, along with some glimpses of the lab milieu.
Research Intern – Security, Privacy and AI
This Research Internship will include (1) conducting threat modeling for Large Language Model (LLM)‑enabled agentic designs and identifying practical mitigations for Windows OS; (2) developing or refining formal security frameworks that support scalable designs and…
Member of Technical Staff, AI Safety Post-Training – MAI Super Intelligence Team
As a Member of Technical Staff, AI Safety Post-Training, you will work to develop and implement cutting-edge safety methodologies for post-training large language models with agentic and reasoning capabilities that are served to millions of…
Publicly-verifiable elections
Microsoft’s free, open-source ElectionGuard tools enable voters to verify their votes were accurately counted without compromising privacy or trusting election equipment or personnel. New research eliminates the need for cryptographic keys, making the process far…
Reducing Privacy leaks in AI: Two approaches to contextual integrity
New research explores two ways to give AI agents stronger privacy safeguards grounded in contextual integrity. One adds lightweight, inference-time checks; the other builds contextual awareness directly into models through reasoning and RL.
CHERI-Lite for Memory Safety Exploit Mitigation
Designing safe digital systems for the humanitarian sector
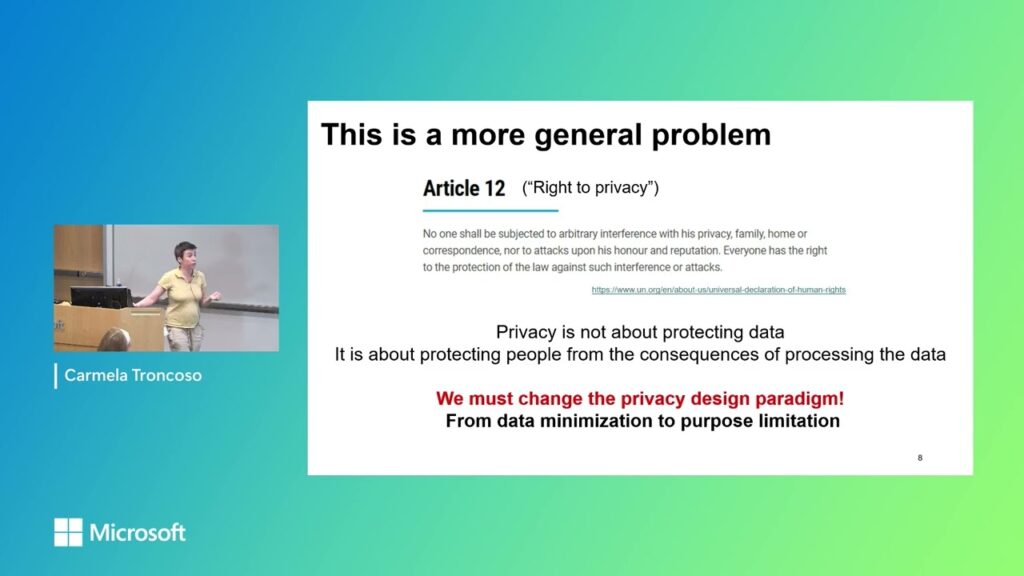
Speaker: Carmela Troncoso Host: Betül Durak In this talk we overview our collaboration with the International Committee of the Red Cross, in which we help them to digitalize their aid distribution process without increasing risks…